StreamSpy Trojan
Protecting personal and workplace devices from modern malware is more critical than ever, as today's threats are designed not only to steal information but also to silently extend an attacker's reach deep into a compromised system. One of the latest examples is StreamSpy, a multi-stage Trojan linked to the Patchwork (APT-Q-36) group. Its modular design, stealthy communication methods, and broad feature set make it a serious security concern.
Table of Contents
A Sneaky Backdoor With Advanced Communication Channels
StreamSpy stands out because it uses both WebSocket and HTTP to communicate with its command server. WebSocket channels carry instructions and transmit results back to the attacker in near real time, while HTTP handles larger data transfers such as uploaded or downloaded files. This is similar to the behavior seen in the Spyder downloader, suggesting shared development techniques or an evolution of existing tools.
Before carrying out any malicious actions, the Trojan unlocks a set of embedded configuration values. These settings guide its communication behavior, provide identity parameters, and define the persistence methods it will use to survive system reboots.
System Profiling and Victim Identification
Once active, StreamSpy performs a deep scan of the infected system. It gathers host metadata such as the device name, current user, operating system version, installed antivirus tools, hardware identifiers, and other environment details. From this information, it constructs a unique victim ID and sends it to the attacker's server, allowing the operators to track individual infections inside their campaign.
To guarantee that it launches automatically, the Trojan plants persistence mechanisms using scheduled tasks, registry run keys, or startup shortcuts.
A Wide Range of Remote Commands
StreamSpy supports an extensive command set that allows attackers to interact with an infected environment in flexible and highly invasive ways. Among its most damaging features are:
- Execution and Deployment Capabilities
- Running arbitrary commands with cmd.exe or PowerShell, granting full control of system functions
- Downloading and launching additional payloads, including encrypted ZIP archives that it decrypts and deploys locally
- File Operations and Device Enumeration
- Uploading or exfiltrating files to or from the compromised machine
- Renaming or deleting files to hide activity or prepare follow-up stages
- Inspecting all connected storage devices, including capacity, file system, and removable-drive attributes
These features make StreamSpy an effective tool for espionage, lateral movement, data theft, and long-term access.
Delivery Through a Deceptive ZIP Archive
Investigators have confirmed that StreamSpy is spread through malicious ZIP archives. One known case involved a file named 'OPS-VII-SIR.zip' hosted on an external server. The archive contained:
- The StreamSpy executable disguised with a PDF-style icon
- Legitimate PDF lure documents added to make the archive look harmless
This technique relies on social engineering. A user opens the archive, sees documents that look legitimate, and unknowingly launches the disguised malware. The initial lure file could be delivered through many channels, including fraudulent websites, fake emails, malicious ads, direct messages, or social media posts.
A Serious Threat That Requires Immediate Removal
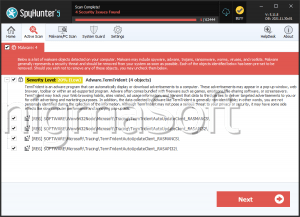
With its wide-ranging capabilities, StreamSpy provides attackers the ability to siphon sensitive data, deploy further malware, interfere with files, and potentially hijack accounts or identities. Its presence on a device exposes victims to significant risks, including financial loss and further compromise. If detected, it should be removed immediately using reputable security tools and thorough system cleanup procedures.
Staying alert to suspicious files, unexpected ZIP archives, and unsolicited communications is essential. As threats like StreamSpy grow increasingly convincing, strong user awareness remains one of the most effective defenses.