StartJoy Ads
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
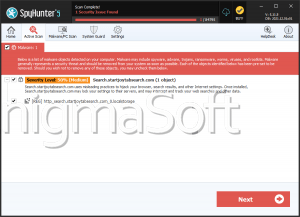
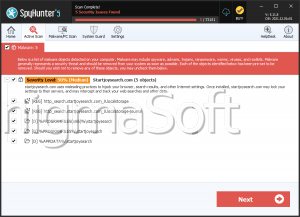
| Threat Level: | 80 % (High) |
| Infected Computers: | 29 |
| First Seen: | May 12, 2016 |
| Last Seen: | March 4, 2026 |
| OS(es) Affected: | Windows |
The StartJoy browser extension is promoted at Startjoy.com as the perfect tool that can allow you to turn your Web browser into 'social & media center.' The StartJoy browser extension may arrive on your PC under the name StartJoy New Tab and may be accompanied by applications like NetCoupon and WinFix Pro. Security investigators reveal that the StartJoy New Tab software is created by the infamous Imali Media Ltd. and shares many similarities with the TvNewTab and the Social Media NewTab adware. It appears that Imali Media Ltd. decided to combine two of their products into one and save on server maintenance and pay-per-install distribution. The StartJoy adware might change your homepage and search aggregator to Search.StartJoy.com and gain access to bookmarks and installed themes and record your Internet history.
The new tab by StartJoy may include to-do lists and links to Facebook, Classmates, Vkontakte and MySpace. Security investigators alert that the StartJoy New Tab adware may bring up a dialog box on your screen and ask to post advertisements via your social media profile on your behalf. The StartJoy New Tab adware may use JavaScript to add panels to your browser interface and load ads on the left and right side of your screen. The ads by StartJoy may include links to products on Amazon, Best Buy and Aliexpress. Users shouldn't buy items that are associated with the StartJoy New Tab adware to avoid being involved in a financial hoax. The search engine at Search.StartJoy.com may feature links to Virustotal.com and Speedtest.net, but the StartJoy adware is not recognized as a legitimate application. The StartJoy adware may compromise the security of Web browsers that run on the Gecko, WebKit and Trident rendering engines. You should not tolerate the activity of the StartJoy adware and reclaim your browser by using a reliable anti-spyware instrument.
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Vemptik.B |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
ab3d39395da4779a612dafe0e22378a5
SHA1:
bf1d8124debae4e45296e47e61396c2b1274c474
SHA256:
63F2B887C11667D57055FE8EEA5ACD2C4CC78787CEA5F1EC896653A1EDA95379
File Size:
1.34 MB, 1344544 bytes
|
|
MD5:
181d6f37e43e1ff4a0e94031ab084bb3
SHA1:
49aa4717e77333497fc12d3bce4ab069509c204d
SHA256:
5E5C498186018344487D28F3CF087FAAFE4ACEC5FC70C1B576A3B8AECFD23804
File Size:
39.77 KB, 39773 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Корпорация Галактика |
| File Description | Ядро 3-х уровневого Атлантис-приложения (клиентская часть) |
| File Version |
|
| Internal Name |
|
| Legal Copyright | (c) АО 'Корпорация Галактика' 2001-2021 |
| Product Name |
|
| Product Version |
|
File Traits
- 2+ executable sections
- dll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 136 |
|---|---|
| Potentially Malicious Blocks: | 4 |
| Whitelisted Blocks: | 110 |
| Unknown Blocks: | 22 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\bf1d8124debae4e45296e47e61396c2b1274c474_0001344544.,LiQMAxHB
|