Startgo123.com
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 7,567 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 9,301 |
| First Seen: | June 29, 2016 |
| Last Seen: | September 7, 2023 |
| OS(es) Affected: | Windows |
Web surfers that use Google Chrome and Opera may be familiar with the Speed Dial functionality of both browsers that allows users to open bookmarked pages and visited sites with one click. The design of Startgo123.com is tailored to resemble the Speed Dial of Opera and Google Chrome and fool users into thinking that their browser is working properly. In reality, the Startgo123.com site is associated with a browser hijacker that may be used to collect search terms, redirect users to a custom version of Google and claim pay-per-click revenue. If you load Startgo123.com in your browser, then you might be infected with a browser hijacker. Computer users may install browser hijacking software via freeware bundles by choosing the 'Express' or 'Typical' option during the installation procedure. The Startgo123.com browser hijacker may travel with programs like SupTab and ProShopper. Security experts note that the links on Startgo123.com to social media services like Twitter and Facebook may lead to phishing pages.
The Startgo123.com browser hijacker may use tracking cookies and record your recently visited pages to show recommended offers from merchants. As stated before, the Startgo123.com browser hijacker may redirect users to a custom build of Google and users may not be protected with HTTPS encryption. Moreover, the results provided by Startgo123.com may not have been filtered by Google Safe Browsing, and you may load insecure pages. The Startgo123.com browser hijacker may edit your DNS settings and obstruct your access to third-party engines like Bing, Yahoo and DuckDuckGo. Also, the Startgo123.com browser hijacker might track what purchases you make on Amazon to show related advertisements via pop-up and pop-under windows. Browser hijacking software is a family of programs that are not classified as harmful but may limit your Internet accessibility and slow down your PC. You should not tolerate the browser hijacker linked to Startgo123.com and use a reliable anti-malware tool to remove it.
Table of Contents
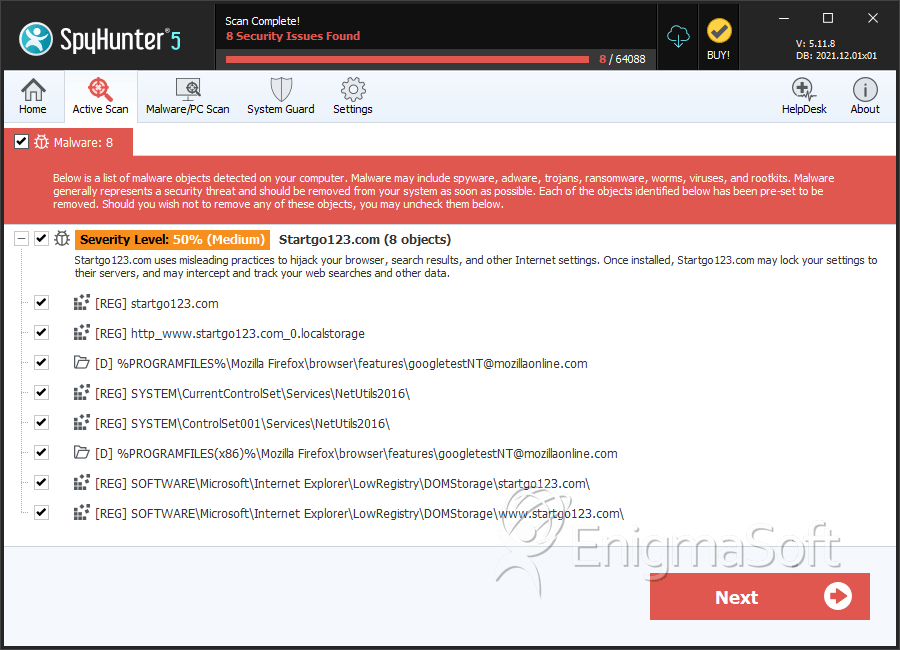
SpyHunter Detects & Remove Startgo123.com
Registry Details
Directories
Startgo123.com may create the following directory or directories:
| %PROGRAMFILES%\Mozilla Firefox\browser\features\googletestNT@mozillaonline.com |
| %PROGRAMFILES(x86)%\Mozilla Firefox\browser\features\googletestNT@mozillaonline.com |
URLs
Startgo123.com may call the following URLs:
| startgo123.com |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.