Startfenster
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 935 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 3,358 |
| First Seen: | April 12, 2013 |
| Last Seen: | September 25, 2023 |
| OS(es) Affected: | Windows |
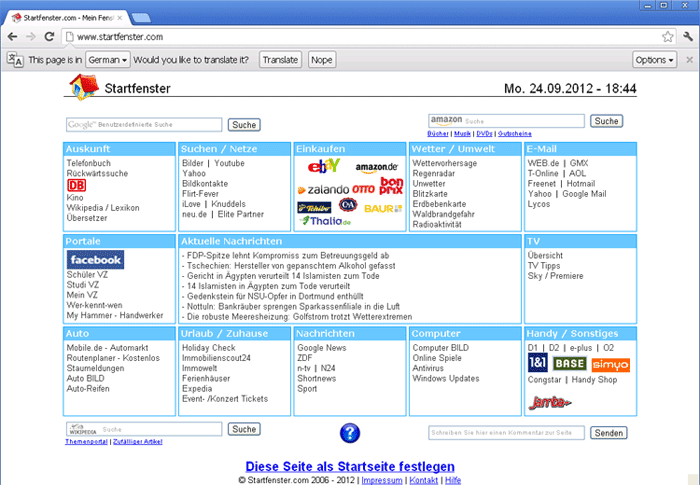
Startfenster likely falls into the category of applications characterized by having browser hijacker capabilities. These applications are designed with the express purpose of taking over users' Web browser. To be more precise, the intrusive applications often target the homepage, new tab page, and default search engine settings and change them to now open a promoted Web address. In the case of Startfenster, affected users may notice frequent redirects to the unfamiliar page http://www.startfenster.de or a similar one.
In the vast majority of cases, browser hijackers also are classified as PUPs (Potentially Unwanted Programs) due to the questionable methods involved in their distribution. After all, the operators of these applications realize that users are extremely unlikely to install them intentionally. That is why PUPs are often included as part of software bundles or even spread via entirely fake installers/updates.
Once such an application has been fully deployed on the user's computer or device, it also may activate additional intrusive functionalities. For example, PUPs are infamous for spying on users' browser activities. The applications may collect browsing and search histories, clicked URLs, IP addresses, geolocation and more. All of the harvested data is likely to be exfiltrated to a remote server under the control of the PUP's operators.
URLs
Startfenster may call the following URLs:
| https://www.startfenster.de/?q= |