Ssimpotashka@gmail.com Ransomware
Ssimpotashka@gmail.com Ransomware Image
The Ssimpotashka@gmail.com Ransomware is an encryption ransomware Trojan that is part of the Scarab family of ransomware. Scarab is a ransomware family that has been part of a RaaS (Ransomware as a Service) platform and a builder kit, which has allowed criminals to release numerous new versions in this family of threats between April and June 2018. The Ssimpotashka@gmail.com Ransomware is just one of the latest versions of this threat to have been released. The Ssimpotashka@gmail.com Ransomware is designed to make the victim's files inaccessible, encrypting them by using an efficacious encryption algorithm and then demanding a ransom payment from the victim. The Ssimpotashka@gmail.com Ransomware spread advertisements through spam email attachments and typical threat delivery avenues commonly, such as unsafe advertising and fake software downloads.
Table of Contents
How the Ssimpotashka@gmail.com Ransomware Attack Works
the Ssimpotashka@gmail.com Ransomware is designed to use AES 256 encryption to make the victim's files inaccessible. the Ssimpotashka@gmail.com Ransomware targets user generated files, which may include a variety of media files, databases, configuration files, and numerous types of documents. There are some files types that may be targeted by threats like the Ssimpotashka@gmail.com Ransomware, which include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
There is very little to differentiate the Ssimpotashka@gmail.com Ransomware from the many other encryption ransomware Trojans currently active. The Ssimpotashka@gmail.com Ransomware will rename affected files in its attack by adding the file extension '.ssimpotashka@gmail.com' to each encrypted files.
The Ssimpotashka@gmail.com Ransomware’s Ransom Note
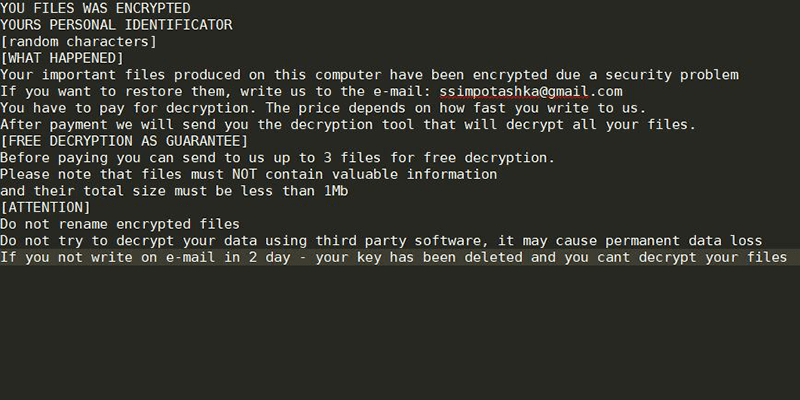
Once the Ssimpotashka@gmail.com Ransomware has encrypted the victim's files, the Ssimpotashka@gmail.com Ransomware will deliver a ransom note. the Ssimpotashka@gmail.com Ransomware's ransom note takes the form of a text file named 'HOW TO RECOVER ENCRYPTED FILES.TXT' which contains the following text:
'YOU FILES WAS ENCRYPTED
YOURS PERSONAL IDENTIFICATOR
[random characters]
[WHAT HAPPENED]
Your important files produced on this computer have been encrypted due a security problem
If you want to restore them, write us to the e-mail: ssimpotashka@gmail.com
You have to pay for decryption. The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.
[FREE DECRYPTION AS GUARANTEE]
Before paying you can send to us up to 3 files for free decryption.
Please note that files must NOT contain valuable information
and their total size must be less than 1Mb
[ATTENTION]
Do not rename encrypted files
Do not try to decrypt your data using third party software, it may cause permanent data loss
If you not write on e-mail in 2 day - your key has been deleted and you cant decrypt your files.'
Computer users should hold back from following the instructions in the Ssimpotashka@gmail.com Ransomware's ransom note or paying the Ssimpotashka@gmail.com Ransomware ransom.
Protecting Your Data from Threats Like the Ssimpotashka@gmail.com Ransomware
The best protection against threats like the Ssimpotashka@gmail.com Ransomware is to have file backups stored in a location away from the reach of ransomware Trojans like the Ssimpotashka@gmail.com Ransomware. Having these backups on the cloud or an external memory device can provide good protection. Apart from file backups, PC security researchers advise computer users to use a constant security product that is fully up to date and take precautions when handling any potentially dangerous content such as spam email attachments or suspicious online advertisements.

