Srcingan.com
Information security researchers have identified that srcingan.com is a deceptive search engine promoted through a browser hijacker. This particular intrusive application is recognized as Anime Nook. Browser hijackers typically promote fake search engines by altering the settings of compromised browsers. Users often inadvertently install such applications without realizing that they will hijack their browsers.
Table of Contents
Srcingan.com May Take Users to Unsafe or Dubious Websites
Once installed, Anime Nook configures srcingan.com as the default search engine, homepage, and new tab page within Web browsers. Consequently, users are directed to srcingan.com whenever they open a browser or initiate a new tab to conduct searches. However, srcingan.com is categorized as a fraudulent search engine because it fails to produce genuine search results. Instead, our investigation revealed that srcingan.com redirects users to bing.com.
Bing.com is a reputable and reliable search engine. Nonetheless, the presence of browser hijackers and deceptive search engines like srcingan.com can introduce certain risks. Browser hijackers are often engineered to collect various browsing-related data, including search queries, IP addresses, geolocation details and more.
The developers behind browser hijackers may misuse the gathered data, which could lead to online privacy concerns. Furthermore, unreliable search engines, such as srcingan.com might be designed to display misleading results, present deceptive advertisements, and steer users towards untrustworthy websites. Therefore, it is advisable to remove both srcingan.com and Anime Nook from affected browsers.
It is crucial to acknowledge that removing browser hijackers can be challenging. Therefore, it is recommended to utilize reputable security tools and adhere to comprehensive removal instructions to eradicate browser hijackers from your system effectively.
Browser Hijackers and PUPs (Potentially Unwanted Programs) Rely Heavily on Shady Distribution Tactics
PUPs and Browser Hijackers are notorious for utilizing shady distribution tactics to infiltrate and install themselves on users' systems. These tactics are often deceptive and exploit users' lack of awareness or caution during software installations.
- Software Bundling: One of the most common methods used by PUPs and browser hijackers is software bundling. They are often bundled with legitimate free software that users download from the Internet. During the installation process of the desired software, users may overlook or hastily agree to additional offers or terms, inadvertently installing the PUP or browser hijacker along with the intended software.
- Misleading Installation Prompts: PUPs and Browser Hijackers employ misleading installation prompts to trick users into accepting their installation. For example, they may use confusing wording on buttons like 'Next' or 'Accept' during installation, where clicking these buttons actually agrees to install the unwanted software. Users who rush through installation processes without carefully reviewing each step are particularly vulnerable to this tactic.
- Fake Updates and Downloads: Another tactic involves presenting users with fake update alerts or download prompts. Users may encounter pop-up messages or banners claiming that their software or browser needs an urgent update or that a particular download is required to access certain content. Clicking on these prompts can lead to the download and installation of PUPs or Browser Hijackers instead of legitimate updates or content.
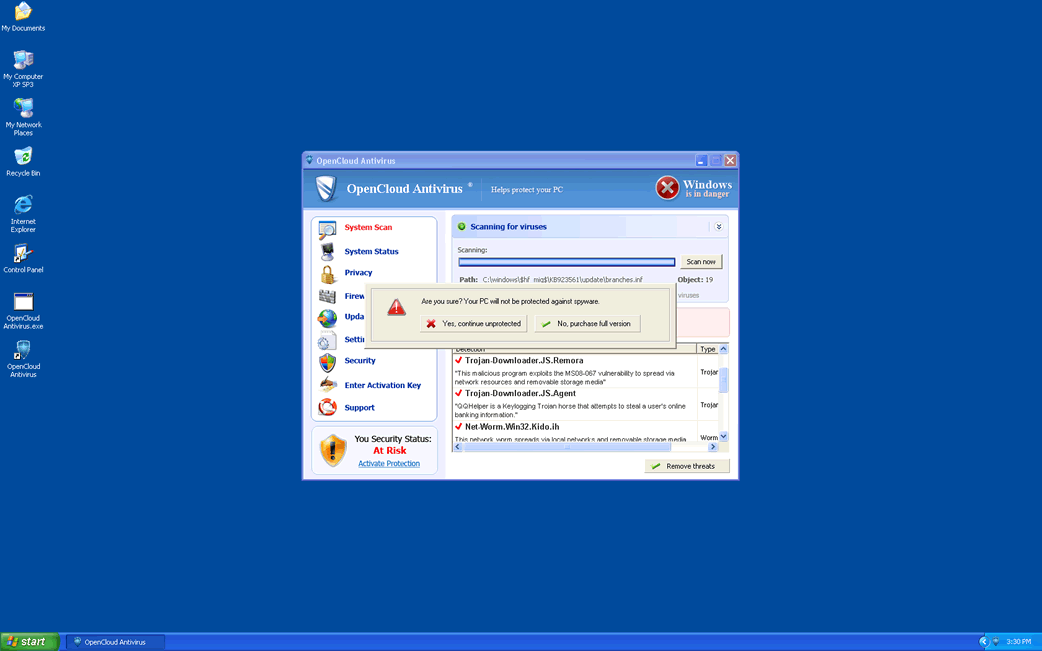
- Aggressive Advertising: PUPs and Browser Hijackers often employ aggressive and misleading advertising techniques. They may display intrusive pop-up advertisements or fake system alerts warning users about non-existent issues with their computers, such as virus infections or outdated software. Users are then encouraged to click on these advertisements or alerts, which can lead to the unintended installation of unwanted programs.
- Disguised as Legitimate Software: Some PUPs and browser hijackers disguise themselves as useful or legitimate software to deceive users. They may mimic popular browser extensions, security tools or optimization utilities, leading users to believe they are downloading a beneficial program. Once installed, these programs reveal their true harmful intent by altering browser settings, displaying unwanted advertisements or collecting user data.
These shady distribution tactics are designed to maximize the spread and installation of PUPs and browser hijackers while minimizing user resistance or detection. To be protected against these threats, users should exercise caution when downloading software, always opt for custom or advanced installation settings to review bundled offers, keep their software and browsers up-to-date, and use dedicated anti-malware software to detect and remove unwanted programs.
URLs
Srcingan.com may call the following URLs:
| srcingan.com |