Spectre Ransomware
PC security researchers have been tracking the Spectre Ransomware for some time. This ransomware Trojan was observed in testing mode approximately on June 9th but was released in a full version a few days later. It seems that the Spectre Ransomware is a sophisticated ransomware Trojan and that considerable time and resources have been extended in creating this threat. Because of this, PC security researchers consider it possible that the Spectre Ransomware and its variants may become an important threat to computer users.
Table of Contents
The Specter of a Spectre Haunting Your Files
The Spectre Ransomware carries out a typical encryption ransomware Trojan attack, which involves encrypting the victims' files and then requesting a ransom. The Spectre Ransomware was first observed in a testing mode, where it connected to its Command and Control server to relay information about the infected computer and receive information about the attack to be carried out on the victim's PC. As part of its attack, the Spectre Ransomware will first delete the Shadow Volume Copies of the files on the infected computer. The Spectre Ransomware then will scan the infected computer for certain file types to carry out its attack. In its testing version, the Spectre Ransomware would encrypt the files with the following extensions:
.txt, .doc, .docx, .pdf, .rtf, .xls, .xlsx, .ppt, .pptx, .bmp, .jpg, .jpeg, .gif, .tiff, .png, .wav, .mpeg, .avi, .zip, .rar, .wmv.
In its full version, the Spectre Ransomware encrypts a higher number of file types. The Spectre Ransomware uses a combination of the AES and RSA encryptions to make the files inaccessible once they have been encrypted. The Spectre Ransomware will add the file extension '.spectre' to each affected file's name and then replace the file's name with random characters. It seems that the Spectre Ransomware uses the Base64 to scramble the files' names, although it does not seem to fit with this model exactly. After encrypting the victim's files, the Spectre Ransomware will deliver the following message to the victim:
'IMPORTANT INFORMATION!
All your files are encrypted by encryption algorithm AES-256, you can't decrypt your files without a key.
If you want to decrypt your files you should pay 200$.
To decrypt your files go to http://a0142503.xsph.ru/login.php your ID:
After encrypting the victim's files, the Spectre Ransomware will display a ransom note in the form of a text file named 'HowToDecryptIMPORTANT!.txt' on the victim's computer. This file is placed on the infected computer's desktop and in each directory where the Spectre Ransomware encrypted data. The Spectre Ransomware ransom note contains the victim's identifier, as well as a link to the payment website associated with the Spectre Ransomware attack
Should You Pay the Spectre Ransomware Ransom
One aspect of the Spectre Ransomware that points to this being a more sophisticated attack than the average ransomware Trojan is that the people responsible for the Spectre Ransomware have created a website dedicated to collecting victims' ransoms specifically. This website was hosted on the Web in the testing version and may have a TOR counterpart for the full version of the Spectre Ransomware. When the victim visits the Spectre Ransomware's payment website, there is a login screen where they need to enter an identifier included in the Spectre Ransomware's ransom note. After logging in, the Spectre Ransomware payment website includes pages for support, frequently asked questions, and decrypting the affected files.
Dealing with the Spectre Ransomware
Computer users should refrain from paying the Spectre Ransomware ransom or contacting the people responsible for the Spectre Ransomware attack. Instead, they should protect their files by having backup copies on the cloud or a portable memory device. Apart from backup copies, a reliable security program is capable of helping computer users intercept threats like the Spectre Ransomware before their files become compromised. The Spectre Ransomware poses a significant threat to the computer users' data and precautions against the Spectre Ransomware, and similar ransomware threats should be put in motion.
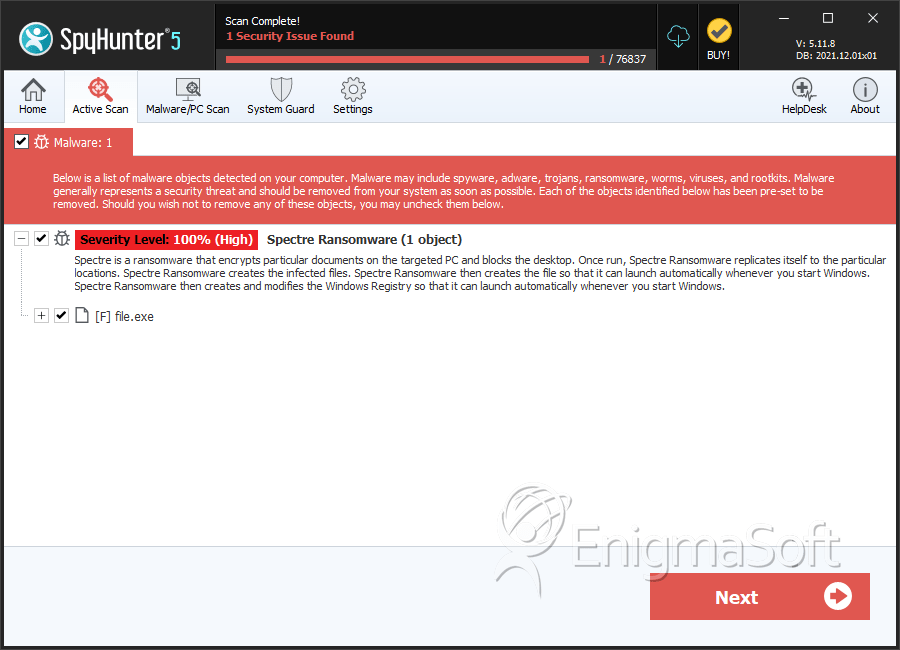
SpyHunter Detects & Remove Spectre Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | e8af7ef13b6ced37d08dce0f747d7d8b | 0 |

