SNSLocker Ransomware
The SNSLocker Ransomware is an encryption ransomware Trojan. Like other similar threats, the SNSLocker Ransomware encrypts the victim's files using an AES-256 encryption algorithm. If the victim wants to recover the information, it may be necessary to pay a $300 USD ransom via BitCoin. Various functions in the SNSLocker Ransomware threat do not work correctly and require various components to display its graphic interface. PC security analysts warn computer users against the SNSLocker Ransomware and advise the use of a reliable security program and the avoidance of unsolicited email attachments, file sharing networks, and other risks associated with these threats.
Table of Contents
How the SNSLocker Ransomware may Attack a Computer
The SNSLocker Ransomware establishes a connection with its Command and Control server, sending information about the configuration of each infected computer. The SNSLocker Ransomware receives a 32-character alphanumeric password that will be used to encrypt the victim's files. Through its connection, the SNSLocker Ransomware will send information such as the user name, the machine's name, its public IP address, its MAC address, and the system date and time. After the SNSLocker Ransomware has received its encryption data, the SNSLocker Ransomware will target the following types of files for encryption:
.1pa, .3dm, .3g2, .3gp, .aaf, .accdb, .aep, .aepx, .aet, .ai, .ai, .aif, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bik, .bmp , .c, .cal, .cdr, .cdt, .cdx, .cgn, .class, .clk, .cmx, .cnt, .cpp, .cpt, .cpx, .cs, .csl, .csv, .cur, .dat, .db, .dbf, .des, .des, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .drw, .ds4, .dsf, .dwg, .dwg, .dxf, .efx, .eps, .eps, .fim, .fla, .flv, .fmv, .fpx, .fpx, .fx0, .fx1, .fxr, .gem, .gif, .gif, .h, .idml, .iff, .iif , .img, .indb, .indd, .indl, .indt, .ini, .inx, .iso, .jar, .java, .jpeg, .jpg", .js, .lgb, .m3u, .m3u8, .m4u, .mac, .max, .mdb, .met, .mid, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .mx0, .nap, .nd, .pat, .pcd, .pct, .pcx, .pdb, .pdf, .pfb, .php, .pic, .plb, .plt, .pmd, .png, .pot, .potm, .potx, .pp4, .pp5, .ppam, .ppf, .ppj, .pps, .ppsm, .ppsx, .ppt, .ppt, .pptm, .pptx, .prel, .prn, .prn, .prproj, .ps, .ps, .ps, .psd, .psp, .ptb, .py, .qba, .qbb, .qbi, .qbm, .qbo, .qbp, .qbr , .qbw, .qbx, .qby , .qpd, .qsm, .qss, .qst, .qwc, .ra, .rar .raw, .raw, .rb, .rif, .rtf, .rtp, .sct, .sdf, .ses, .set, .shw, .sldm, .sldx, .sql, .svg, .svg, .swf, .swf, .tga, .tif, .tiff, .tlg, .tlg, .ttf, .txt, .txt, .txt, .v30, .vcf, .vob, .vsd, .vsd, .wav, .wav, .webm, .wi, .wk3, .wk4, .wma, .wmf, .wmv, .wpd, .wpd, .wpg, .wps, .xcf, .xla, .xlam, .xll, .xlm, .xls, .xls, .xlsb, .xlsm, .xlsm, .xlsx, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xpm, .xqx, .xqx, .zip.
After encrypting the victim's files, the SNSLocker Ransomware changes the affected files' extensions by adding the extension '.RSNSlocked' to the end of each file name. The SNSLocker Ransomware stores the decryption key on its Command and Control server. This key, which is encrypted to prevent computer users from accessing it is only provided if the victim pays a ransom. After carrying out the encryption, the SNSLocker Ransomware changes the affected computer's Desktop image, delivering an image that is currently stored on the Imgur image hosting service. This image contains information about how to pay the SNSLocker Ransomware ransom. Currently, this image is copyrighted to Saad Nabil Soufyane, author of this encryption ransomware Trojan.
Some Considerations About the SNSLocker Ransomware Payment
Every time the SNSLocker Ransomware encrypts a computer's files, it creates an identifying number that is used to identify each infected computer. The SNSLocker Ransomware allows the victim to consult a website containing information about how to pay in BitCoin, and how to carry out payment. Malware analysts strongly advise against paying these ransom amounts. Paying it only enables con artists to continue carrying out their attacks. Instead, computer users should ensure that they have backed up their files regularly. This way, instead of paying the SNSLocker Ransomware ransom (with no guarantee that these people will deliver the decryption key), computer users can remove the SNSLocker Ransomware infection and recover the encrypted files from the backup location.
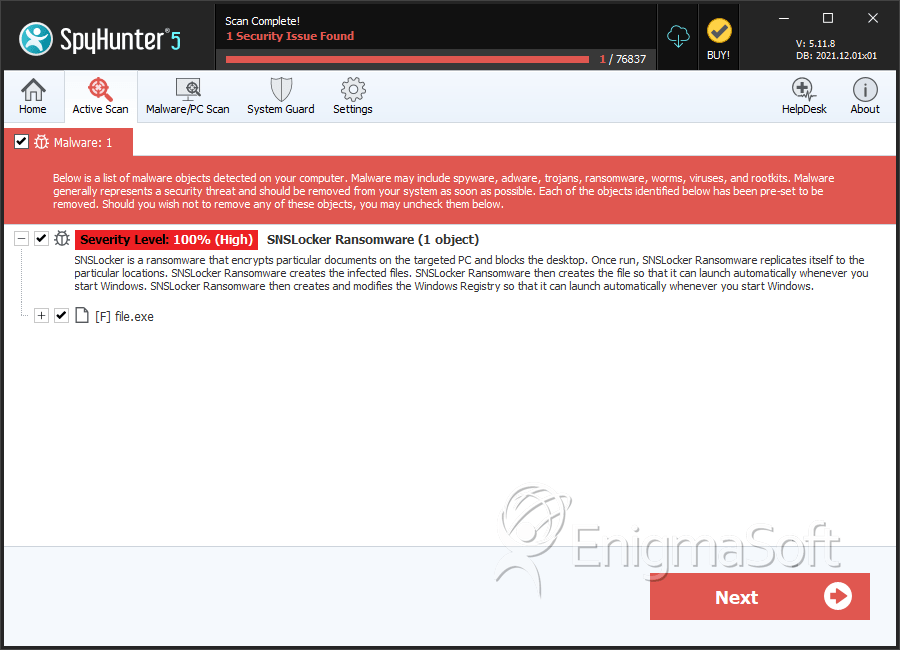
SpyHunter Detects & Remove SNSLocker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c3cd8168f96e89998cab52b436c24b7d | 0 |

