Skeleton Key Malware
It is probably time to start implementing strong security measures on corporate networks, particularly two-factor authentication, which is a trusted, well-known way of preventing intrusions. One contributing factor is the appearance of the Skeleton Key malware, which allows third parties to gain unprecedented access to a corporate network. The Skeleton Key malware may circumvent authentication on Active Directory systems, which are commonly used to protect important corporate networks and other sensitive content. The recent discovery of the Skeleton Key malware should prompt computer users and companies to protect their networks using two-factor authentication and other security measures.
Table of Contents
The Skeleton Key malware Provides Access to Third Parties
The Skeleton Key malware is used to bypass Active Directory systems that implement a single authentication factor, that is, computers that rely on a password for security. Using the Skeleton Key malware, third parties may gain access to a network by using any password, bypassing authentication altogether. The Skeleton Key malware was first uncovered being used on a corporate network that used passwords to gain access to VPN services and email. The Skeleton Key malware is deployed as an in-memory patch on the Active Directory domain controller, which allows third parties to gain full access to remote access services, while legitimate computer users continued to use the affected network without knowing there was a problem at all. The Skeleton Key malware is especially threatening in that the Skeleton Key malware allows anyone with physical access to the login systems to authenticate users on the affected network. This means that an attack may pose as any user without alerting others or restricting legitimate users from accessing the network. The Skeleton Key malware gives third parties an unprecedented level of stealth, a key factor in carrying out any type of threat attack effectively.
Why the Skeleton Key malware Poses a Specific Risk to Corporate Networks
At first glance, the above description doesn't make it seem as if the Skeleton Key malware poses a huge threat since the Skeleton Key malware doesn't sound like the most sophisticated kind of attack. However, the fact that the Skeleton Key malware gives anyone access to information on a corporate network is extremely threatening to a company. Today, it may be the most lucrative online illicit deal using sensitive information. While attacks that target personal computers with adware or that try to collect banking information are threatening, threats designed to target corporations and engage in industrial espionage operate on an entirely different level. Using the Skeleton Key malware, any disgruntled employee could pose as a high-level user or chief of the company to access data associated with all employees, customers or sensitive information. All it would take would be a bribe and providing the employee with the Skeleton Key malware to collect all types of data. As evidenced by the high-profile attacks on Sony Pictures, these types of attacks may be devastating for any company. The fact that the Skeleton Key malware can hide its tracks makes the Skeleton Key malware substantially more threatening, as well.
Weakenesses and Characteristics of the Skeleton Key malware
Fortunately, the Skeleton Key malware has many weaknesses as the Skeleton Key malware is currently implemented. The Skeleton Key malware needs to be redeployed each time the domain controller starts. The Skeleton Key malware can only attack 64-bit Windows versions. To bypass the first weakness, the Skeleton Key malware may be associated with a remote access Trojan installed on the victim's network to redeploy the Skeleton Key malware whenever necessary. The Skeleton Key malware does not generate network traffic since this is not part of its attack. Although this lack of a Command and Control may make the Skeleton Key malware more vulnerable to analysis, it makes the Skeleton Key malware harder to detect due to the fact that many security methods rely on monitoring network traffic for anomalies in order to detect and stop threat attacks. Overall, the Skeleton Key malware should be considered for what it is, a threatening tool that may allow anyone to overcome single-factor authentication.
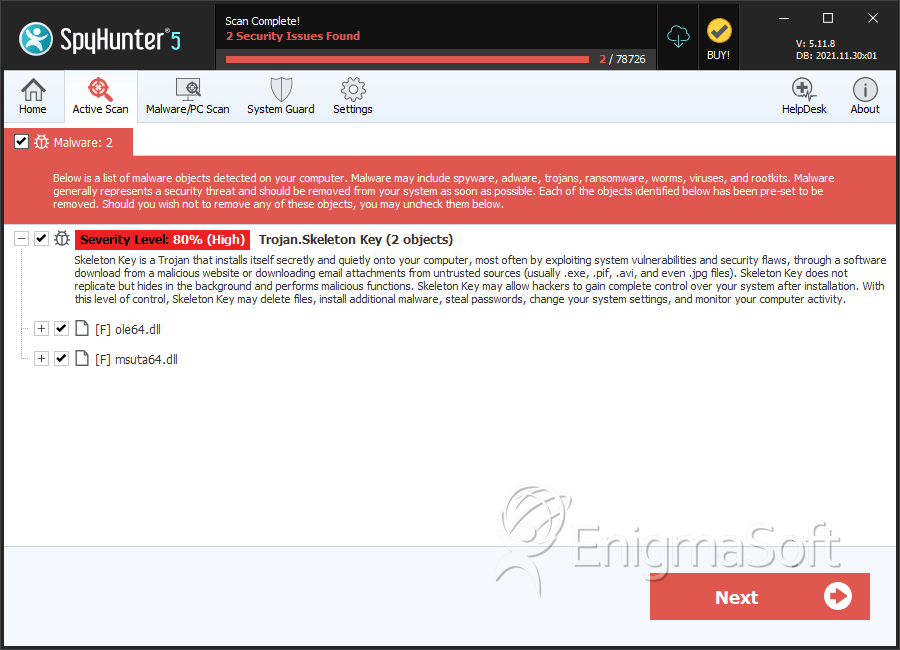
SpyHunter Detects & Remove Skeleton Key Malware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ole64.dll | bf45086e6334f647fda33576e2a05826 | 0 |
| 2. | msuta64.dll | 66da7ed621149975f6e643b4f9886cfd | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.