Shlayer Trojan
Shlayer Trojan Image
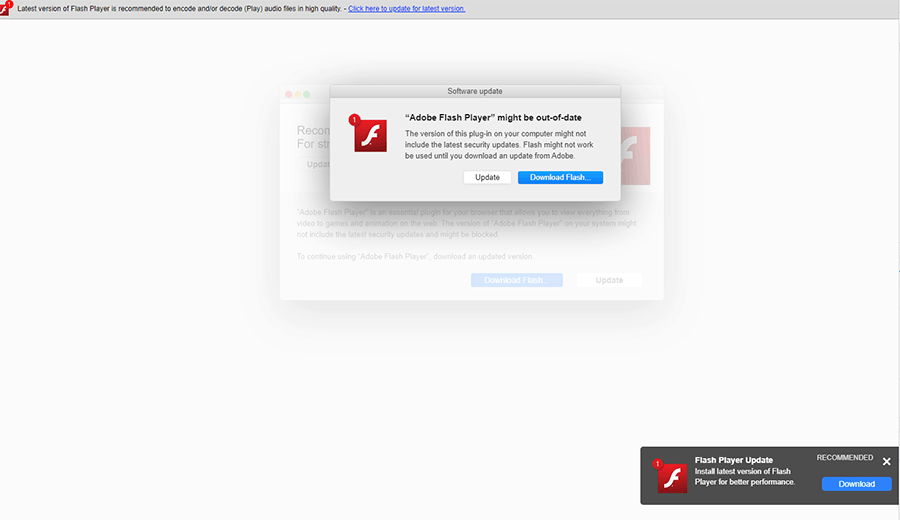
The Shlayer Trojan is a cyber-threat aimed at Mac users who might be interested in trying out application stores other than the official App Store by Apple. The Shlayer Trojan might be promoted to the users as an independent application delivery platform that offers discounts on premium software. The Shlayer platform was reported of delivering harmful programs, unwanted browser extension, unrequested Internet settings modifications, promoting questionable shopping helpers and distributing supposedly free premium applications. The Shlayer Trojan was recognized by computer security researchers in January 2019 when the users started reporting fake Adobe Flash updates to Web browser vendors.
It appears that the criminals behind the Shlayer Trojan follow the tried-and-true tactic of pushing Web users to install a supposedly legitimate update to their Adobe Flash Player plug-in before accessing protected media content. The Shlayer Trojan may be presented to the users via pages that mimic the official Adobe Flash Player site, and the users might experience in-browser notifications that look like Mac OS dialog boxes. We have seen phishing sites associated with the Shlayer Trojan display pop-up windows and play alarm sounds to convince the users to download and run a the Shlayer Trojan installer package. Notifications with the following text may lead the users to install the Shlayer Trojan on their devices:
'Adobe Flash player installer
Update your Flash Player in order continue
Security updates and enhancements are periodically released for
Adobe Flash player that can be downloaded and installed
automatically, please update your Flash in order to continue'
Web surfers may notice banners saying 'Latest version of Flash Player is recommended to encode and decode (play) audio files in high quality' on misleading pages that include a URL to a corrupted version of the official Adobe Flash Player software. You should not trust notifications like the one listed above and navigate to the legitimate site for Adobe Inc. products as opposed to following links on untrustworthy banners. The Shlayer Trojan is operated as a program that provides remote attackers with direct access to your device and Internet settings. The Shlayer Trojan might be used to install browser add-ons in Google Chrome, Mozilla Firefox and Safari, as well as run hidden applications on your system.
Initially, the Shlayer Trojan was used for pay-per-install tactics, fake clicks on advertisements and redirect users to low-quality search services. The threat actors behind the Shlayer Trojan may transition to more harmful practices in the near future and exploit unprotected third-party application stores. It is recommended to install applications from the official Apple store and keep your cybersecurity solution updated regularly.
Recommended steps to take to avoid Shlayer Trojan on Mac computers
- Scan unknown files using trusted antimalware or antivirus apps
- Enable a Firewall
- Download and enable ad-blocking software
- Read the fine print or comments before downloading and installing apps
- Utilize and keep trusted security, antimalware, or antivirus apps updated
- Never download keygens or cracks to unlock apps
- Keep the Mac OS X (operating system) updated at all times
Shlayer Trojan gets updated to aggressively attack Mac computers
During February 2019 Shlayer Trojan was found to be updated where it aggressively spreads fake Flash Player updates on Mac computers, which is an older method for tricking computer users into downloading additional malware on their system without apparent suspicion. Moreover, the campaign utilized by hackers who are spreading Shlayer Trojan are targeting BitTorrent users allowing the malware to be spread on a wider spectrum throughout the world.
List of files and file paths created by Shlayer Trojan once it is installed and loaded on a Mac OS X computer:
- /Applications/Advanced Mac Cleaner
- /Applications/MyMacUpdater
- /Applications/MyShopcoupon
- /Applications/mediaDownloader
- /Library/LaunchAgents/com.MyMacUpdater.agent.plist
- /Library/LaunchAgents/com.MyShopcoupon.agent.plist
- /mm-plugin.dylib
- /myshopcoupon.safariextz
- ~ Library/Application Support/amc
- ~ Library/Caches/com.apple.Safari/Extensions/Chumsearch+.safariextension
- ~ Library/LaunchAgents/com.pcv.hlpramcn.plist
- ~ Library/Safari/Extensions/Chumsearch+.safariextz
There used to be a time where fake Flash Players were leveraged on Windows PCs to trick computer users. However, in recent months there has been a major influx of threats that target Mac OSX computers through web-based infiltration methods, which the fake Flash Player can be said to be. The payload of Shlayer Trojan is known to collect system information and create a unique ID for the infected device so it may download additional malware from a remote server. As it turns out, the Shlayer Trojan malware payload in a secondary from is a .app executable that Mac computers may simply open and run by double-clicking the app.
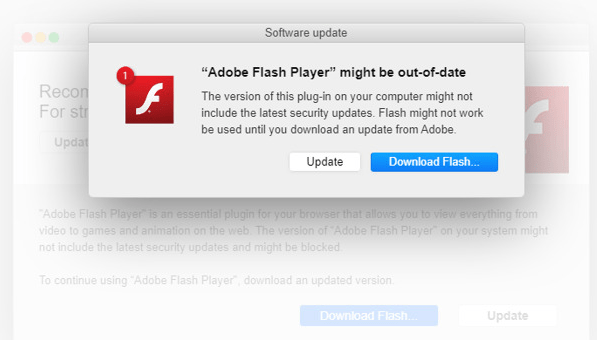
Representation image of a Fake Flash Player install prompt to load Shlayer Trojan on a Mac
Many personal details stored on a system infected by Shlayer Trojan are at risk of being exposed, such as usernames, passwords, and banking data. Web browsers loaded on the infected Mac may also be leveraged in ways to prompt site redirects loading pages that push fake applications that turn out to be malicious.
Never before have Mac computers been so heavily targeted by malware, and the Shlayer Trojan is among an onslaught of newer variations of malware that we’ve seen come into the fray of Mac malware.

