Sequre Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | May 3, 2018 |
| Last Seen: | October 18, 2018 |
| OS(es) Affected: | Windows |
The Sequre Ransomware is an encryption ransomware Trojan that PC security researchers first observed in April 2018, in the fourth week of this month. The Sequre Ransomware is delivered using damaged spam email messages that contain corrupted file attachments or embedded links leading to compromised websites. Once the Sequre Ransomware is installed, the Sequre Ransomware carries out an encryption ransomware attack. Threats like the Sequre Ransomware will take the victim's files hostage, making them inaccessible and demanding a ransom payment from the computer user in exchange for restoring access to the victim's data.
Table of Contents
How the Sequre Ransomware Trojan Attacks a Computer
The Sequre Ransomware uses a strong encryption method, a combination of the AES and RSA encryptions to make the victim's files inaccessible. The Sequre Ransomware will scan the victim's computer in search for files that can be targeted in its attack. The Sequre Ransomware behaves in a way that is very similar to HiddenTear. However, curiously, the Sequre Ransomware does not seem to be a HiddenTear variant and appears to have been created independently. The Sequre Ransomware targets the user-generated files such as media files and numerous document formats. Some of the files that are encrypted by the Sequre Ransomware attack include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
Once the Sequre Ransomware encodes the files, they will become identifiable easily because the Sequre Ransomware will change their names following the pattern 'sequre@tuta.io_ [hex code],' with a hex code that seems to be generated depending on the infected file's name and original file extension.
The Sequre Ransomware’s Ransom Demands
The Sequre Ransomware will deliver two files to the victim's computer after encrypting the victim's files; an HTA file named 'HOW TO DECRYPT YOUR FILES.hta' and a TXT file named '_HELP_INSTRUCTIONS.txt.' The Sequre Ransomware delivers a ransom note that includes a unique identifier for the victim, a text note asking for a ransom payment, and a Bitcoin wallet address for the victim to make the payment. The Sequre Ransomware demands that the victim communicates with the con artists via email at the address 'tosequre@tuta.io' to make the payment. Computer users must refrain from paying the Sequre Ransomware ransom, which equals 0.14 Bitcoin, or 1300 USD at the current exchange rate approximately.
Protecting Your Data from Threats Like the Sequre Ransomware
The best protection against threats like the Sequre Ransomware is to have file backups stored on independent devices. If your files are backed up, then it is possible to recover from a Sequre Ransomware attack by removing the corrupted files and the Sequre Ransomware threat itself and restoring the affected data from the backup. While the Sequre Ransomware threat itself is not difficult to remove since it can be done by most updated security programs (and in fact, it will often remove itself after the files have been encrypted), the files encrypted by the Sequre Ransomware attack are not recoverable with our current technology. Because of this, file backups are the best method to ensure that your data can be recovered after an attack.
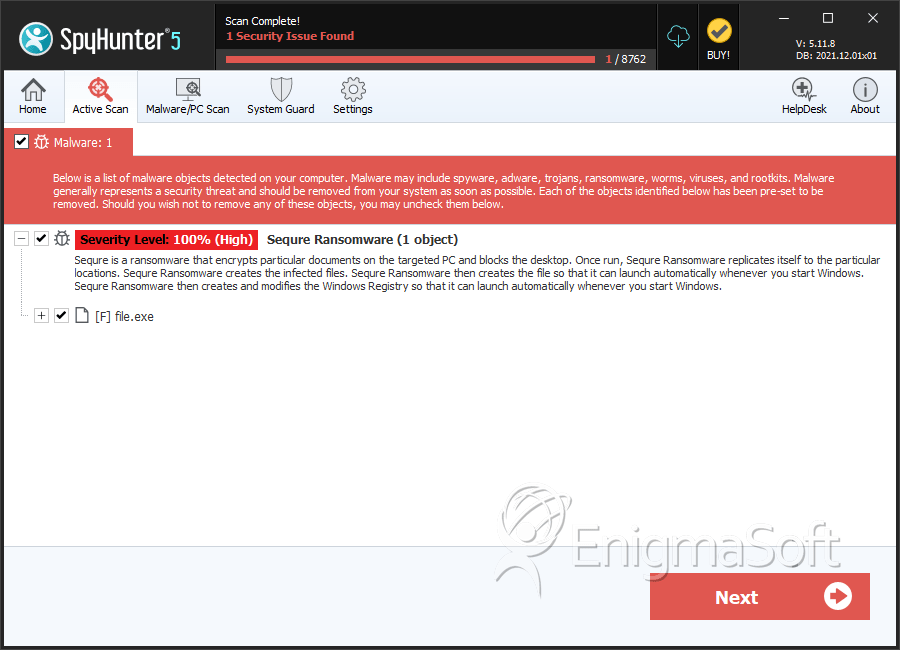
SpyHunter Detects & Remove Sequre Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c35506bd3fedad57e7f1ea975ebcaec5 | 0 |

