Sednit (Sofacy)
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
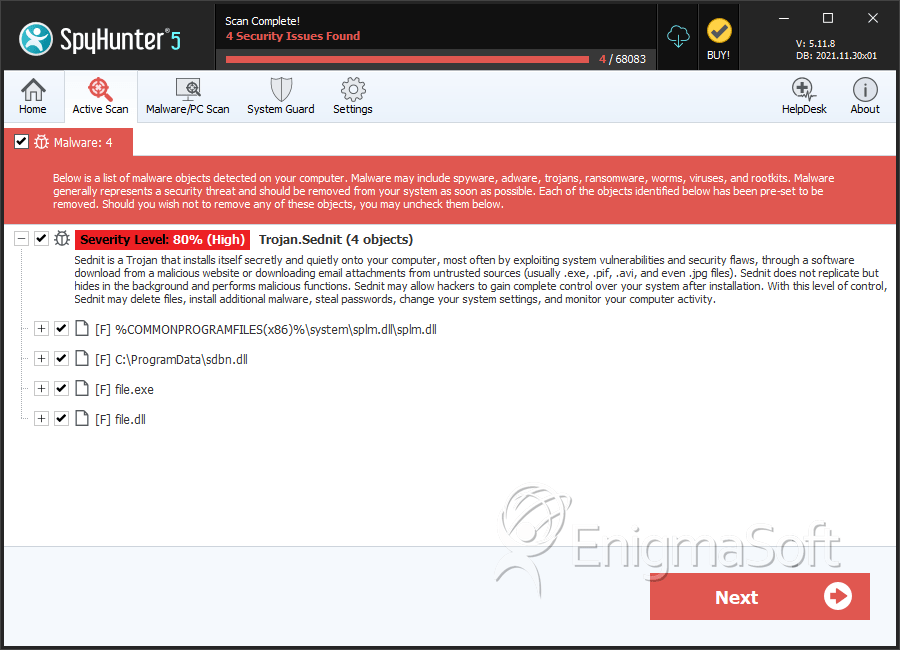
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 10 |
| First Seen: | October 29, 2014 |
| Last Seen: | March 26, 2022 |
| OS(es) Affected: | Windows |
 Sednit, also detected as Sofacy, is a threat that has been used by hackers as part of Pawn Storm attacks (a well-used cyber-infiltration method that targets government, media, and military-related organization). Sednit was developed to trespass its targets security and protection in order to register any useful information.
Sednit, also detected as Sofacy, is a threat that has been used by hackers as part of Pawn Storm attacks (a well-used cyber-infiltration method that targets government, media, and military-related organization). Sednit was developed to trespass its targets security and protection in order to register any useful information.
Sednit may invade a computer when the computer user clicks on a spam e-mail attachment that will trigger the installation of Sednit. Another invasion method used by Sednit is a phishing attack that involves Outlook Web Access users. Usually, ordinary computer users will not be attacked by Sednit since they do not belong to the targeted group selected by Pawn Storm attacks and, consequently, Sednit. However, we never know what the future has in store for computer users.
Table of Contents
US Election Malware Attack details uncovered
Diving into additional details about Sednit, or what is sometimes referred to as containing the malware threat Sofacy, Fancy Bear, APT28, or STRONTIUM, is that hackers have levered these threats in a way to steal data from particular targets. Moreover, the same Sofacy malware was claimed to be used in a hacking case in the Central Election Commission attack and found on the servers of the Democratic National Committee (DNC).
Sofacy, or Sednit, or any one of the various names used to identify the threat as a whole, has close ties to the Russian interface during the 2016 US elections.
Sofacy remains to be a culprit in the 2016 DNC Server attack
For obvious reasons, the 2016 US presidential election cycle had many suspected cases of hacking attacks, one of which was the DNC servers where Sofacy was uncovered. It is possible that Sofacy was utilized in many other cases of attacking servers belonging to entities involved with the presidential election. However, we're not ones to claim or expose such matters as they are highly controversial.
What we do know about Sofacy is that it was welded by hackers that originate out of Russia and other countries known for using aggressive malware threats to attack systems for the purpose of compromising data. No doubt that the US presidential campaign trail was one where everyone grappled for data or "dirt" on their opponent. Threats like Sofacy were certainly utilized by parties, mostly those out of foreign areas.
Sofacy origins and associations
Sofacy/Sednit dates back to 2015 when computer security researchers started seeing new components being developed by the culprits behind Sofacy. The Sednit backdoor threat, a spreading component of Sofacy at the time, is suspected to be a newer variation of a family belonging to downloaders and backdoors that compromise systems in ways that stored data may be accessed and stolen. The data gathered by Sofacy may be accessed by remote attackers, where many of the victims have been in various regions of the world. In fact, Zebrocy, believed to be the malware family that Sofacy/Sednit belongs to, is known to have three variations that coded in different languages, all on programmed with a quest to collect data from a compromised system. Zebrocy is known to have victims located in several countries, such as Azerbaijan, Bosnia, Egypt, Georgia, Iran, Kazakhstan, Korea, Russia, Saudi Arabia, Serbia, Switzerland, Turkey, Ukraine, Zimbabwe, and many others.
Remedying Sofacy’s path of destruction
Computer users and server administrators must be aware of the complications of threats like Sofacy. An attack orchestrated through Sofacy, and its large family of data-compromising threats could have grave consequences when private data is later exposed as a result. In any given case of suspecting such an attack or infection on a system, the users or administrators must take prompt action to remedy the satiation with the necessary resources before it's too late.
SpyHunter Detects & Remove Sednit (Sofacy)
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 4bfe2216ee63657312af1b2507c8f2bf362fdf1d63c88faba397e880c2e39430 | f8c8f6456c5a52ef24aa426e6b121685 | 2 |
| 2. | splm.dll | ee64d3273f9b4d80020c24edcbbf961e | 1 |
| 3. | sdbn.dll | 374896a75493a406eb427f35eec86fe5 | 1 |
| 4. | file.exe | df895e6479abf85c4c65d7d3a2451ddb | 0 |
| 5. | file.dll | 4b04b04c9d60bd2d75773298633f26e8 | 0 |
| 6. | file.exe | a5946714a9ac20f4facb0c8596525655 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.