Security Essentials 2010
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 60 |
| First Seen: | February 18, 2010 |
| Last Seen: | March 9, 2023 |
| OS(es) Affected: | Windows |
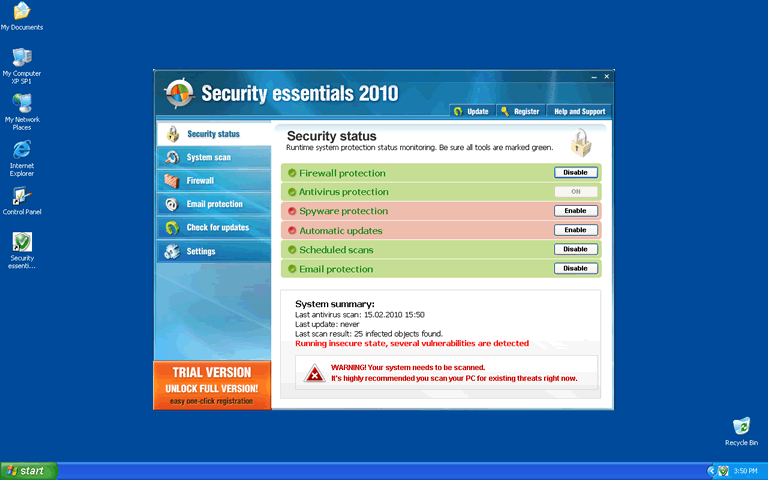
Security Essentials 2010 Image
Security Essentials 2010 is not a Microsoft product. Although the name is very similar to that of Microsoft Security Essentials, which is a real anti-malware program, Security Essentials 2010 is a rogue anti-malware application that tries to scare money out of the users of infected PC's. Also, Security Essentials 2010 is a rogue security application that just keeps coming back, in one way or another, sometimes under different names.
Table of Contents
Symptoms Caused by Security Essentials 2010
The signs of an infection with Security Essentials 2010 are easy to spot, because this fake security software will constantly pester you for money. Because Security Essentials 2010 will be configured to run when Windows starts, the first time you'll see Security Essentials 2010 will be when you boot your computer, and the Security Essentials 2010 interface appears. The interface uses a weird icon, with the Windows logo inside some kind of metal frame or lock, and there will be text in at least one or two places that says that you are using the "trial version" of Security Essentials 2010. Every time this interface loads, Security Essentials 2010 will pretend to run a scan of your computer, and then Security Essentials 2010 will tell you that a very large number of the core Windows files are actually viruses. Security Essentials 2010 will offer to remove these bogus threats, but only if you pay for the full or "licensed" version of Security Essentials 2010's software by visiting the phony Security Essentials 2010 website.
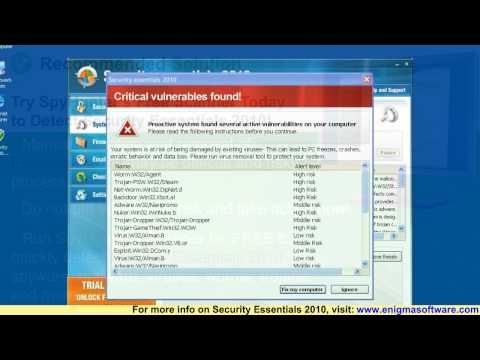
Security Essentials 2010 will also try to persuade you that your PC is in danger by generating fake security warnings, which will pop-up frequently. These warnings typically begin with the phrases Critical warning, System warning, Security warning, and Attention! Either the warnings will be very vague, claiming that your PC is unprotected, or they will say that a specific threat has been found, such as the Netsky worm. However, as is the case with the phony system scans, all of the claims made in these warnings are fake. Security Essentials 2010 can't actually detect or remove malware.
In order to protect itself and to try to convince you that your computer is in danger and in need of help, Security Essentials 2010 will prevent you from running other programs, including Task Manager. When you try to run something other than Security Essentials 2010 – or the web browser, since Security Essentials 2010 needs it in order to get you to the payment site – Security Essentials 2010 will shut it down, and give you a warning message that says that the program or file in question is dangerous. It should be obvious that not every program on your computer can be dangerous or infected, but Security Essentials 2010 will shut them all down anyway.
How Security Essentials 2010 Gets into your Computer, and where Security Essentials 2010 Comes from in the First Place
Like most rogue anti-virus programs, Security Essentials 2010 relies on a Trojan in order to find a way into victim PC's. In this case, the Trojan that supports Security Essentials 2010 is commonly called Win32/Fakeinit, and it is very frequently disguised as a Flash update, offered for download on a third-party website. The Trojan may also be bundled with a freeware download. Once you have been tricked into unknowingly downloading the Trojan, it unpacks the files for Security Essentials 2010. Sometimes, it also downloads another piece of malware, called Win32/Alureon, which steals personal information stored on the affected computer. Either way, Security Essentials 2010 will become active the next time you start Windows.
Security Essentials 2010 first appeared in February 2010, but Security Essentials 2010 reappeared in November 2010, sometimes calling itself Security Essentials 2010, and sometimes using the name Security Essentials 2011. Security Essentials 2010 is also essentially identical to other rogue security applications in this family, including Internet Security Essentials 2010 and Internet Security Essentials 2011. All of these fake security programs are part of a huge Internet-based scam.






Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Symantec | Trojan.FakeAV!gen24 |
| Panda | Suspicious file |
| Ikarus | Trojan.Renos |
| BitDefender | Trojan.Renos.Gen.1 |
| Symantec | CoreGuardAntivirus2009 |
| Sophos | Mal/Bredo-F |
| F-Secure | Trojan:W32/Fakexpa.BE |
| Kaspersky | Trojan-Downloader.Win32.FraudLoad.wyhz |
| Sunbelt | Trojan.Win32.Generic!BT |
| Panda | Adware/SecurityEssentials2010 |
| McAfee-GW-Edition | Heuristic.LooksLike.Trojan.FraudPack.I |
| McAfee | FakeAlert-MA |
| eSafe | Win32.FakeAlert.Ma |
| DrWeb | Trojan.Fakealert.12853 |
| AVG | SHeur2.CMHO |
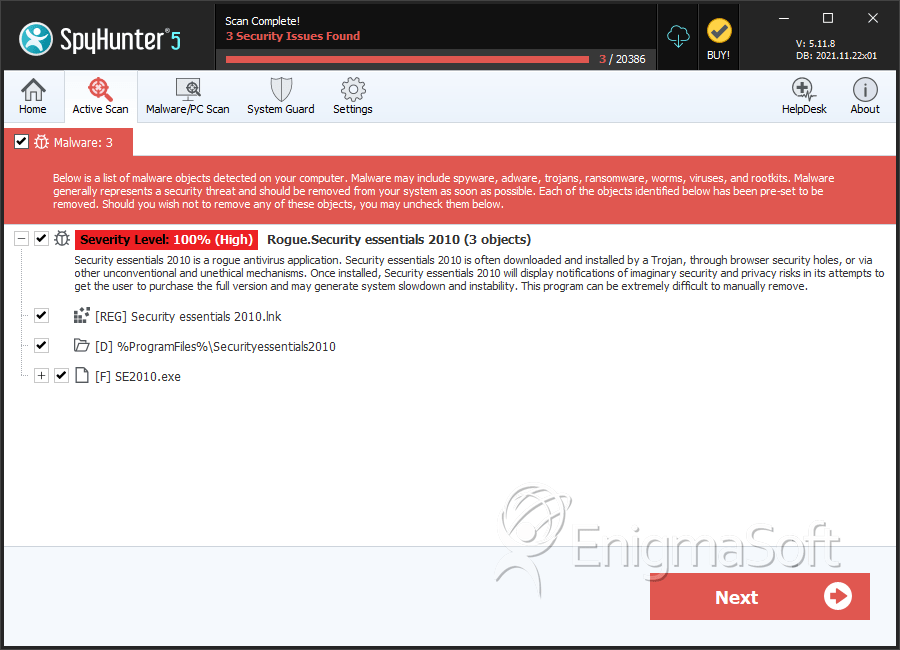
SpyHunter Detects & Remove Security Essentials 2010
Security Essentials 2010 Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | SE2010.exe | 5cb463586c30033bf89618f9c13be2e3 | 38 |
| 2. | SE2010.exe | b29cb77382dedb6b81854ed0f63e63e0 | 4 |
| 3. | SE2010.exe | 0f2e7c457ab4481c81544aaba8bcb212 | 0 |
| 4. | SE2010.exe | 8b6c61381388171658c0f2a5606f608b | 0 |
| 5. | SE2010.exe | e751e0120b1ef07f48e5552baaf6327d | 0 |
| 6. | SE2010.exe | bcffb70ca16ce7a17875d5daa4ba167f | 0 |
| 7. | SE2010.exe | 40c2459be511830d02c25da9ffc421a6 | 0 |
| 8. | SE2010.exe | 211b273cb032fa4654ccd86bac1a1fbf | 0 |
| 9. | SE2010.exe | 128431880239236564f932118f9ae3c7 | 0 |
| 10. | SE2010.exe | 98e738f6c4804accad556ede71196a1d | 0 |
| 11. | SE2010.exe | 8b9ee828183f776745f88ea9304fb1db | 0 |
| 12. | SE2010.exe | c390ad4dfa72d240ff150b731abc6dbb | 0 |
| 13. | SE2010.exe | b356b2cdd65cb6aa5fcadecf4d9499ae | 0 |
| 14. | SE2010.exe | 008927b901ca73202dd67707d9295f5e | 0 |
| 15. | SE2010.exe | 428e36c3c913da61290af3de382da346 | 0 |
| 16. | SE2010.exe | 4b446f7387efcbc6c2f6fa6bd2e548fd | 0 |
| 17. | SE2010.exe | b3dffa607d61f5c8fdceb8c444619008 | 0 |
| 18. | SE2010.exe | 3332f7820d7e185598106dc52941c902 | 0 |
| 19. | SE2010.exe | 88a7280d82682f5437007dc93fec7d38 | 0 |
| 20. | SE2010.exe | 0eda8b7d6d5b25b7023b2c04530555d0 | 0 |
| 21. | SE2010.exe | a2ff3479794dfc0ab0687f8ffb93d574 | 0 |
| 22. | SE2010.exe | ba907662a0187a074202f0d5f43eccbb | 0 |
| 23. | SE2010.exe | 816e01c35c8c7ae4c272f88e3a1e0262 | 0 |
| 24. | SE2010.exe | 1d0d2b02e037948c1a9c6b15e3b5e3f2 | 0 |
| 25. | SE2010.exe | 9936618c92561007f28084e4822c913e | 0 |
| 26. | SE2010.exe | c4ebd2b2a1612c7270aaec02bb44a263 | 0 |
| 27. | SE2010.exe | b45eb51f42ff8f5d0a398dba6669fbb5 | 0 |
Registry Details
Directories
Security Essentials 2010 may create the following directory or directories:
| %ProgramFiles%\Securityessentials2010 |
URLs
Security Essentials 2010 may call the following URLs:
| Buy-security-essentials.com |
| buy-security-essentials.com |
| essentials-free.org |
| essentials-pro.com |
| essentialsfree.info |
| essentialsfree.net |
| essentialsfree.org |
| essentialssite.com |
| securityessentials-2010.com |
| securityessentials2010.com |

