Salsa Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 13 |
| First Seen: | April 11, 2017 |
| Last Seen: | March 18, 2021 |
| OS(es) Affected: | Windows |
The Salsa Ransomware is a ransomware Trojan first reported in April 2017. The Salsa Ransomware seems to be a standalone ransomware threat rather than part of a larger family of ransomware. The most common way in which the Salsa Ransomware is being distributed is by attaching corrupted files to spam email messages. When the victim opens the file, a compromised script downloads and installs the Salsa Ransomware on the victim’s computer.
Table of Contents
The Too Spiced Salsa for Your Files
The Salsa Ransomware's intended target seems to be mainly corporate networks and servers, although the Salsa Ransomware attacks also can be quite effective against individual computer users. The Salsa Ransomware functions like most ransomware Trojans, encrypting the victim’s files by using a strong encryption algorithm to make them inaccessible. The Salsa Ransomware creates an index file that contains the names of all the files encrypted in the Salsa Ransomware attack. The Salsa Ransomware is designed to work fast in the background, encrypting as much of the victim's data as possible. The files encrypted in the Salsa Ransomware attack are marked with the file extension '.salsa222,' making it an easy task to know which files have been compromised in the Salsa Ransomware attack. It is likely that new variants of the Salsa Ransomware will be released over time. After encrypting the victim’s files, the Salsa Ransomware delivers its ransom note, which informs the victim about the attack and asks for the payment of a ransom. The Salsa Ransomware drops its ransom note in the following directory:
C:/ProgramData/DONOTDELETESALSA/CUCK%20HERE%20TO%20UNLOCK%20YOUR%20FILES%20SALSA222/READ%20TO%20UNLOCK%20FILES.salsa.html
The Salsa Ransomware’s ransom note is available in 40 different languages and is displayed on the infected computer’s default Internet browser. The full text of the Salsa Ransomware ransom reads:
'[LINKS TO VERSIONS FOR 40 LANGUAGES]
YOUR PERSONAL FILES HAVE BEEN ENCRYPTED/DAMAGED (USB, NETWORK, STORAGE, ...)
READ CAREFULLY IF YOU WANT YOUR FILES BACK!
IF YOU DO NOT PAY IN TIME THE PRICE WILL DOUBLE OR WURST YOUR FILES WEILL BE DELETED FOREVER!
Date (FILESS WILL BE DELETED FOREVER): [TIMESTAMP]
Date (PRICE WILL DOUBLE) : [TIMESTAMP]
Disable your Anti Virus now! If this program is deleted by your Anti Virus, you lose your files forever because it is impossible to decrypt your files!
PRICE: $500 in Bitcoins
We only accept bitcoins! Follow the steps below to decrypt your files:
Send exactly 0.465112 [BTC,BITCOINS] to this address: 1AY2tmQff1PYNM78B5VJaB4U6g7sGBY42y
After you send the payment, wait a few minutes...your files will be automatically decrypted and repaired. Your computer/files will be back to normal.'
PC security researchers advise against paying the Salsa Ransomware ransom or following the instructions in this ransom note.
Protecting Your Computer from an Attack
Computer users can recover from the Salsa Ransomware attack by restoring their files from a backup copy. Unfortunately, once the files have been encrypted in the Salsa Ransomware attack, they become unrecoverable. Because of this, the key to dealing with the Salsa Ransomware and other ransomware Trojans is to take preventive measures. Computer users should keep back ups of their files. Having file backups allows computer users the possibility of recovering from the Salsa Ransomware attacks without having to consider paying the ransom, which, in many cases, does not guarantee that the people responsible for the Salsa Ransomware attack will respond to the victim's request and provide the decryption key. Other important elements in preventing the Salsa Ransomware attacks include exercising caution when opening email attachments from unsolicited sources. This is especially important because corrupted email attachments are the main way in which the Salsa Ransomware and similar threats spread. Apart from having file backups and handling email with caution, having a reliable security program that is fully up-to-date is also an important element of protecting your computer from the Salsa Ransomware and other threats that use a similar attack.
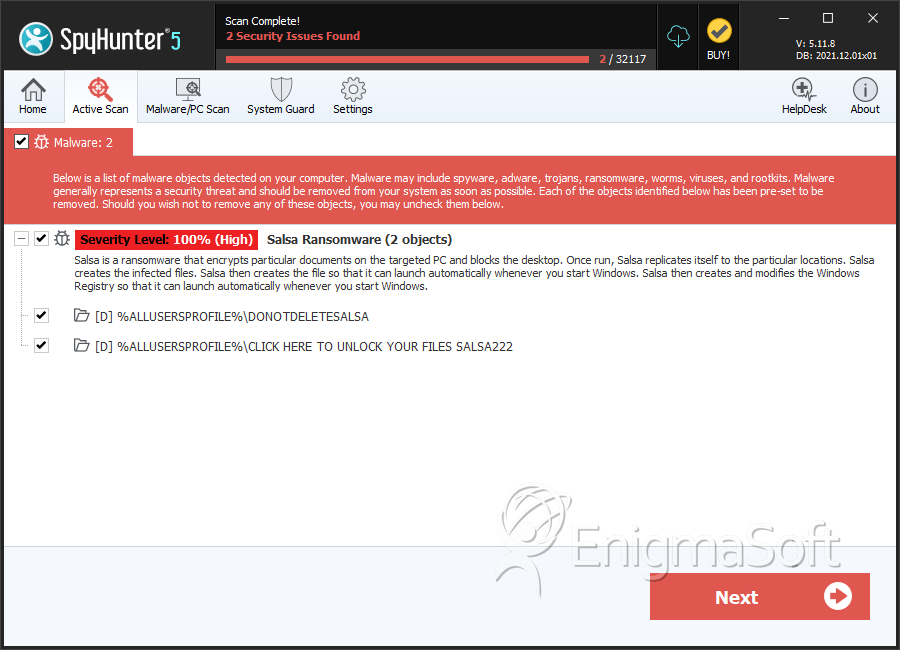
SpyHunter Detects & Remove Salsa Ransomware
Directories
Salsa Ransomware may create the following directory or directories:
| %ALLUSERSPROFILE%\CLICK HERE TO UNLOCK YOUR FILES SALSA222 |
| %ALLUSERSPROFILE%\DONOTDELETESALSA |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.