Sage 2.0 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,955 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 1,121 |
| First Seen: | December 5, 2016 |
| Last Seen: | September 9, 2023 |
| OS(es) Affected: | Windows |
The Sage 2.0 Ransomware is a ransomware Trojan that updates Sage, an already existing ransomware Trojan. The Sage 2.0 Ransomware carries out a typical ransomware attack, encrypting the victims' files and demanding the payment of a ransom. The files encrypted by the Sage 2.0 Ransomware will have the extension '.sage' added to the end of the file name. The Sage 2.0 Ransomware delivers its ransom note in an HTML file named 'Recovery_[3_random_characters].html,' which is dropped in each directory where files were encrypted. The Sage 2.0 Ransomware also demands its ransom by changing the infected computer's Desktop image into a ransom note.
Table of Contents
The Outrageous Sum Demanded by the Sage 2.0 Ransomware
The Sage 2.0 Ransomware's ransom note informs the victim of the attack and demands the payment of $2000 USD in BitCoin. The Sage 2.0 Ransomware uses a strong encryption method and, unfortunately, the files that the Sage 2.0 Ransomware encrypts cannot be recovered without the decryption key (which the con artists will hold in their possession). The Sage 2.0 Ransomware's ransom is paid through a website, which is linked in the Sage 2.0 Ransomware's ransom note. The Sage 2.0 Ransomware claims that if the ransom isn't paid within a certain time frame, the decryption key will be deleted, which will doom the victim's files forever. PC security researchers strongly advise against paying the Sage 2.0 Ransomware ransom, since there is little chance that the con artists will keep their promise to restore the victim's files. The best protection against threats like the Sage 2.0 Ransomware is to have file backups on the cloud or an external memory device.
How the Sage 2.0 Ransomware Carries out Its Attack
The Sage 2.0 Ransomware is virtually identical to countless other ransomware Trojans. Fortunately, since the Sage 2.0 Ransomware has gone through various iterations, the content associated with the attack has become fairly well-known among PC security researchers. After the Sage 2.0 Ransomware changes the victim's Desktop image, it replaces it with the following message:
'Need help with translation?? Use https://translate.google.com
ATTENTION! ALL YOUR FILES WERE ENCRYPTED!
PLEASE READ THIS MESSAGE CAREFULLY
All your important and critical files as well as databases, images and videos and so on were encrypted by software known as SAGE!
SAGE 2.0 uses military grade elliptic curve cryptography and you have no chances restoring your files without our help!
But if you follow our instructions we guarantee that you can restore all your files quickly and safely!
To get the instructions open any of this temporary links m your browser:
This links are temporary and will stop working after some time, so if you can't open these links, you can use TOR Browser
The TOR Browser is available on the official website https://www.torproiect.org/
Just open this site, click on the "Download Tor" button and follow the installation instructions, then use it to open the following link:
Please be sure to copy this instruction text and links to your notepad to avoid losing it.
This crypto ransomware encrypts user data using the AES, and then calls go to the Tor-site to pay a ransom in Bitcoin and get instructions on how to return the files. Redemption amount: $ 2,000 (~ 2.15550 Bitcoin). After 7 days, the amount of foreclosures doubled.'
Victims of the Sage 2.0 Ransomware attack are redirected to a website hosted on the anonymous TOR network. When victims land on the website, they will be greeted with the following message:
'Important Information! Please read very carefully!
Attention!
Sage 2.0 encrypted all your files!
All your files, images, videos and databases where have been encrypted and no longer accessible by software known as Sage 2.0!
To restore all your files you need to pay $2000 (≈2.17965) for the decryption.
The after full payment, you will be able to download the software to restore your data.
In the case of non-payment of the full commission within 5d 05h,
the amount of commission will be raised to $4000 (≈4.35929)
You have no chance to restore the files without our help!
The files will restored easily if you will follow our instructions!
In case of the repeated non-payment of the increased commission during the 5d 05h period,
the unique decryption code for your files will be blocked
and its recovery will be absolutely impossible!'
The Sage 2.0 Ransomware payment website includes an additional message with more specific instructions on how to pay the Sage 2.0 Ransomware ransom. The following is the text displayed in this 'Payment' page:
'Payment procedure How to pay?
Payment can only be made using the BitCoin system.
So you can be sure that in the case of full payment of the commission, all your files will be decrypted.
Please note that BTC currency rate as any other currency rate in the world is not fixed. It tends to increase, therefore we advise you not to delay the BTC currency purchase and payment.
If you want to learn more what is Bitcoin, then watch this YouTube Video or visit WeUseCoins website.
How to pay within the BitCoin system?
Don't worry, the payment process in the BitCoin system is not difficult and requires few simple steps.
First of all, you need to create your Bitcoin currency (BTC) wallet.
We recommend to use most popular and easy-to-use online BlockChain.info wallet.
Or you can install Electrum software wallet for any OS you need
Next, you need to top-up your Bitcoin wallet's balance.
Below is the list of trusted services where you may buy Bitcoin. These services absolutely are not related to us!
If you can't find the option that suits you, then maybe you need to try find the solution in Google?
To receive the payment from you, we have created the unique Bitcoin wallet.
Further you need to make transaction from your own Bitcoin-wallet to the Bitcoin-wallet which we have prepared for you.
You can see it below (large font).
This wallet has been created especially for you and the amount paid can not be lost!
Send 2.17965 to the following wallet: 1EjHLfL5yy4o7pjG7sfvPrQfPwfMtVT4J8
If you already made the partial payment before, you can see there the remaining amount that you need to pay.
If you need to save or copy your BTC wallet address don't try to write it down by hand.
If while making the transaction you type the wrong BTC wallet number, the money will be lost!
Therefore, if necessary, print out the BTC wallet address you need or use the QR-code scanner on your smartphone/tablet.
Keep in mind that some Bitcoin purchase services are not work in real time and have the delay in payment processing.
The delay may last from 1 to 36 hours.
We therefore recommend you not to put aside the decision of payment until the last moment. Failure to pay on time may result in the increase of the payment amount!
After full payment you can download the decryption software from the Instructions section and use it with your personal decryption key.
We guarantee that all your files will be decrypted.
Note: Due to the configuration of some browsers simply reload this page does not always update the current information.
Please logout and relogin into your account to check the actually decryption status.'
The Sage 2.0 Ransomware displays instructions for the victim to decrypt the files 'helpfull.' These instructions are typical of these attacks. Unfortunately, without the decryption application, they will not be useful for computer users to recover from the Sage 2.0 Ransomware attack. Below are the instructions presented in the 'Instructions' page:
'Instructions What to do after the payment is made? How to decrypt all your data?
After payment you can download the decryption software from the home page. We guarantee that all your files will be decrypted.
Just follow these simple steps:
1. Login to your personal page
2. Copy the decryption key from field on the home page
3. Click "Download decryption software" button and save Sage2Decrypter.exe to your hard disk
4. Run Sage2Decrypter.exe
5. Paste the decryption key into "Key code" field in the decryption software window.
6. Select folder or disk you want to decrypt.
7. Click "Decrypt" button and wait for successfully completion of the decryption process
8. IMPORTANT: Don't turn off or reboot your PC before the process is completed!
9. Congratulations! Now all your files are restored!'
Similarly to legitimate software and operations, the Sage 2.0 Ransomware also includes a 'Support' page. The following is the full text of the Sage 2.0 Ransomware 'Support' page:
'If you still have some questions on the work of our service, please use the special form to contact our support service.
We will be glad to answer any questions you may have.
Note: Due to the configuration of some browsers simply reload this page does not always update the current information.
Please logout and relogin into your account to check the actually decryption status.'
The people responsible for the Sage 2.0 Ransomware have updated this threat regularly, making slight changes to its ransom notes and attack patterns, including small stylistic changes such as the color of the font used in the ransom notes or the design of the ransom note.
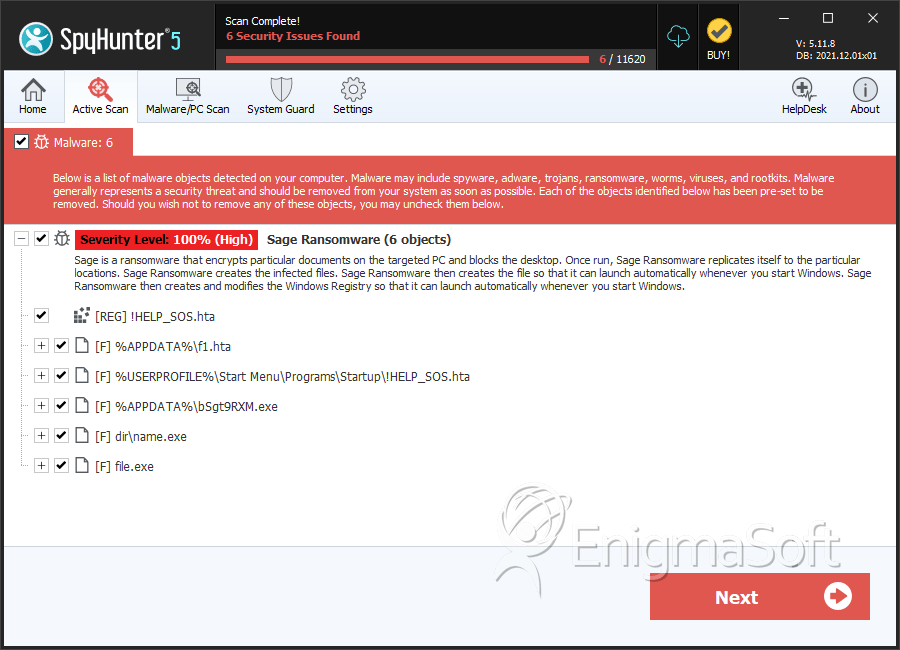
SpyHunter Detects & Remove Sage 2.0 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | f1.hta | da3fc4dc0cab7127d2228eea660def92 | 91 |
| 2. | f1.hta | 69ffb32f0a73e94492e1de2759ec4e47 | 58 |
| 3. | f1.hta | 0e962b17327cf256a7a9aac36bcc2e73 | 42 |
| 4. | f1.hta | 3d2a8e8b0c01ee4c0bafc49feb66dcf8 | 39 |
| 5. | f1.hta | 3d06a605002f0804b7ee4b28b5b0add1 | 38 |
| 6. | f1.hta | cef78bb8b23c09271a714810bee83ead | 37 |
| 7. | f1.hta | 9ac24a74c5fb285bda11a36f2572f358 | 30 |
| 8. | f1.hta | f043948461a12b1013c69cb0f9202db9 | 25 |
| 9. | f1.hta | 996df93357dd6b84ff3f4bb776799008 | 22 |
| 10. | f1.hta | ba63852da88e3217747e246c13f0b350 | 22 |
| 11. | f1.hta | 5b665ea43bb8bd2752c2a676aec9095d | 22 |
| 12. | f1.hta | 2df49f17d4b5faadebd80e0ba8abd64c | 14 |
| 13. | f1.hta | 75e0befbf9f654183f8fd28b568df045 | 13 |
| 14. | f1.hta | 56c72facc278384e05dc2f7aa0eab860 | 13 |
| 15. | f1.hta | 793dbbc4261f681a5d204e8e196d11bc | 12 |
| 16. | f1.hta | 4856de358dd83e9562b0864c7d1ed40c | 12 |
| 17. | f1.hta | 5760263e095cd4fec28a0d8a5b3a8e2a | 12 |
| 18. | !HELP_SOS.hta | b98ea223d2147b74a151614b756a84fd | 11 |
| 19. | f1.hta | e00e17e5c7525ed68e1b660239a81e3f | 10 |
| 20. | f1.hta | e68e9dfeb02037693858df00008d0af0 | 10 |
| 21. | f1.hta | 5947e68e4358be02cd264a68bc8e22c3 | 10 |
| 22. | !HELP_SOS.hta | f6339a90d5a71c514a1d1aeeeb44829c | 10 |
| 23. | f1.hta | 22dda250b1f467bdc19d4075c9da1327 | 10 |
| 24. | !HELP_SOS.hta | 557ae920ab0898fba2a5b05ea3167ab5 | 4 |
| 25. | !HELP_SOS.hta | 7dfb4582aec404f6ec68614a476cb178 | 4 |
| 26. | !HELP_SOS.hta | a8c342224490fb8a30616ded6d030622 | 1 |
| 27. | !HELP_SOS.hta | b339f1cdfd77aeb604727798e33af202 | 1 |
| 28. | file.exe | c167732d2390deb95b081c97caf23cc2 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.