Rietspoof
The Rietspoof malware is an advanced cyber threat that was announced to the wide public in February 2019, but its development was tracked since August 2018. The attacks involving the Rietspoof cyber-threat seem to be geo-restricted to the USA, based on initial threat assessment reports. The threat actors behind Rietspoof employ a multi-stage infection tactic aimed at evading AV scanners, the built-in Windows code execution prevention and potential problems with network monitoring tools.
Rietspoof Might Infect Users via Skype and Facebook Messenger
Computer security experts warn that the Rietspoof malware is distributed via obfuscated Visual Basic scripts sent from fake accounts on Skype and fake profiles on Facebook. PC users may be contacted by seemingly legitimate profiles that pose as friends of their friends. You may be directed to download an installation a package of a Web browser plug-in before you can play a family video and access photos that might include you. It is all a ruse to make you run the proposed VBS file and allow an encrypted CAB file to be downloaded to the TEMP directory on your system.
This is the second-stage of the infiltration, where the CAB file is loaded in the RAM, and it contacts the 'Command and Control' servers over a secure connection. Analysis showed that the Rietspoof malware used a standard TCP connection with added HTTPS features initially. However, a new version in January 2019 started using a custom-made network protocol and supports full HTTPS features. The harmful CAB file associated with Rietspoof proceeded to download a Trojan bot that can download and upload files, start processes, or wipe itself from the infected memory drive.
Rietspoof Creates 'Windowsupdate.Lnk' to Gain Reboot Persistence
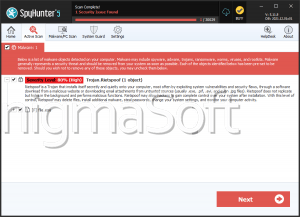
The Rietspoof Trojan is reported to create a custom starter module named 'Windowsupdate.Lnk' and save it to the Startup folder on Windows. Thus, the OS loads the Rietspoof main component, which then connects to its commands servers and can downloader other harmful binaries. The use of the Rietspoof seems to fall under the category of Trojan downloaders, but Rietspoof might be used for crypto jacking operations and making the infected hosts acts as proxies for Web traffic from other devices. AV engines include detection rules for the Rietspoof malware and PC users that notice questionable network transmissions and poor CPU performance may want to run a complete system scan.