Resurrection Ransomware
The Resurrection Ransomware carries out a typical ransomware tactic. One of the aspects of the Resurrection Ransomware that has caught the attention of malware researchers is that the Resurrection Ransomware will play music along with its ransom note, a little detail that makes the Resurrection Ransomware fairly unique in a landscape where countless ransomware variants are active simultaneously, being used to trick computer users in the wild. Like other ransomware Trojans, the Resurrection Ransomware is mainly designed to extort computer users by encoding their files and then stipulating the payment of a ransom.
Table of Contents
The Ironic Ransom Message Displayed by the Resurrection Ransomware
Apart from the fact that the Resurrection Ransomware plays music in the background along with its ransom note (a fact that adds to the irritation factor of this threat), there is little to distinguish the Resurrection Ransomware from other ransomware Trojans that are active currently. The following is the ransom note that the Resurrection Ransomware will deliver to its victims during an attack:
'Hi, this is not your luck day because this is not a joke, all your files has been encrypted with Resurrection-Ransomware
If you waut to retrieve all of your files I recommend you follow my simple instructions because you have no way out
Send me 1.77 Bitcoin (3918 USD Dollars or 3500 Euros) to this address: 1B1encH1cncoBjH64K1JfgLF1GqoY9dwpJ
If you do not know what bitcoins are or you do not know how to buy them, I suggest you visit the official site
https://bitcoin.org/en
https://bitcoin.org/en/exclianges
After making the payment please contact me resurrection777@protonmail.com here you will receive the decryption key for your files.
You have to make payment upon expiration of this expiration you will lose forever all your files and your pc will be formatted.
I suggest you not to underestimate this message and to follow my instructions carefully....... TIC TAC THE TIME FLOWING'
The Resurrection Ransomware will be delivered to its victims using spam email messages. These email messages may use various social engineering tactics to trick victims into opening a file attachment. These file attachments may take the form of Microsoft Word documents or PDF files that use corrupted scripts to download and execute the Resurrection Ransomware on the victim's computer. Once the Resurrection Ransomware has been installed on the victim's computer, the Resurrection Ransomware will encrypt the victim's files. The Resurrection Ransomware will rename the affected files, making it fairly simple to know which files have been affected by the attack.
The Resurrection Ransomware’s Ransom Demand Music
One aspect of the Resurrection Ransomware that has been somewhat curious is that it plays music in the background during this attack. Although this is not a new characteristic by any means, it is extremely uncommon. The music played by the Resurrection Ransomware on the victim's computer is somewhat creepy; it could perhaps be appropriate for Halloween or a similar event.
Dealing with the Resurrection Ransomware
At first glance, the Resurrection Ransomware is like most ransomware Trojans that are active currently in that it may be impossible to recover the affected files after a Resurrection Ransomware infection. However, the Resurrection Ransomware does not remove the Shadow Volume Copies of the affected files on the hard drive (a step that most ransomware Trojans take as part of the infection process). Because of this, many computer users may have success in recovering their data using a file recovery tool (of course, first the Resurrection Ransomware infection itself would have to be removed with the help of a reliable security program). Some decryption utilities that are active today (such as the 'Stupid Decryptor') have been capable of helping some computer users recover their files. However, as always, the best protection is to have file backups on an external memory device or the cloud to allow easy and fast recovery of all files after removing the Resurrection Ransomware infection itself.
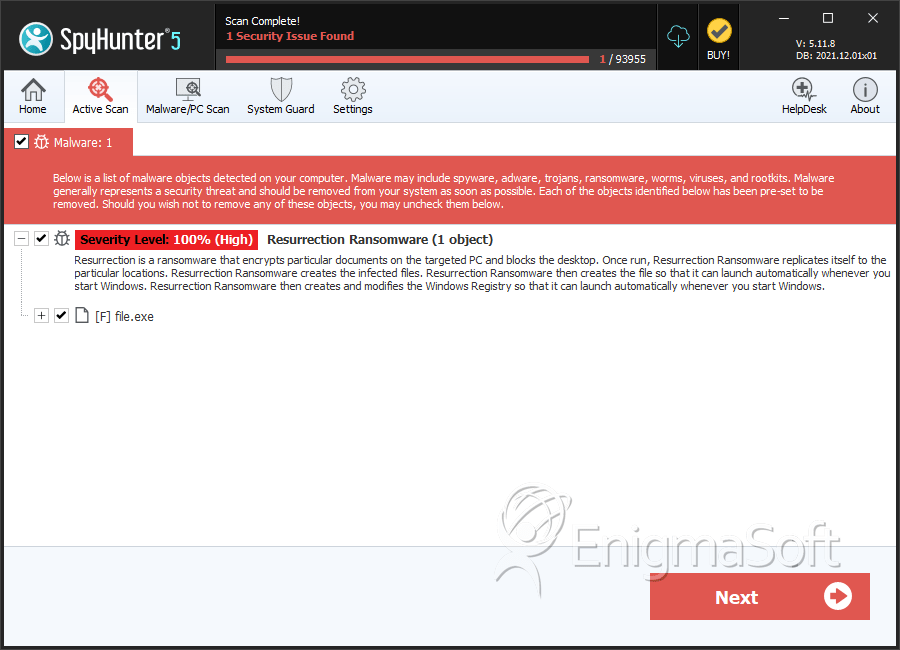
SpyHunter Detects & Remove Resurrection Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 898b9d28cfd2ab0e8de2d34c8273078b | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.