RedAnts Ransomware
The RedAnts Ransomware is a ransomware Trojan that was first observed in March 2017. The RedAnts Ransomware carries out a typical ransomware attack, which involves encrypting victims' files with a strong encryption algorithm to make them inaccessible. Victims of the attack are then asked to pay a large ransom to recover their files. Malware researchers strongly advise computer users to take preventive measures, since attacks like the on executed by the RedAnts Ransomware have increased in popularity in the last year substantially, and are predicted to become ever more common. Fortunately, protecting a computer is simple; having file backups makes computer users invulnerable to these attacks completely.
Table of Contents
These Red Ants will Attack your Wallet
The RedAnts Ransomware uses a strong encryption method to encrypt the victims' files. The files encrypted using the RedAnts Ransomware will have the extension '.Horas-Bah' added to the end of their file names. The files encrypted by the RedAnts Ransomware will become inaccessible completely, unreadable by Windows. The RedAnts Ransomware is written using the Assembly programming language and can be used to infect both 32-bit and 64-bit versions of the Windows operating system.
The RedAnts Ransomware is one of the countless variants in the HiddenTear family of ransomware. This family of ransomware is based on an open source ransomware Trojan that was originally released for 'educational' purposes. Unfortunately, since its release, HiddenTear has been responsible for countless ransomware variants, which have managed to weaponize this ransomware engine with very little modification. The RedAnts Ransomware seems to be a variant of MafiaWare, where both use ransom notes that are virtually identical in every aspect except for the BitCoin Wallet address used to carry out the payment.
The RedAnts Ransomware attack is typical of these threats. The RedAnts Ransomware will delete the System Restore points and the Shadow Volume Copies to prevent these recovery methods. The RedAnts Ransomware scans the infected computer for certain file types and then encrypts them using the AES-256 encryption. The files encrypted by the RedAnts Ransomware will have the extension '.Horas-Bah' added to the end of each file name. This makes it easy to know which files have been compromised during the attack.
How Con Artists may Profit from the RedAnts Ransomware
The RedAnts Ransomware attack will demand the payment of a ransom from the victim. Victims are asked to contact an email address from the @india.com domain to obtain information on how to pay the ransom. The victims of the RedAnts Ransomware must make a payment of $200 USD to a BitCoin Wallet address and then contact the con artists to confirm the payment. This payment method is used by numerous other ransomware Trojans. PC security researchers strongly advise computer users against paying the RedAnts Ransomware ransom, since this allows con artists to continue financing their activities. Apart from this, a very large percentage of ransomware creators may fail to follow up after the victim pays the ransom, or continue the extortion, asking for even more money.
Dealing with a RedAnts Ransomware Infection
Computer users should avoid paying the ransom. The best protection against the RedAnts Ransomware is to have backups of all files. Computer users are advised to restore their files from backup copies after removing the RedAnts Ransomware threat itself with the help of a reliable security program that is fully up-to-date. Having backup copies on the cloud or an external memory device can allow computer users to recover their files quickly and make these attacks ineffective completely. If computer users can recover, then the con artists lose the leverage that they have to demand ransom payments from the victims. In fact, once enough computer users worldwide have backups as a regular occurrence, it is likely that these attacks will become far less common.
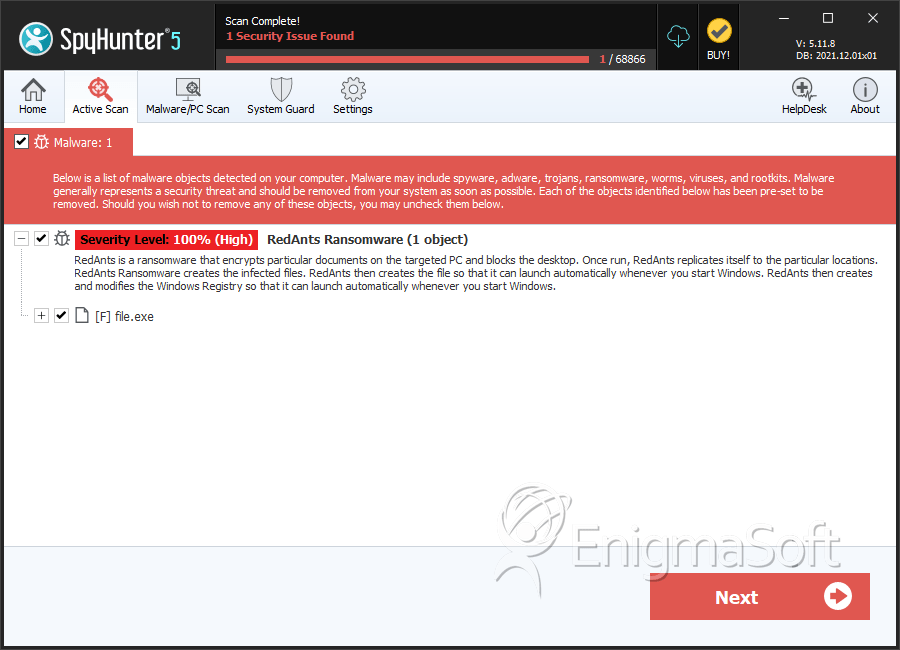
SpyHunter Detects & Remove RedAnts Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 8941f44f8d91c837cc97c8f66410662e | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.