Recovery Ransomware
The Recovery Ransomware is an encryption ransomware Trojan. The Recovery Ransomware is being distributed to computer users through a fake patch for the Windows Defender that is being distributed online to potential victims. The Recovery Ransomware carries out a typical encryption ransomware attack, taking the victim's files hostage by encrypting them with a robust encryption algorithm and then demanding payment of a ransom in exchange for the return of the affected files.
It is not Easy to Recover from a Recovery Ransomware Attack
Threats like the Recovery Ransomware are designed to take the victims' files hostage, typically using a strong encryption algorithm to make them inaccessible. The Recovery Ransomware is often distributed as an executable file named 'win_defeder_patch.exe,' which, once installed on the victim's computer, will target the user-generated files such as media files, numerous types of documents, databases, and many other data types. The following are examples of the file extensions that the Recovery Ransomware will generally search for when carrying out its attack:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
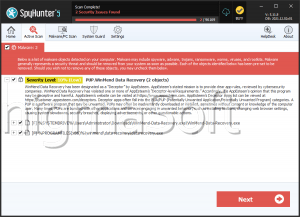
The Recovery Ransomware displays a pop-up window after encrypting the victim's files. This window contains the Recovery Ransomware's 'ransom note,' which essentially contains a list of all the directories that were encrypted by the Recovery Ransomware attack, as well as a brief note about what happened and a contact email address. The note is poorly written, making it apparent that the criminals responsible for the Recovery Ransomware attack are not native English speakers. Apart from this, there are other reasons to believe that the criminals responsible for the Recovery Ransomware attack do not have considerable resources, such as the encryption used to make the victim's files inaccessible.
The Recovery Ransomware Uses a Weak Encryption Algorithm in Its Attack
Most encryption ransomware Trojans use the AES or RSA encryptions to make the victim's files inaccessible, since they cannot be decrypted without the decryption key. However, the Recovery Ransomware uses the DES (Data Encryption Standard), considered an outdated form of encryption that can, today, be decrypted. In fact, PC security researchers have reported that they have been capable of recovering the files encrypted by the Recovery Ransomware and other threats using DES for their encryption. Having the ability to restore the files encrypted by these attacks is not usual, and computer users are strongly advised to take precautions to ensure that they can recover in the event of a ransomware Trojan attack using a stronger encryption standard than the Recovery Ransomware. Because of this, the best protection against all encryption ransomware Trojans is to have backup copies of all data and store these backup copies in a secure, offline location.