Ransom X Ransomware
Ransom X Ransomware Image
Ransom X Ransomware is the name of a newly uncovered data-encrypting Trojan that has already been deployed against the Texas Department of Transportation. Unlike most file-lockers that tend to target regular users, the Ransom X Ransomware appears to be used against high-value targets only. Another significant difference between most data-lockers and the Ransom X Ransomware is that the latter does not rely on phishing emails, torrent trackers or fake software updates to infect the targeted hosts. Instead, the Ransom X Ransomware is deployed against each target manually. To do this, the operators of this threat need to have elevated privileges on the compromised system.
This Week In Malware Episode 21 Part 2: Texas Ransom X Ransomware Threat Goes Global Attacking Govt & Enterprise Agencies
Since the Ransom X Ransomware is launched manually, it does not need to try and disguise its threatening activity on the host. As soon as the threat is deployed on the system, it will spawn a window that shows the progress of the campaign. By the time the attack is completed, the operators of the Ransom X Ransomware will know:
- The exact number of locked files.
- The extension that has been appended to the affected files.
- The total time spent on completing the attack.
When the Ransom X Ransomware is active on the targeted system, it will check for 289 processes that are linked to anti-malware suites, remote access connections, database management, email servers, etc. When the Ransom X Ransomware detects a process that matches the set criteria, it will terminate it immediately. This step is necessary so that all the targeted files will be encrypted successfully, as any files used by the processes in question will not be available for encryption. However, the Ransom X Ransomware is programmed to avoid encrypting specific folders and files, as tampering with them may result in a system malfunction.
To make it more difficult for the victim to recover the encrypted files, the Ransom X Ransomware will make sure to:
- Disable the Windows Recovery Environment.
- Disable the Windows System Restore.
- Wipe out the Windows Event logs.
- Wipe out the Windows backup data.
- Remove NTFS data.
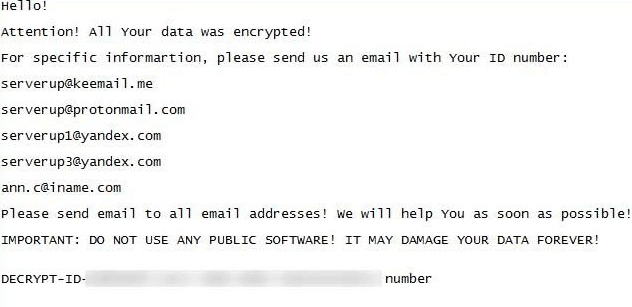
It would appear that the Ransom X Ransomware generates a unique extension for each victim. The Texas Department of Transportation reports that the encrypted files on their systems had the ‘.txd0t’ extension appended to their names. The ransom note of the Ransom X Ransomware contains the extension name, and in the case of the aforementioned target, the file was called ‘!_README_ME!.txt.’
The Ransom X Ransomware is a very threatening Trojan, but for now, it has a low infection rate. This is due to the fact that the attackers appear to go after carefully selected high-value targets only. Unfortunately, a free decryption tool is not available for the victims of the Ransom X Ransomware.

