RansomPlus Ransomware
Not much is known currently about the RansomPlus Ransomware, released in January 2017, although it is likely that PC security researchers will learn new information about this threat quickly. The RansomPlus Ransomware is one of countless ransomware Trojans that are released daily by con artists to carry out ransomware attacks on victims. The RansomPlus Ransomware, like other ransomware Trojans, generates revenue by threatening computer users and taking their files hostage until the victims pay a ransom. The RansomPlus Ransomware makes the victim's files unusable by encrypting them with a strong encryption algorithm. Although it is not possible to decrypt the files that have been affected by the RansomPlus Ransomware infection, it is not unlikely that PC security researchers will release a decryption utility eventually. Meanwhile, the only way to recover the affected files is to replace them with backup copies. Because of this, it is absolutely essential that computer users have backups of their files on an external device or the cloud.
Table of Contents
You can Find the Files Encrypted by the RansomPlus Ransomware Easily
The RansomPlus Ransomware enters a computer after the victim opens an infected email attachment, or being exposed to this threat through other means (such as attack websites or corrupted files distributed on file sharing networks). Once the RansomPlus Ransomware infects a computer, it begins encrypting the victim's files using its encryption algorithm. The files affected during the RansomPlus Ransomware infection will be marked by the RansomPlus Ransomware with the extension '.encrypted,' which is added to the end of each encrypted file's name. After encrypting the victim's files, the RansomPlus Ransomware drops a ransom note on the infected computer's Desktop. It is a text document named YOUR FILES ARE ENCRYPTED!!!.txt that contains the following message:
'YOUR FILES ARE ENCRYPTED!!!
To restore (decrypt) them you must:
1. Pay 0.25 bitcoin (btc) to address [deleted]
You can get BTC on this site http://localbitcoins.com
2. After payment you must send Bitcoin Transaction ID to E-mail: andresaha82@gmail.com
Then we will send you decryption tool.'
Victims of the RansomPlus Ransomware are asked to contact the con artists using the email address andresaha82@gmail.com. However, PC security researchers strongly advise against contacting these people. Paying the RansomPlus Ransomware ransom will often result in nothing; the con artists may ignore you, send you a non-functioning decryption tool, or even ask for more money after you have made the first payment. Because of this, malware analysts do not recommend establishing contact and paying the ransom.
Preventing a the RansomPlus Ransomware Infection
The most common way of ensuring that the corrupted files containing the RansomPlus Ransomware enter a computer is by disguising them as something else. In most cases, the RansomPlus Ransomware will be delivered by using social engineering techniques to trick computer users into opening a corrupted email attachment. For example, the victim may receive an email that seems to have been sent from a social media platform such as Facebook or Twitter asking them to click on a link or an email from PayPal or Amazon claiming to contain an invoice or an update to the terms of service. The attached file may be a Microsoft Word file or a PDF, both file formats that computer users may not associate with a threat. However, the attached file often contains corrupted scripts that run unsafe code on the victim's computer, connecting to a remote server and downloading and installing the RansomPlus Ransomware.
Dealing with the RansomPlus Ransomware Infection
Although a reliable security program will be able to detect and remove the RansomPlus Ransomware, the real problem is dealing with the files that are compromised during the attack. Because of this, the best recovery method involves restoring the affected files from the backup copy after the RansomPlus Ransomware has been removed. In most cases, computer users will prefer to reinstall Windows or wipe their hard drives before restoring it from a disk image or a backup, if this is a viable option, especially in the case of a compromised server.
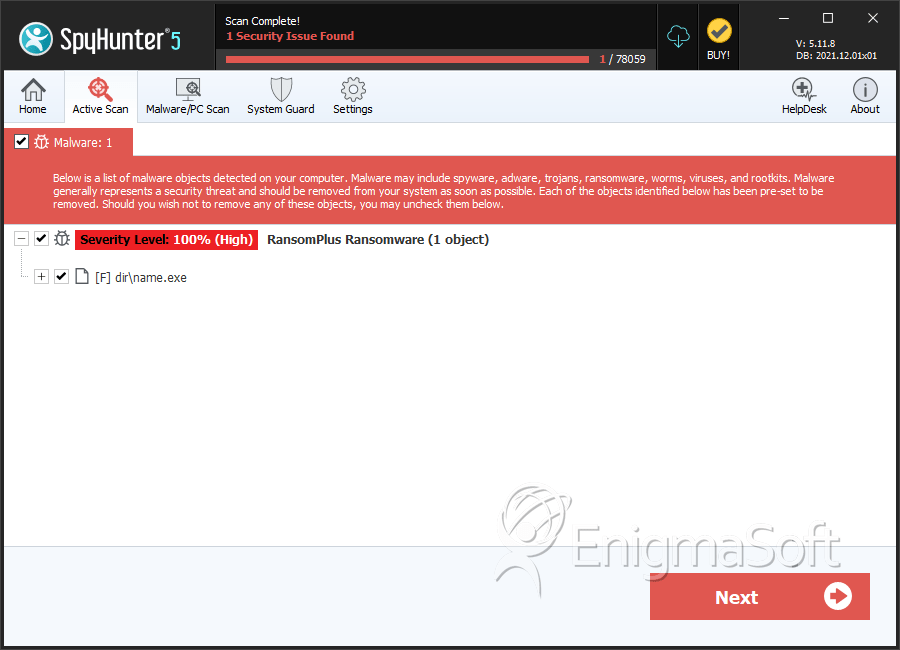
SpyHunter Detects & Remove RansomPlus Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | name.exe | 729871063d04ce837b6b65a57f4a2153 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.