RanRans Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | July 10, 2017 |
| Last Seen: | April 18, 2018 |
| OS(es) Affected: | Windows |
The RanRans Ransomware is an encryption ransomware Trojan that is used to encrypt the victims' files to demand the payment of a ransom. Although PC security analysts reported on a threat named RanRan Ransomware (also known as the zXz File Extension Ransomware) earlier in 2017, the RanRans Ransomware should not be confused with this threat. The RanRans Ransomware seems to be an independent ransomware Trojan, based on the HiddenTear open source ransomware engine that has been the basis for so many encryption ransomware Trojans that are active today. The most common way in which the RanRans Ransomware may be delivered to victims is through the use of corrupted Microsoft Word documents that use macro scripts to download and install the RanRans Ransomware onto the victim's computer. These documents may be included in spam email messages sent to victims of the attack. Having macro scripts enabled will allow the RanRans Ransomware to be installed, and many computer users may allow its installation by ignoring a User Account Control prompt. The RanRans Ransomware also has been distributed by packaging it with 'Crack Me.exe,' a file that was included in a torrent file shared on peer-to-peer file sharing networks. These are common sources for file infections, preying on inexperienced computer users searching for copyrighted content illegally.
Table of Contents
The Powerful Encryption Used by the RanRans Ransomware
The RanRans Ransomware is rooted on HiddenTear. HiddenTear is an open source ransomware program that was made public in the Summer of 2015. Since its initial release, for educational purposes, con artists to create countless ransomware variants, which have been responsible for a large percentage of ransomware infections worldwide since then, have adapted this ransomware engine. Like most other ransomware Trojans, the main goal of the RanRans Ransomware is to encrypt its victims' files, then demand that the victim pays a large ransom to recover the affected files. During the attack, the RanRans Ransomware will create a list of files on the victim's computer to be targeted with the RanRans Ransomware's encryption algorithm. Once this list is created, the RanRans Ransomware will use a strong encryption algorithm to make the files inaccessible, marking them with the file extension '.ransrans.' The files encrypted by the RanRans Ransomware will become inaccessible.
How the People Responsible for the RanRans Ransomware may Profit from the Infection
The RanRans Ransomware will demand a ransom payment from the victim after the files have been encrypted. To do this, the RanRans Ransomware will display a ransom note on the infected computer. This ransom note will include contact information, instructions on how to pay, and basic information on the nature of the attack. The RanRans Ransomware's ransom note is contained in a text file named 'READ_IT.txt' that is dropped at various locations on the infected computer. The following is the text of the RanRans Ransomware ransom note:
'Please send 50$ in Bitcoin to this Address : 1EkL3c68MY5MvchU4FHRYCjEj4DKAerG9
With Blockchain : [PAYMENT PAGE]
Sign up on blockchains.info or some other website and send the payment.
What's BTC? [A PAGE ON WIKIPEDIA]
Download Decrypt Tool : [LINK 1] or [LINK 2] or [LINK 3]
Once paid you will have your key for Restore your file.
Please Send your email as comment with the name of your computer when you send the Payment'
Dealing with the RanRans Ransomwar
Considering that the RanRans Ransomware demands a ransom amount lower than many other ransomware Trojans considerably, many computer users may be tempted to pay the RanRans Ransomware ransom amount. However, PC security researchers strongly advise against this course of action. Paying these ransoms may not result in anything good. The con artists may ignore the payments or target the victims who pay for additional infections and other tactics frequently. Furthermore, giving these peoples money allows them to continue to carry out these attacks on other innocent computer users. Instead of paying the RanRans Ransomware ransom, computer users should have file backups, which can allow computer users to get back their files after an attack.
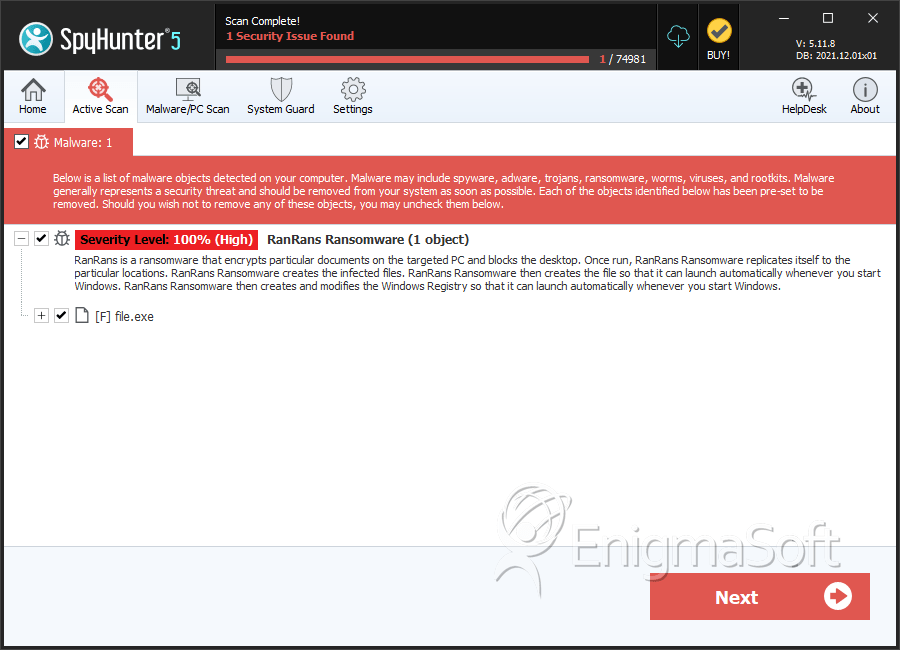
SpyHunter Detects & Remove RanRans Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 7774a30be28a49f293bba343f3b3409c | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.