QuakeWay Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | June 26, 2017 |
| Last Seen: | April 18, 2018 |
| OS(es) Affected: | Windows |
The QuakeWay Ransomware is a ransomware Trojan that is designed to encrypt the victims' files, as a way to demand ransom payments from them. The QuakeWay Ransomware takes the victims' files hostage and then demands a payment to provide the decryption key required to recover the affected files. PC security analysts advise computer users to refrain from paying the QuakeWay Ransomware ransom.
Table of Contents
This QuakeWay Leads to the Installation of a Threat on Your PC
The QuakeWay Ransomware is written using the AutoIt computer language. The QuakeWay Ransomware is designed to target individual computer users (rather than businesses or Web servers). The most common way of distributing the QuakeWay Ransomware is by delivering it through a corrupted spam email attachment. When the victim downloads the email attachment, the document will use corrupted scripts and macros to download and install the QuakeWay Ransomware onto the victim's computer. The email messages used to distribute threats like the QuakeWay Ransomware will use social engineering techniques, such as impersonating emails from a bank or a credible business (in an attempt to trick the victim into opening the attached file).
How the QuakeWay Ransomware Attack Works
There is little to differentiate the QuakeWay Ransomware from other ransomware Trojans. The QuakeWay Ransomware will scan the infected computer in search for certain file types, looking for file types with certain extensions. After encrypting them, the QuakeWay Ransomware will display a ransom note, which demands a ransom payment from the victim. The QuakeWay Ransomware's ransom note is dropped on the infected computer's Desktop in a text file named '__iWasHere.txt.' This file demands that the victim contacts the con artists at the email address 'quakeway@mail.ru' to receive the decryption key to recover the affected files.
The QuakeWay Ransomware Ransom Note
Since the QuakeWay Ransomware uses a combination of the RSA and AES encryption algorithms, it is not possible to recover the files encrypted by the QuakeWay Ransomware attack currently. The QuakeWay Ransomware will mark the files encrypted by the attack with the file extension '.org,' which will be added to each file the QuakeWay Ransomware manages to compromise. In its attack, the QuakeWay Ransomware will target the user-generated files, which may include media files, audio, video, photos, and a wide variety of file types associated with software such as Libre Office, Microsoft Office, Adobe Photoshop, 7Zip, Adobe Acrobat, AutoCAD, etc. After encrypting the victim's files, the QuakeWay Ransomware demands a ransom payment by dropping a text file on the infected computer. The full text of the QuakeWay Ransomware ransom note reads:
'===> Your files content changed to unreadable content to you and your PC, For restore operation send an email to quakeway@mail.ru and send your UID came bellow as mail subject you will get back all of your files by instruction as our reply.
===> WARNING !!!Dont be stupid to delete this TXT file(or any change on your locked folder),else YOUR FILES WILL BE CORRUPT AND CANNOT BE RESTORED ANYWAY! EVEN BY INSERT TRUE CODE !
===> ATTENTION !!This is not a Ransomware. We don't need your money Just wanna care you and upgrade your security.
Your System UID for email it is -->> [EDITED]: [EDITED] <-- We answer it during 7 days.'
Dealing with the QuakeWay Ransomware Infection
PC security researchers strongly advise computer users to refrain from paying the QuakeWay Ransomware ransom. There is no guarantee that the people responsible for the QuakeWay Ransomware attack will deliver the decryption key necessary to recover the affected files. Furthermore, paying the QuakeWay Ransomware ransom simply enables the people responsible for the QuakeWay Ransomware attack to continue creating these infections. Instead of paying the QuakeWay Ransomware ransom, you should have file backups on an external memory device. The ability to recover the files encrypted in the QuakeWay Ransomware attack is the best protection against the QuakeWay Ransomware and other ransomware Trojans that may use a similar strategy to attack your computer.
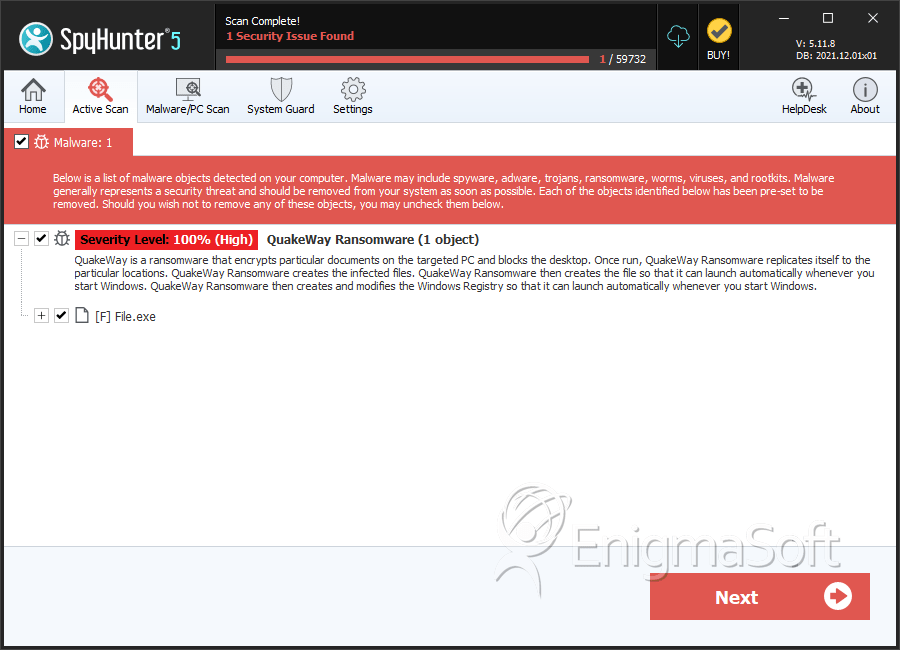
SpyHunter Detects & Remove QuakeWay Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | File.exe | 82e1295d92903394972cd466e9c04062 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.