PTP Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
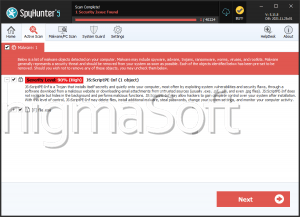
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | August 20, 2018 |
| Last Seen: | August 29, 2018 |
| OS(es) Affected: | Windows |
The PTP Ransomware is an encryption ransomware Trojan. The PTP Ransomware is one of the many variants of HiddenTear, an open source encryption ransomware platform that has been around since August 2015. The PTP Ransomware variant was first observed on August 8, 2018. It is likely that the PTP Ransomware is still in development since there are aspects of the PTP Ransomware that seem unfinished. The PTP Ransomware's code makes it likely that criminals located in South Korea developed the PTP Ransomware.
The Objective of the PTP Ransomware is to Extort Its Victims
The PTP Ransomware carries out a typical version of the encryption ransomware tactic, taking over the victims' computers and their files hostage. To do this, the PTP Ransomware uses the AES 256 encryption to make the victim's files inaccessible and then delivers a ransom note to ask the victim to pay a large amount of money to recover access to the compromised files. The PTP Ransomware targets the user-generated files in its attack, which may include a wide variety of media files, documents, databases, and numerous other file types. The files typically compromised in attacks like the PTP Ransomware include:
.ebd, .jbc, .pst, .ost, .tib, .tbk, .bak, .bac, .abk, .as4, .asd, .ashbak, .backup, .bck, .bdb, .bk1, .bkc, .bkf, .bkp, .boe, .bpa, .bpd, .bup, .cmb, .fbf, .fbw, .fh, .ful, .gho, .ipd, .nb7, .nba, .nbd, .nbf, .nbi, .nbu, .nco, .oeb, .old, .qic, .sn1, .sn2, .sna, .spi, .stg, .uci, .win, .xbk, .iso, .htm, .html, .mht, .p7, .p7c, .pem, .sgn, .sec, .cer, .csr, .djvu, .der, .stl, .crt, .p7b, .pfx, .fb, .fb2, .tif, .tiff, .pdf, .doc, .docx, .docm, .rtf, .xls, .xlsx, .xlsm, .ppt, .pptx, .ppsx, .txt, .cdr, .jpe, .jpg, .jpeg, .png, .bmp, .jiff, .jpf, .ply, .pov, .raw, .cf, .cfn, .tbn, .xcf, .xof, .key, .eml, .tbb, .dwf, .egg, .fc2, .fcz, .fg, .fp3, .pab, .oab, .psd, .psb, .pcx, .dwg, .dws, .dxe, .zip, .zipx, .7z, .rar, .rev, .afp, .bfa, .bpk, .bsk, .enc, .rzk, .rzx, .sef, .shy, .snk, .accdb, .ldf, .accdc, .adp, .dbc, .dbx, .dbf, .dbt, .dxl, .edb, .eql, .mdb, .mxl, .mdf, .sql, .sqlite, .sqlite3, .sqlitedb, .kdb, .kdbx, .1cd, .dt, .erf, .lgp, .md, .epf, .efb, .eis, .efn, .emd, .emr, .end, .eog, .erb, .ebn, .ebb, .prefab, .jif, .wor, .csv, .msg, .msf, .kwm, .pwm, .ai, .eps, .abd, .repx, .oxps, .dot.
The PTP Ransomware marks the files encrypted by its attack by adding the file extension '.PTPRansomware' to the end of the file's name. Once the PTP Ransomware has finished encrypting the victim's files, the PTP Ransomware will deliver a ransom note to the victim's computer. This ransom note is contained in a text file named 'READ_IT.TXT,' which is dropped on the infected computer's desktop and various other locations on the infected PC. The PTP Ransomware ransom note contains the following message written in Korean and English:
'Made by KimApple,
You have been infected with the PTP Ransomware
The file was sucked into construction
the PTP Ransomware will come back
work hard
The computer has become a fool
Discord : KimApple#1159'
It seems that the creators of the English version of the PTP Ransomware ransom note translated it from Korean to English using the Google Translate or similar tool because the PTP Ransomware ransom note displays poor grammar and syntax.
Protecting Your Data from Threats Like the PTP Ransomware
The best protection from threats like the PTP Ransomware is to have file backups. Having file backups allows computer users to restore their files after an attack without having to pay a ransom or contact the criminals responsible for the PTP Ransomware attack. Apart from file backups, PC security researchers strongly advise computer users to have a reliable security program that is fully up to date installed, which can prevent threats like the PTP Ransomware from being installed or remove this threat if it has already been installed. However, the PTP Ransomware encrypts the files in a way that they will not be recoverable without the decryption key.