ProLock Ransomware
The ProLock Ransomware is one of the more recent data-encrypting crypto-viruses circulating the Web and looking for victims. Having first sprung into action in late 2019 under the PwndLocker moniker, the crypto-virus underwent a major code overhaul in March 2020 after security analysts had managed to crack PwndLocker’s encryption algorithm. PwndLocker has since operated as ProLock because the revamped ransomware tool started appending the “.ProLock” extension to each encrypted file in what appears to be a multi-level encryption process. More recently, ProLock has shifted its focus on bigger targets — government entities, financial institutions, retail businesses, and healthcare organizations — in an attempt to extort exorbitant amounts of money ranging from 35 to a whopping 225 Bitcoin.
Victims are told to pay the ransom quickly, or they run the risk of losing the key, which hackers only keep for a month. Hackers also claim they stole sensitive information, and they will share it if the ransom goes unpaid. With attacks like this, the only people who can undo the damage caused by the ransomware are the people who created it. Unfortunately, there are no guarantees that they will send the decryption key if they receive their payment. Security experts say that you should never pay a ransom. It may be possible to restore lost files using a backup or using data recovery tools.
Table of Contents
ProLock Propagation Methods
Although ProLock's distribution methods had been elusive initially, subsequent research confirmed that the ransomware thrived most of all on corporate and government networks compromised with the infamous QakBot banking Trojan infection beforehand. The Qakbot Trojan either comes as a spam email attachment or a by-product of an earlier Emotet Trojan infection. To launch an attack, ProLock’s exploiters first look for a networked PC hosting the Qakbot Trojan. Taking advantage of the CVE-2019-0859 Windows security flaw, they acquire administrator rights and spread ProLock across the entire network through lateral movement. The latter may make its way through a domain controller, a compromised RDP, or an unsecured SMB protocol. Once they have seized control of the network, the crooks use Microsoft’s WMIC.exe command-line utility to launch the actual ProLock executable straight into system memory.
Apart from ProLock's association with the Qakbot banking Trojan, some experts believe that the ProLock Ransomware may also spread via vulnerable RDP (Remote Desktop Protocol) utilities like the TeamViewer application. However, it is not unlikely that other infection vectors may be at play too – bogus pirated copies of popular software tools, mass spam email campaigns, malvertising, etc.
Encryption
Like other Ransomware threats out there, ProLock targets all kinds of files, including documents, images, videos, and many others - .pdf, .doc, .docx, .xls, .xlsx, .png, .jpg, .jpeg, .mp3, .mp4, .mov, .ppt, .pptx, .rar, .gif. Unlike its counterparts, however, ProLock applies a somewhat peculiar encryption algorithm that only encrypts a portion of a file while leaving the first 8 kilobytes of its size intact. Moreover, files smaller than 8 kilobytes in size emerge unscathed from the encryption, i.e., ProLock ignores them. In the end, the victim's files get the ".ProLock" appendix. Albeit partially readable, the files remain unusable nonetheless. Plus, they will have an additional extension at the end of the names of the encrypted files – ‘.ProLock.’ Therefore, a file named ‘small-paw.jpg’ prior to the attack will be renamed to ‘small-paw.jpg.ProLock’ in the aftermath.
Alas, the unique partial encryption algorithm eventually backfired as those victims who agreed to pay the ransom got a faulty decryption tool in return.
Ransom Note and Demands
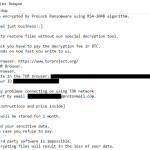
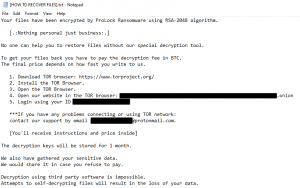
Following encryption, the ransomware places a ransom note into infected folders and on the desktop. Titled ‘[HOW TO RECOVER FILES].txt.’, the ransom note explains that the encryption applied an unbreakable RSA-2048 algorithm.
The crooks also pledge to store the decryption key for a month, giving the victim 30 days to submit the payment unless they are willing to part with their data for good. Finally, they offer to demand lower compensation should the victim agree to an immediate payment.
The threat actors behind the attack can be contacted through their TOR-based website or by the email address provided in the note.
The ransom note reads:
Your files have been encrypted by ProLock Ransomware using RSA-2048 algorithm.
[.:Nothing personal just business:.]
No one can help you to restore files without our special decryption tool.
To get your files back you have to pay the decryption fee in BTC.
The final price depends on how fast you write to us.
1. Download TOR browser: hxxps://www.torproject.org/
2. Install the TOR Browser.
3. Open the TOR Browser.
4. Open our website in the TOR browser: msaoyrayohnp32tcgwcanhjouetb5k54aekgnwg7dcvtgtecpumrxpqd.onion
5. Login using your ID -
***If you have any problems connecting or using TOR network:
contact our support by email support981723721@protonmail.com
[You'll receive instructions and price inside]
The decryption keys will be stored for 1 month.
We also have gathered your sensitive data.
We would share it in case you refuse to pay.
Decryption using third party software is impossible.
Attempts to self-decrypting files will result in the loss of your data.
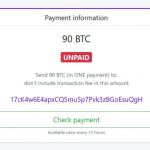
The actual size of the required ransom amount won't show up unless the victims follow the steps outlined in the note above. Once they have done that, they see another window containing the ransom amount and the Bitcoin payment account. The ransom amount may vary from 35BTC to 225 BTC, depending on the targeted entity. Here is what the payment note looks like:
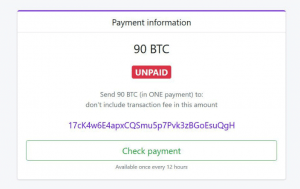
Image Source: ZDNet
Ransomware threats are among the nastiest threats that may cross your path. They infiltrate your machine, locate your files, encrypt them, and then extort you for money. Speaking of money, you should never submit any funds whatsoever. This advice is all the more valid for ProLock, as many of its victims who paid the ransom ended up getting a faulty decryptor. There’s NEVER a guarantee that the hacker will give you the decryption key they promise. It's best to maintain a trusted antivirus program and keep regular backups of your data. That way, you always have a backup and don’t need to worry about data loss.