PornBlackmailer Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 17,038 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 79 |
| First Seen: | January 31, 2018 |
| Last Seen: | September 16, 2023 |
| OS(es) Affected: | Windows |
The PornBlackmailer Ransomware is a threat infection that is used to blackmail computer users. The PornBlackmailer Ransomware has been distributed to computer users downloading pornographic video clips from xvideos, a popular pornographic website. The PornBlackmailer Ransomware attack is simple, and typical of police ransomware Trojans, a category of threats that threaten to report the victim to the police or impersonate a message from the police in its attack. The PornBlackmailer Ransomware displays a screenshot of the victim's computer's desktop and displays a threatening message.
Table of Contents
The PornBlackmailer Ransomware and Its Scary Threat
Computer users first reported the PornBlackmailer Ransomware attack through Reddit, asking for advice on how to remove the PornBlackmailer Ransomware Trojan. These threats do not encrypt the victim's files, unlike most ransomware Trojans active today. Instead, the PornBlackmailer Ransomware will display a note with a ransom demand, blackmailing the victim after the victim's computer starts up. The PornBlackmailer Ransomware is a simple tactic that relies on scaring the victims, rather than any advanced technology in the attack. The PornBlackmailer Ransomware is not capable of encrypting the victims' files. The PornBlackmailer Ransomware is also not capable of communicating with a remote server. The extortion message that the PornBlackmailer Ransomware displays on the infected computer reads:
'This is not joke! Your data will indeed be sent to POLICE departments with help of email if you do not send 0.01 BTC. All process is fully automatic. Believe me, these pennies do not cost 1 or more years in jail.
-->> Send 0.01 BTC to this address 1LoUuj2EkqSiP5U1ejw8KR56dfopgSJuw4 (specially generated for you) -->> Send 0.01 BTC to this address 1LoUuj2EkqSiP5U1ejw8KR56dfopgSJuw4 (specially generated for you) -->> Send 0.01 BTC to this address 1LoUuj2EkqSiP5U1ejw8KR56dfopgSJuw4 (specially generated for you)
If you do not pay, then tomorrow at exactly 2:56:15 AM o'clock your data will be automatically sent to the police emails and posted to public forums. If you don't know how to buy bitcoin, just type to google "How to buy bitcoins?".
The script on the server will automatically delete your data after the payment is received on the wallet.'
One aspect of the PornBlackmailer Ransomware that has caught the attention of PC security researchers is that it seems capable of avoiding various anti-malware programs commonly used today. It is likely that PC security researchers will update anti-virus software with capabilities to remove the PornBlackmailer Ransomware and similar threats if they didn't do so already.
Further Information about a PornBlackmailer Ransomware Attack
PC security researchers have found three variants of the PornBlackmailer Ransomware, with the first of these having been uploaded to the pornographic website in question on January 8, 2018. As soon as the PornBlackmailer Ransomware is installed on the victim's computer, the PornBlackmailer Ransomware will create a directory on the victim's computer that includes information such as the victim's browser history and four different screenshots of the infected PC's desktop. The PornBlackmailer Ransomware also will gather information about the infected computer, which may include the computer and account name and IP and MAC address. The PornBlackmailer Ransomware saves this information in a text file named 'your_information.txt.' The PornBlackmailer Ransomware also will attempt to create an image of the victim's location using Google Maps, saving this image in a file named 'your_location.jpg.' The PornBlackmailer Ransomware lists the affected browser's cookie files, saving it in a different directory. Finally, the PornBlackmailer Ransomware generates text files named 'READ_ME.txt,' which contain the PornBlackmailer Ransomware's threatening message. Computer users visiting the pornographic websites that are affected by the PornBlackmailer Ransomware may believe its claims of having been 'caught in the act.' The PornBlackmailer Ransomware will accuse them of viewing pornographic images and videos involving children, and demand a large ransom by threatening to report the victims to the police and send them to jail. Inexperienced computer users, who may not have experience with ransomware and extortionware, may believe these claims and be tempted to pay the PornBlackmailer Ransomware ransom amount.
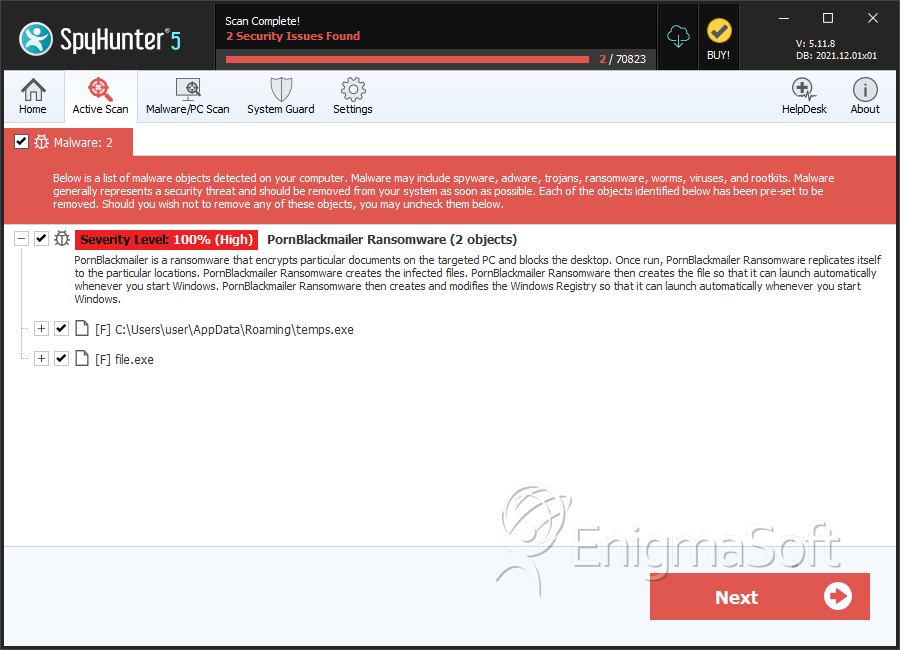
SpyHunter Detects & Remove PornBlackmailer Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | temps.exe | eff93c4f284e5021d26010949276943f | 2 |
| 2. | file.exe | 2c1ffe8e1e51b0d6780ef1f0f83acf69 | 0 |
| 3. | file.exe | 8b75eb8c2a4e5abafc95d7593c0daeed | 0 |
| 4. | file.exe | 89b85515963c27c13d3dfb6cc98d002e | 0 |
| 5. | file.exe | 53410f3585c0b255e35bb025361b50e2 | 0 |

