Payransom500 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
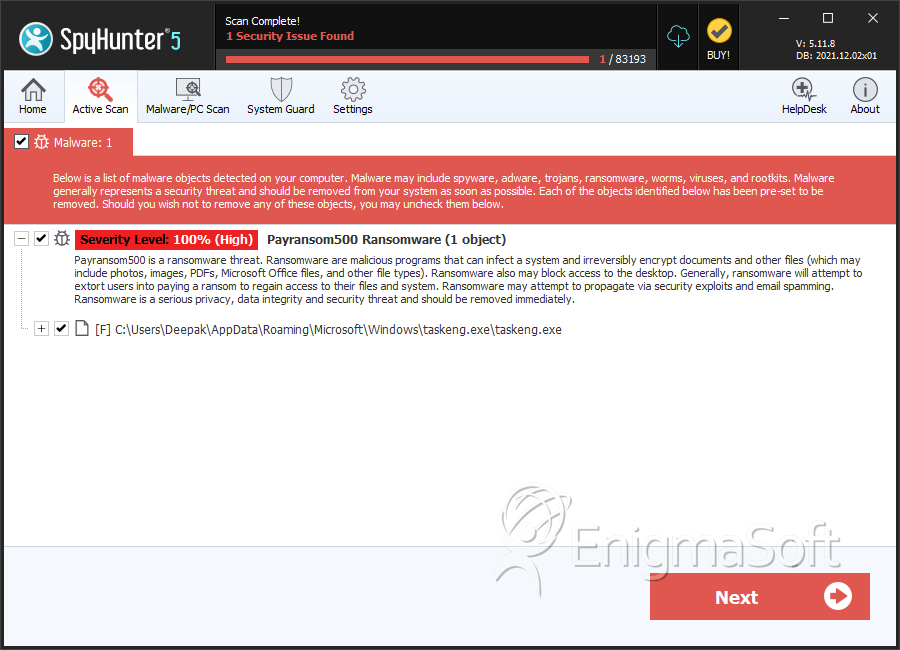
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 134 |
| First Seen: | October 7, 2021 |
| OS(es) Affected: | Windows |
Payransom500 is a ransomware threat that has been detected in the wild. The malware is capable of locking numerous file types, and the use of a strong encryption algorithm ensures that victims will not be able to restore their data on their own. In most ransomware attacks, victims who wish to receive the necessary decryption key and software tool will need to contact the hackers and pay the demanded ransom.
When Payransom500 locks a file, it will append '@payransom500' followed by an ID number assigned to the specific victim to the original filename as a new extension. The final step of the threat's functionality is to deliver a ransom note to the compromised system. The ransom-demanding message will be contained inside a text file named '!!! ALL YOUR FILES ARE ENCRYPTED !!!.TXT.'
Table of Contents
Ransom Note’s Details
According to the instructions left behind by the threat, victims will have to pay the sum of $500. The money must be transferred to the provided crypto-wallet address using the Bitcoin cryptocurrency. Users affected by the Payransom500 Ransomware are allowed to send a single locked file to be decrypted for free. To contact the cybercriminals, users can message the email address and Telegram account mentioned in the ransom note - 'payransom500@mail2tor.com' and '@payransom500.'
The full text of the ransom note is:
'!!! ALL YOUR FILES ARE ENCRYPTED !!!
All your files, documents, photos, databases and other important files are encrypted.
You are not able to decrypt it by yourself! The only method of recovering files is to purchase an unique private key.
Only we can give you this key and only we can recover your files.To be sure we have the decryptor and it works you can send an email: payransom500@mail2tor.com and decrypt one file for free.
But this file should be of not valuable!Do you really want to restore your files?
Write to email: payransom500@mail2tor.com
Telegram @payransom500Btc 500$ adress -
Your personal ID: -
Attention!Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.'
SpyHunter Detects & Remove Payransom500 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | taskeng.exe | 86d11b31007a713ce45399c288250e13 | 134 |


