Paaa Ransomware
Cybersecurity researchers identified the Paaa Ransomware during their investigation of potentially harmful software. This ransomware employs encryption techniques to lock victims out of their files. Additionally, it alters file names by adding the '.paaa' extension to each affected file and leaves behind a ransom note named '!!!README!!!.txt' containing the attackers' demands.
For instance, when Paaa infects a system, it modifies filenames by appending '.paaa' to them, like changing '1.pdf' to '1.pdf.paaa' and '2.jpg' to '2.jpg.paaa'. It's important to recognize that the Paaa Ransomware belongs to the STOP/Djvu malware family. STOP/Djvu threats have been known to accompany information-stealing malware like RedLine or Vidar when infecting devices.
The Paaa Ransomware may Cause Serious Disruptions by Locking Valuable Data
The ransom note left by the Paaa Ransomware enlightens the victims that their files have been encrypted and are inaccessible. It instructs them to purchase a decryption tool and corresponding key to regain access to their files. The note mentions that the attackers will decrypt one file as proof of their ability. The demanded ransom amount for the decryption software is $1999, but if the victim contacts the attackers within 72 hours, a 50% discount is offered.
Emphasizing the urgency, the ransom note stresses that data recovery is impossible without payment and provides two email addresses (support@freshingmail.top and datarestorehelpyou@airmail.cc) for communication with the attackers.
The process of file encryption carried out by the STOP/Djvu Ransomware involves complex actions. It begins with the execution of multi-stage shellcodes to initiate encryption. To evade detection by security tools, the ransomware dynamically resolves APIs and incorporates looping techniques to prolong its operation. Furthermore, the STOP/Djvu Ransomware employs process hollowing, a tactic that disguises itself as a legitimate process to evade detection and termination.
Typically, ransomware encrypts files and then demands payment in exchange for decryption instructions and tools. It's common for attackers to rename encrypted files and request payment in cryptocurrency to avoid traceability. Decrypting files without the involvement of cybercriminals is usually impractical due to the encryption methods used.
Despite the urgency created by ransomware attacks, it is strongly advised against meeting the attackers' demands. Paying the ransom supports criminal activities and does not guarantee the successful recovery of all affected data. Victims should prioritize implementing preventive measures and seek assistance from cybersecurity professionals to mitigate the impact of ransomware attacks.
Essential Security Measures to Boost Your Defense against Ransomware Threats
Implementing essential security measures can significantly boost defense against ransomware threats. Some basic steps users can adopt to protect their systems and data:
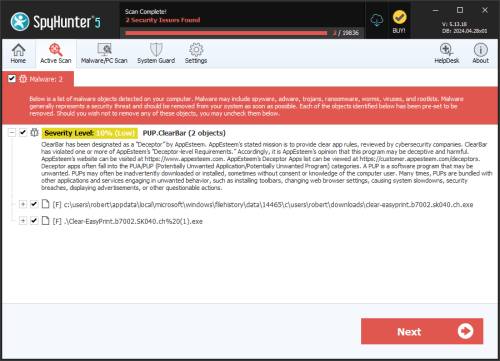
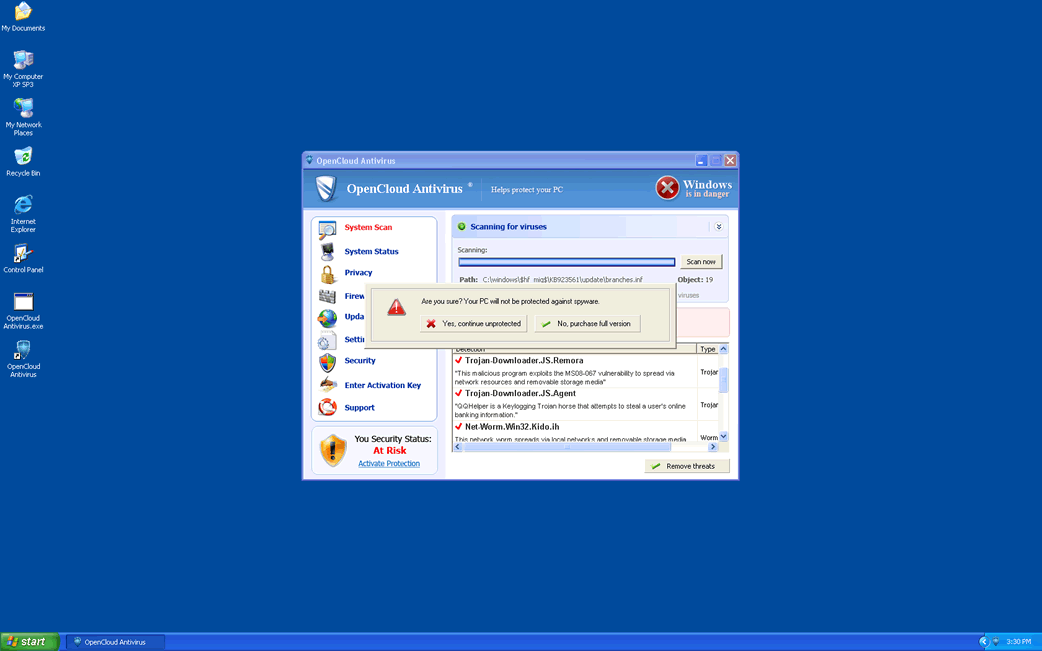
- Install and Maintain Anti-malware Software: Use reputable anti-malware software on all devices. Ensure it is regularly upgraded to detect and block known ransomware threats.
- Keep Updated Operating Systems and Software: Apply available security patches regularly and updates to your operating system, software applications and plugins. Vulnerabilities in out-of-date software can be exploited by ransomware.
- Enable Firewall Protection: Activate and configure firewalls on your devices and network routers. Firewalls observe and control network traffic (incoming and outgoing), providing an additional layer of defense against ransomware.
- Use Email and Web Filtering: Employ email and Web filtering solutions to block threatening attachments, links, and websites commonly used to distribute ransomware via phishing attacks.
- Backup Data Regularly and Securely: Maintain regular backups of critical data on external storage devices or cloud services. Ensure backups are encrypted and stored securely to prevent them from being targeted by ransomware.
- Educate and Train Users: Conduct cybersecurity awareness training for all users to recognize phishing emails, suspicious links, and other common tactics used by ransomware attackers.
- Implement Least Privilege Access: Limit user permissions and privileges to only what is necessary for their roles. Restricting access can help prevent ransomware from spreading across the network.
- Enable Pop-up Blockers and Ad Blockers: Configure Web browsers with pop-up blockers and ad blockers to prevent fraudulent advertisements and pop-ups that may lead to ransomware infections.
- Control and Analyze Network Traffic: Use network monitoring tools to detect unusual or suspicious network activities that may be an indication that a ransomware attack is in progress.
By implementing these essential security measures and maintaining a proactive approach to cybersecurity, users can significantly enhance their defense against ransomware threats and minimize the risk of falling victim to these hurtful attacks.
The ransom note the victims of the Paaa Ransomware will get reads:
'ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
Do not ask assistants from youtube and recovery data sites for help in recovering your data.
They can use your free decryption quota and scam you.
Our contact is emails in this text document only.
You can get and look video overview decrypt tool:Price of private key and decrypt software is $1999.
Discount 50% available if you contact us first 72 hours, that's price for you is $999.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:'