Outsider Ransomware
The Outsider Ransomware is an encryption ransomware Trojan that was first observed on December 7, 2018. The Outsider Ransomware is typically delivered to victims via corrupted spam email attachments. Once installed, the Outsider Ransomware is designed to encrypt the victim's files to take them hostage, then demanding a ransom payment as a condition to return access to the compromised data.
Table of Contents
How the Outsider Ransomware Attacks a Computer
The Outsider Ransomware's attack targets a wide variety of the user-generated files, which may include media files, databases, configuration files, documents and numerous other file types. Threats like the Outsider Ransomware target the following files on their attacks:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
The Outsider Ransomware's attack marks the damaged files with the file extension '.protected,' which is added to each affected file. The Outsider Ransomware delivers a ransom note in the form of a text file named 'HOW_TO_RESTORE_FILES.txt,' which contains a message for the victim, which reads:
'! SYSTEM SECURITY ALERT !
Your SERVER was tried to be attacked
by an outsider.
Immediatly change your password, use a minimum of 8 characters in length.
All your personal files was encrypted with RSA public key (1024 bit) to SAVE them from a third party persons. Now they are ENCRYPTED and SAFE!
To RESTORE all your files back immediatly, follow this few simple steps:
1) Our SECURE-SERVER service charge a payment for file decryption and preventing damage of your SERVER by 3th party persons;
2) After your SUCCESSFUL payment, write us an E-MAIL with your unique SERVER-ID and Payment ID;
3) Receive an DECRYPTION TOOL from us back to your E-MAIL;
4) Run the tool on your SERVER and safe-decrypt all your files back to NORMAL state.
We STRONGLY RECOMMEND you NOT to use any other decryption tool, files will be LOST! Only our DECRYPTION TOOL can turn back your files.
We guarantee:
100% Successful restoring all of your files 100% Satisfaction guarantee 100% Safe and secure service
As a proof, you can send us 1 file and we will DECRYPT it for free and send it back to you.
Our E-MAIL: secureserver@memeware.net
Payment type: Bitcoin
Summ: $900
Our wallet: 1CfMU2eKnajfpnYvLbWR3m7jZRXujtx8Cm
Your SERVER-ID: [random characters]
For any questions, write us: secureserver@memeware.net'
Security experts strongly advise computer users to avoid paying the Outsider Ransomware ransom or contacting the criminals responsible for the attack. Instead, it is important to replace any files compromised in the attack by using backup copies, if available. A good security program should be used to remove the Outsider Ransomware and prevent these attacks in the future.
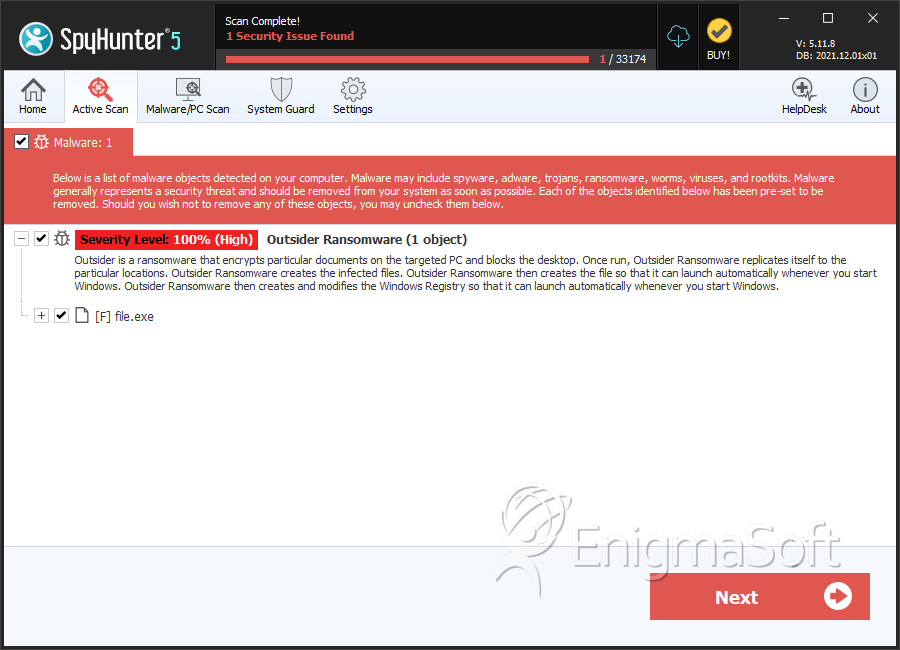
SpyHunter Detects & Remove Outsider Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 5a43d2db5c8cc3b8ec273aa470ccc931 | 0 |

