Ordinal Ransomware
The Ordinal Ransomware is an encryption ransomware Trojan that malware researchers reported on October 20, 2017. The Ordinal Ransomware is being used to attack computer users, who receive the Ordinal Ransomware as a spam email attachment. The Ordinal Ransomware will be downloaded by these attachments, which may take the form of Microsoft Office documents with corrupted macros, which install the Ordinal Ransomware when accessed. Once the Ordinal Ransomware is installed, it will encrypt the victim's files, making them inaccessible until the victim pays a ransom amount in exchange for the decryption key needed to restore the affected files.
Table of Contents
How the the Ordinal Ransomware Infection Works
The Ordinal Ransomware is one of the countless variants of HiddenTear, an open source ransomware platform that was released in August 2015. HiddenTear has spawned countless ransomware variants because it carries out an effective ransomware attack that is easy to implement and free to use for the people responsible for the attack. The Ordinal Ransomware runs as an executable file named 'main.exe' on the victim's computer, and in its attack, it will encrypt a wide variety of file types, ranging from audio and video files to office documents, databases, configuration files, archives and many others. The Ordinal Ransomware marks the files encrypted by its attack by adding the file extension '.Ordinal' to the end of each file's name. The Ordinal Ransomware's infection targets various file types, which include:
.aif, .apk, .arj, .asp, .bat, .bin, .cab, .cda, .cer, .cfg, .cfm, .cpl, .css, .csv, .cur, .dat, .deb, .dmg, .dmp, .doc, .docx, .drv, .gif, .htm, .html, .icns, .iso, .jar, .jpeg, .jpg, .jsp, .log, .mid, .mp3, .mp4, .mpa, .odp, .ods, .odt, .ogg,.part, .pdf, .php, .pkg, .png, .ppt, .pptx, .psd, .rar, .rpm, .rss, .rtf, .sql, .svg, .tar.gz, .tex, .tif, .tiff, .toast, .txt, .vcd, .wav, .wks, .wma, .wpd, .wpl, .wps, .wsf, .xlr, .xls, .xlsx, .zip.
The Costly Ransom Demand of the Ordinal Ransomware
The Ordinal Ransomware delivers its ransom note in a text file named 'READ Me To Get Your Files Back.txt,' which is dropped on the infected computer's desktop after it finishes encrypting the victim's files. The Ordinal Ransomware displays a ransom message on the infected computer, which reads:
'Ordinal Ransomware
Follow the Instructions to unlock your data
YOU FILES ARE ENCRYPTED All your files have been encrypted with AES-256 Military Grade Encryption
INSTRUCTIONS Your files have been encrypted, the only way to recover your files is to pay the fee. Once you have paid the fee all your files will be decrypted and return to normal.
Send the required fee (found below) to the Bitcoin address (found below). Once you have sent the required fee to the Bitcoin address send an email with your Identification key (without this we cant help you). It may take 12-24 hours for us to respond. You will receive a Decryption Program a Decryption Key.
WHAT NOT TO DO
DO NOT RESTART/TURNOFF YOUR COMPUTER
DO NOT ATTEMPT TO RECOVER FILES YOURSELF
DO NOT CLOSE THIS PROGRAM
DECRYPTION KEY WILL BE DELETED FROM OUR SERVERS IN 7 DAYS FROM TODAY
Amount to Send: 1.00 BTC
Contact: TEST@dprotanmail.cam
Bitcoin Address: [31 RANDOM CHARACTERS]
Identification: [8 RANDOM CHARACTERS]'
The Ordinal Ransomware's ransom demand is nearly 6,000 USD! Computer users should refrain from paying the Ordinal Ransomware ransom amount. There is no option to ch to be sure that the people responsible for the Ordinal Ransomware attack will respond and restore the affected files. They are just as likely to ignore the victim or demand even more money. Instead of paying the Ordinal Ransomware ransom, take preemptive measures to protect your files. The best protection against threats like the Ordinal Ransomware is to have a reliable backup system that allows you to restore your files from a backup copy after an attack like the one executed by the Ordinal Ransomware.
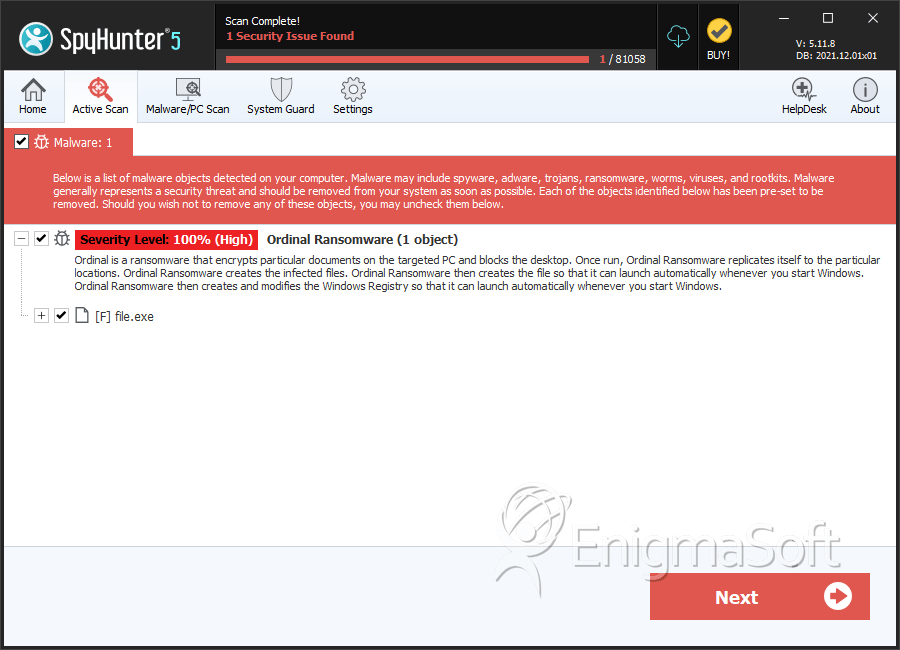
SpyHunter Detects & Remove Ordinal Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 8bcffc24d7a50cdff0c52c46a7a124fa | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.