OoPS Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
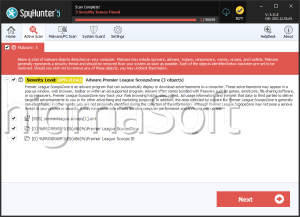
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 3,620 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 15,146 |
| First Seen: | June 5, 2017 |
| Last Seen: | October 14, 2025 |
| OS(es) Affected: | Windows |
The OoPS Ransomware is an encryption ransomware Trojan that is used to extort computer users. The OoPS Ransomware may be delivered to its victims as an attachment contained in spam email campaigns. The OoPS Ransomware is part of a large family of ransomware, with previous variants having been detected previously. The OoPS Ransomware has variants that will encrypt individual files, while other variants will place the victim's files into a password-protected archive. In both cases, the file extension used to identify the encrypted content is '.oops,' which is included to the end of the files' names. This is why the OoPS Ransomware is referred to with this name. Regretfully, as soon as the files have been encrypted in the OoPS Ransomware attack it can be nearly impossible to restore the affected files if there are no backup copies available.
Table of Contents
Uncovering the Files Targeted by the OoPS Ransomware
The OoPS Ransomware is being studied by malware researchers currently and was first observed in early June of 2017. The OoPS Ransomware uses an attack pattern typical of these threats, encrypting the victim's files using the AES encryption. As part of its attack, the OoPS Ransomware will scan the victim's computer for files with the following file extensions:
.mid, .wma, .flv, .mkv, .mov, .avi, .asf, .m peg, .vob, .mpg, .wmv, .fla, .swf, .wav, .mp3, .qcow2, .vdi, .vmdk, .vmx, .gpg, .aes, .ARC, .PAQ, .tar, .bz2, .tbk, .bak, .tar, .t z, .rar, .zip, .djv, .djvu, .svg, .bmp, .png, .gif, .raw, .com, .jpeg, .jpg, .tif, .tiff, .NEF, .psd, .cmd, .bat, .class, .jar, .java, .asp, .aspx, .brd, .sch, .dch, .dip, .vbs, .asm, .pas, .cpp, .php, .ldf, .mdf, .ibd, .MYI, .MYD, .frm, .odb, .dbf, .mdb, .sql, .SQLITEDB, .SQLITE3, .asc, .lay6, .lay, .ms11, .sldm, .sldx, .ppsm, .ppsx, .ppam, .docb, .mml, .sxm, .otg, .odg, .uop, .potx, .potm, .pptx, .pptm, .std, .sxd, .pot, .pps, .sti, .sxi, .otp, .odp, .wks, .xltx, .xltm, .xlsx, .xlsm, .xlsb, .slk, .xlw, .xlt, .xlm, .xlc, .dif, .stc, .sxc, .ots, .ods, .hwp, .dotm, .dotx, .docm, .docx, .DOT, .max, .xml, .txt, .csv, .not, .RTF, .pdf, .XLS, .PPT, .stw, .sxw, .Ott, .odt, .DOC, .pem, .csr, .crt, .key, .dat.
After making a list of the files available for encryption on the victim's computer, the OoPS Ransomware will use its encryption engine to make the files inaccessible and add the file extension '.oops' to the compromised files. The OoPS Ransomware will drop an HTML file named '_HELP_Recover_Files_.html' on the infected computer. This HTML file contains the OoPS Ransomware's ransom note, which includes the following text:
!!! IMPORTANT INFORMATION !!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about RSA and AES can be found here:
https://en.wikipedia.org/wiki/RSA_(cryptosystem)
https://en.wikipedia.org/wiki/Advanced_Encryption_Standard
Decrypting of your files is only possible with private key and decrypt program, which is on our secret server.
To receive your private key you need to make payment to us.
After you make payment run program called ‘DecryptFiles' that is located on your Desktop and your Documents.
Program will automatically decrypt all of your files!
If you try to decrypt files with another software your files can be forever lost.
How to buy decrypter?
1. You can make a payment with BitCoins, there are many methods to get them.
2. You should register BitCoin Wallet
3. Purchase Bitcoins – Althought it is not very easy to buy bitcoins, it is getting simpler every day.
Here are our recommendations:
Localbitcoins.com (WU) – Buy Bitcoins with Western Union
Coincafe.com – Recommended for fast, simple service.
Localbitcoins.com Service allows you to search for people in your community willing to sell bitcoins to you directly.
CEX.IO – Buy Bitcoins with VISA/MASTERCARD or Wire Transfer
btcdirect.eu – THE BEST FOR EUROPE
4. Send 0.2 BTC to Bitcoin address:
5. After you make payment, run program called ‘DecryptFiles'that is located on your Desktop and your Documents.
Program will automatically decrypt all of your files!'
Dealing with the OoPS Ransomware
PC security analysts advise against paying the OoPS Ransomware's ransom of 0.2 BitCoin. Instead, computer users should take preventive measures to limit the potential damage of an OoPS Ransomware infection. Just having file backups and a reliable security program that is fully up-to- date will be enough to protect your data from the OoPS Ransomware and similar threat infections entirely.
Analysis Report
General information
| Family Name: | Trojan.Kryptik.AF |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
8c538eed75265ad3de42f084dca09a32
SHA1:
08ffe113fea716b64ad94e82e06166a4c6244681
SHA256:
A034EC11AE678167C175ECE8A5AB546961C8C0D278DE3CFF3C2E3C6ABD464875
File Size:
7.14 MB, 7138304 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- HighEntropy
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 4,329 |
|---|---|
| Potentially Malicious Blocks: | 322 |
| Whitelisted Blocks: | 1,536 |
| Unknown Blocks: | 2,471 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block