Onion3Cry Ransomware
The main targets of a threat named the Onion3Cry Ransomware attacks are located in Brazil. The Onion3Cry Ransomware is probably being distributed using spam email messages, as well as fake software updates. The corrupted emails are sent out including file attachments that use macro scripts to download and install the Onion3Cry Ransomware when opened. The Onion3Cry Ransomware seems to be a variant of other encryption Trojans, particularly the Fantom Ransomware, a ransomware Trojan that was first observed in August 2016. The Onion3Cry Ransomware, in its attack, will display a fake Windows Update screen to hide the fact that the Onion3Cry Ransomware is encrypting the victim's data in the background. Once the files become encrypted, they are no longer accessible. This is the purpose of the Onion3Cry Ransomware attack; encrypt the victim's files to take them hostage and then ask the victim to pay a large amount of money for a program named 'Black decryptor,' which is needed to restore the affected files.
Table of Contents
Why an Onion3Cry Ransomware Attack can Cause So Many Trouble
The Onion3Cry Ransomware is based on HiddenTear, an open source ransomware engine that has been active since August 2015. The Onion3Cry Ransomware is just one of countless encryption ransomware Trojans based on this freely available ransomware engine. The Onion3Cry Ransomware will display a blue screen with a glowing key image and the following message in its attack:
'Obtendo atualizações
isso pode levar
alguns minutos
Verificando se ha atualizações'
Which when translated from Portuguese into English, reads as follows:
'Getting Updates
This can take
a few minutes
Checking for updates'
This screen makes the victim believe that updates are being installed. However, what is happening is that the victim's files are being encrypted in the background, with a strong encryption method. The files encrypted in the attack will be marked with the file extension '.onion3cry-open-DECRYPTMYFILES,' which will be added to the file's name. Once the Onion3Cry Ransomware finishes encrypting the targeted files, they are no longer accessible. The file types (and others) that are typically targeted in these attacks include:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Onion3Cry Ransomware and Its Ransom Demand
The Onion3Cry Ransomware will drop a text file named 'DECRYPTMYFILES.txt' on the infected computer's desktop as soon as the files have been enciphered. The full text (translated into English) of the Onion3Cry Ransomware ransom note reads:
'ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED
Our credibility at stake
To decrypt your files you need to buy the special software Black decryptor
You can find out the details / buy the decryptor + key / asks questions by email: onion33544@india.com
Unable to decode data without decoder ID: [RANDOM NUMBER]
To recover your data.
contact in up
[12H COUNTDOWN TIMER]'
Computer users are advised to not write an email to the address included in the Onion3Cry Ransomware ransom note. The people responsible for the Onion3Cry Ransomware attack are very unlikely to keep their word and help computer users restore their files. The best course of action for computer users is to take steps to make sure that their files are protected in advance. A trustable security program that is fully up-to-date, coupled with file backups is the best solution to ensure that computer users are protected.
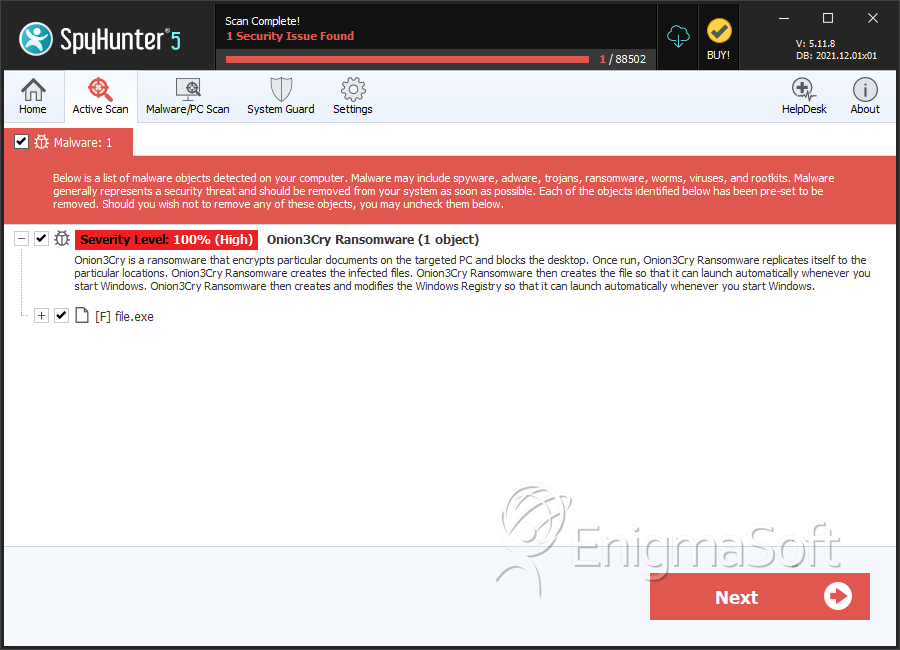
SpyHunter Detects & Remove Onion3Cry Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | a4046a44b24f172d662e01bd05ac046b | 0 |
| 2. | file.exe | 92117db6e028061b49507c9538a19a79 | 0 |

