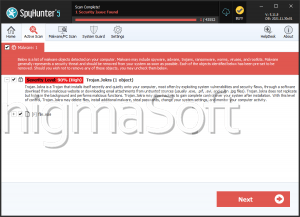
NullBulge Ransomware
The NullBulge Ransomware, a variant of the notorious LockBit.Ransomware family, has been wreaking havoc on computers worldwide. Known for its sophisticated encryption techniques and seamless ability to disrupt personal and organizational data, the NullBulge Ransomware poses a significant threat to cybersecurity.
Characteristics of the NullBulge Ransomware
Upon infection, the NullBulge Ransomware scans the victim's system for a wide range of file types, including documents, images, videos and databases. It then encrypts these files using a robust encryption algorithm, rendering them inaccessible to the user. A distinctive feature of this ransomware is that it appends a random extension to each encrypted file. For instance, a file named report.docx might be renamed to report.docx.3f9w after encryption.
After encryption, the NullBulge Ransomware generates a ransom note, named [extension].README.txt, where [extension] corresponds to the random extension appended to the encrypted files. This ransom note is strategically placed in various directories on the infected system, including the desktop, to ensure it catches the victim's attention.
The ransom note typically contains the following information:
- Notification of Encryption: The note informs the victims that their files have been encrypted.
- Personal Decryption ID: Each victim is assigned a unique DECRYPTION ID, which is essential for communication with the attackers and for any potential decryption.
- Instructions for Payment: The note provides detailed instructions on how to access a TOR site for further communication.
- Free File Decryption Offer: To demonstrate their capability and willingness to decrypt the files, the attackers offer to decrypt one file for free. This is often seen as a tactic to build trust and coerce victims into paying the ransom.
What to Do When Infected by the NullBulge Ransomware
Getting infected by ransomware can be a distressing experience, but there are critical steps you should follow to mitigate the damage and attempt recovery:
- Do not Pay the Ransom
- The ransom payment will not be a guarantee that you will be able of accesing your files. Additionally, it encourages the attackers and funds their future criminal activities.
- Disconnect from the Network
- Immediately isolate the infected system from any network to prevent the ransomware from spreading to other devices.
- Assess the Damage
- Determine which files and systems have been affected. Check the ransom note for details on the encryption and any specific instructions from the attackers.
- Report the Incident
- Report the ransomware attack to your local law enforcement agency or cybersecurity authority. Providing them with information about the attack can help in their efforts to combat such threats.
- Seek Professional Help
- Contact a cybersecurity professional or a company specializing in ransomware recovery. They can assist with the decryption of your files or restoring data from backups.
- Recover from a Backup
- If you have recent backups of your data, restore your files from these backups. Ensure that the backup is clean and not compromised by the ransomware.
- Utilize Decryption Tools
- Occasionally, cybersecurity researchers and organizations release decryption tools for certain ransomware variants. Check reputable sources such as cybersecurity forums, websites of cybersecurity firms, and organizations like for available decryption tools.
- Improve Future Security
- After dealing with the immediate threat, take steps to enhance your cybersecurity measures. This includes regular backups, keeping software and systems updated, employing robust antivirus solutions, and educating users about phishing and other common attack vectors.
The NullBulge Ransomware, a part of the LockBit Ransomware family, represents a significant threat due to its advanced encryption techniques and the psychological pressure it places on victims through its ransom note and free decryption offer. Awareness and preparedness are critical in combating such threats. By following the recommended steps, victims can mitigate the damage and enhance their defenses against future attacks. Remember, the best defense against ransomware is a combination of preventive measures, rapid response, and informed recovery strategies.
Below you will find the ransom note's diplayed bi the NullBulge Ransomware:
'NULLBULGE LOCK - BASED ON LOCKBIT~~~
>>>> Your data is encrypted... but dont freak out
If we encrypted you, you majorly f***ed up. But... all can be saved
But not for free, we require an xmr payment>>>> What guarantees that we will not deceive you?
We are not a politically motivated group and we do not need anything other than your money.
If you pay, we will provide you the programs for decryption.
Life is too short to be sad. Dont be sad money is only paper. Your files are more important than paper right?
If we do not give you decrypter then nobody will pay us in the future.
To us, our reputation is very important. There is no dissatisfied victim after payment.
>>>> You may contact us and decrypt one file for free on these TOR sites with your personal DECRYPTION ID
Download and install TOR Browser hxxps://www.torproject.org/
Write to a chat and wait for the answer, we will always answer you.
Sometimes you will need to wait a whileLinks for Tor Browser:
hxxp://nullblgtk7dwzpfklgktzll27ovvnj7pvqkoprmhubnnb32qcbmcpgid.onion/Link for the normal browser
hxxp://group.goocasino.org
hxxps://nullbulge.com>>>> Your personal DECRYPTION ID: 217B9D5D58C4AD3C58695ABBA6C6AA0B
>>>> Warning! Do not DELETE or MODIFY any files, it can lead to recovery problems!'