Nodersok
Many cyber crooks are taking an interest in hacking techniques called LOLBins (Living-Off-the-Land Binaries). This is becoming increasingly popular because it allows cybercriminals to bypass anti-malware tools as the threatening campaigns are carried out through legitimate applications and services, which helps the operators remain under the radar. Recently, malware researchers have spotted a new threat that employs the LOLBins techniques – Nodersok. The authors of this threat have gone a step further and have made sure that these techniques are executed at every phase of the attack making the Nodersok a threat, which operates very silently.
Table of Contents
Turns Compromised Machines into Proxy Servers
The creators of the Nodersok threat are using it to infect hosts and turn them into proxy servers by injecting them with a proxy script called Node.JS framework. It is not clear what they plan on doing with the infiltrated machines exactly, but it is likely that they may be used as a part of the fast-growing infrastructure of the creators of Nodersok or simply be employed in mass spam email campaigns.
Most Victims are Regular Users
The activity of the Nodersok is concentrated in the United States and Europe mainly. It has been reported that the victims are in the thousands already, which is rather impressive. Cybersecurity experts have estimated that 3% of the infected hosts belong to corporations, which means that almost all the PCs that have fallen victim to the Nodersok malware belong to regular users.
How the Attack is Carried Out
The Nodersok threat executes a few tasks as a part of its attack:
- Corrupted advertisements deliver a '.hta' file, which is hosted on a genuine cloud service to the user.
- If the user runs the file, the injected JavaScript code will trigger the download of a '.xsl' or a '.js' file.
- Once the second file infiltrates the system, it will begin a decryption process, which will unlock a PowerShell command.
- Next, the revealed PowerShell command will enable the threat to plant additional LOLBins on the host.
Additional LOLBins
If the Nodersok threat is successful and manages to download the extra LOLBins, the user may be in a upright bit of trouble as these tools include:
- The previously mentioned Node.JS framework.
- A module related to the Node.JS framework, which allows the operators to turn the host into a dormant proxy server.
- A network packets capturing kit called Windivert.
- A shellcode, which allows the attackers to gain administrator privileges on the infected host.
- A PowerShell script, which makes sure that none of the Windows security tools are functioning as long as the Nodersok malware is present on the system.
The authors of the Nodersok threat take their security very seriously and make sure to wipe out their tracks every 2-3 days by replacing the domains, which host the extra JavaScript code.
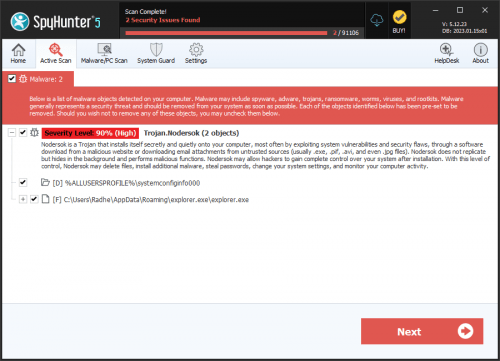
The Nodersok malware is not a threat you can take lightly. Make sure you download and install a reputable anti-virus software suite, which will help you remove the Nodersok malware from your system safely.