Ninja Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 28 |
| First Seen: | September 17, 2015 |
| Last Seen: | March 21, 2020 |
| OS(es) Affected: | Windows |
The Ninja Ransomware is a ransomware infection that is used to encrypt the victims' files to demand payment of a ransom. The Ninja Ransomware displays a message in Russian that can be particularly confusing for computer users that do not read or understand this language. One of the main dangers of the Ninja Ransomware is that it represents a threat to the computer users' data because its encryption cannot be undone without access to the decryption key. Computer users without a file back-up may be unable to recover from a Ninja Ransomware infection. Although the Ninja Ransomware is clearly Russian in origin, the Ninja Ransomware has attacked computers all over the world. The Ninja Ransomware is distributed using corrupted email messages, attack websites and similar threat delivery methods. The best ways to prevent the Ninja Ransomware attacks include the use of good online browsing habits and strong security software that is fully up-to-date.
Table of Contents
The Ninja that Attacks Your Files
The most common way of delivering the Ninja Ransomware is as a compromised file attachment contained in spam email messages. Once the Ninja Ransomware is installed on a computer, it may cause the affected computer to slow down. This may happen because the Ninja Ransomware will start searching for files that match commonly used file formats and then encrypts them. After the encryption process is over, the Ninja Ransomware displays a ransom message in Russian, changing the victim's desktop image and displaying pop-up windows. The Ninja Ransomware ransom message demands payment within a week. The Ninja Ransomware contains an email address (ninja.gaiver@aol.com) so that computer users can send one small encrypted file so that it will be decrypted. However, for computer users to decrypt the rest of their files, they will be forced to pay a large amount of money. PC security researchers strongly advise computer users to avoid paying the Ninja Ransomware ransom, since this will allow con artists to continue carrying out these kinds of attacks. Instead, computer users should restore their files from an external back-up.
The Wok of Ransomware Infections Like the Ninja Ransomware
There are numerous encryption ransomware infections like the Ninja Ransomware. These carry out similar types of attacks that may be distributed using spam email messages that try to trick inexperienced computer users into opening attached files. These types of emails are easy to recognize, although it is best for computer users to be educated so they will recognize these hoaxes for what they are. The following is the English version of the Ninja Ransomware ransom note:
Your files are encoded, if you want to get them back, send one encoded file to this address:
Ninja.gaiver@aol.com
ATTENTION!!! You have 1 week to write an email for me, once the time is over, it will be impossible to decrypt!!!!
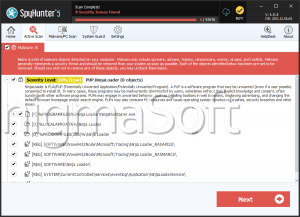
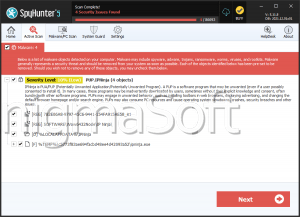
In this case, you should follow the instructions that we have provided for you and initiate and immediate Ninja ransomware removal.
Dealing with a Ninja Ransomware infection is not easy. Computer users should remove the Ninja Ransomware infection completely with the help of a reliable, fully updated security program. They should make sure that all related files are completely removed before restoring files from a backup. Otherwise, there is a significant risk of the victims' files being encrypted again. The best way to recover from a Ninja Ransomware attack is using an external backup method. These types of methods may include external memory devices or cloud storage options. A strong security application and good browsing methods can prevent exposure to further attacks. In these cases, one shouldn't underestimate the benefits of a good anti-spam filter, which would prevent these kinds of threatening emails from arriving.