Nextgensecuritylabs.co.in
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 7,223 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 21 |
| First Seen: | October 8, 2025 |
| Last Seen: | October 12, 2025 |
| OS(es) Affected: | Windows |
The internet is filled with deceptive and malicious sites that attempt to trick users into compromising their privacy or system security. Cybersecurity specialists continuously warn that even seemingly harmless websites can conceal dangerous schemes. One such rogue platform, Nextgensecuritylabs.co.in, exemplifies how scammers exploit users' trust through social engineering and misleading prompts.
Table of Contents
A Rogue Website Masquerading as Legitimate
Upon investigation, cybersecurity experts confirmed that Nextgensecuritylabs.co.in is a fraudulent site designed to mislead visitors into enabling push notifications. It relies on clickbait tactics, a form of online deception that uses enticing or alarming content to provoke user interaction.
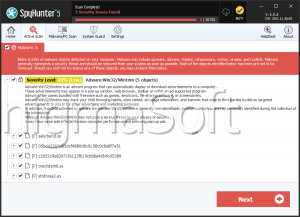
Once permission is granted, the site begins pushing intrusive notifications directly to the user's screen. These notifications often display fake security alerts or deceptive pop-ups urging the visitor to scan their system for nonexistent threats. In many cases, these alerts claim that the user's device is infected with malware or that their Gmail login details have been stolen, then prompt them to click on 'Scan,' 'Install,' or similar buttons.
Following these links may redirect users to malicious or scam-promoting pages, including sites distributing harmful software, phishing portals, or fake technical support pages designed to extract sensitive personal data.
The Fake CAPTCHA Trap
A key component of Nextgensecuritylabs.co. in's deceptive strategy is its fraudulent CAPTCHA check. The page typically shows a reCAPTCHA logo, a checkbox, and a message asking the visitor to 'verify that you are not a robot.' However, instead of performing a genuine CAPTCHA verification, the site instructs users to click the 'Allow' button in their browser's notification prompt.
This action, rather than confirming the user's humanity, grants the website permission to send notifications, effectively giving scammers a direct communication channel to the user's device. These fake CAPTCHA prompts exploit a familiar and trusted design, which makes users more likely to comply without suspicion.
Common Signs of a Fake CAPTCHA Page
To avoid falling for such tricks, users should be aware of several warning signs that suggest a CAPTCHA page is fake or malicious:
Unusual instructions – Genuine CAPTCHA tests never ask you to click 'Allow' or enable browser notifications.
Pop-ups with browser-level requests – A CAPTCHA should appear as part of a website form, not trigger permission boxes.
Poor design or grammar mistakes – Fake CAPTCHA pages often contain spelling errors, off-brand logos, or visual inconsistencies.
Unexpected redirects – If completing a CAPTCHA immediately opens new tabs or websites, it's likely fraudulent.
Alarming messages afterward – Real CAPTCHAs never follow up with fake alerts or infection warnings.
Potential Dangers and Misleading Notifications
Once Nextgensecuritylabs.co.in gains notification permissions, it can bombard users with misleading or harmful content. These messages often include fabricated system warnings and security prompts designed to:
- Convince users to download untrustworthy or malicious software.
- Redirect them to phishing websites that steal credentials.
- Encourage fake technical support payments or fraudulent transactions.
Such notifications create a false sense of urgency, pushing victims into rash decisions that compromise both privacy and financial security.
How Users End Up on Such Sites
Most users do not access pages like Nextgensecuritylabs.co.in intentionally. Instead, they are redirected through unreliable ad networks tied to pirated streaming platforms, torrent sites, or misleading advertisements. In some cases, the source may be adware installed on the user's system or spam emails containing malicious links.
Protecting Yourself from Notification Abuse
Users who have accidentally clicked 'Allow' on such rogue sites should immediately revoke notification permissions via their browser settings. It's also wise to avoid visiting suspicious domains, install reputable anti-malware software, and keep browser security features enabled to block deceptive content.
URLs
Nextgensecuritylabs.co.in may call the following URLs:
| nextgensecuritylabs.co.in |