NETCrypton Ransomware
The NETCrypton Ransomware is an encryption ransomware Trojan that was first observed on November 28, 2017. The NETCrypton Ransomware is spreading currently as a key generator for the Data Recovery Wizard, a program that is developed by EaseUS. This is a common way of delivering threats, disguising it as a software crack or key on file sharing websites or similar places. The NETCrypton Ransomware targets victims that are not willing to pay for legitimate backup tools and instead try to find pirated solutions to gaining access to this software kind specifically. The NETCrypton Ransomware functions like most encryption ransomware Trojans, taking the victim's files hostage and then demanding payment of a ransom from the victim in exchange for the decryption key necessary to restore the affected files.
Table of Contents
How the NETCrypton Ransomware Attack Works
Most ransomware Trojans carry out their attack without alerting the victim. In the case of the NETCrypton Ransomware, the victim is given the choice of executing the NETCrypton Ransomware or not, making it seem as if the NETCrypton Ransomware is part of a prank or a way to punish computer users using an illicitly copied software. The NETCrypton Ransomware, before its attack, delivers the following dialog box:
'ARE YOU SURE YOU WANT TO EXECUTE THIS RANSOMWARE?
[OK|Button] [NO|BUTTON]'
If computer users choose 'No,' then the NETCrypton Ransomware is deactivated, and it will no longer carry out its attack. Choosing 'OK' triggers the NETCrypton Ransomware attack, and this Trojan will encrypt the victim's data using a strong encryption algorithm. The NETCrypton Ransomware targets a wide variety of file types in its attack, searching for the user-generated files, which can include media files and a variety of documents. The following file types are some of the ones that are targeted by the NETCrypton Ransomware attack and similar infections:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The NETCrypton Ransomware’s Ransom Demand
The NETCrypton Ransomware runs on infected computers as 'EaseUSDataRecovery.exe.' The NETCrypton Ransomware uses a strong encryption method that makes it impossible to restore the files encrypted by the NETCrypton Ransomware attack. The NETCrypton Ransomware marks the files encrypted by the attack by adding the file extension '.encrptd' to each affected file's name. The NETCrypton Ransomware changes the infected PC's desktop image into a black screen with a red text after encrypting the victim's files. In this message, the NETCrypton Ransomware delivers the following text:
'OOPS!
Your files have been encrypted with Crypton. It was encrypted by
generating and locking your files
with a unique password.
To recover your files, you will
have to pay a fee of $300 to the
following bitcoin address:
[31 RANDOM CHARCTERS]'
It is easy to understand why computer users must refrain from paying the NETCrypton Ransomware ransom.
Dealing with a NETCrypton Ransomware Infection
If the NETCrypton Ransomware has enciphered your files, it will be necessary to remove the NETCrypton Ransomware infection with a trustable security product that is fully up-to-date. However, anti-virus programs will not restore the files encrypted by the NETCrypton Ransomware attack. This is the reason that makes file backups so necessary when protecting your data. Having file backups stored in safe places, allows computer users to restore the affected files, making the attack ineffective.
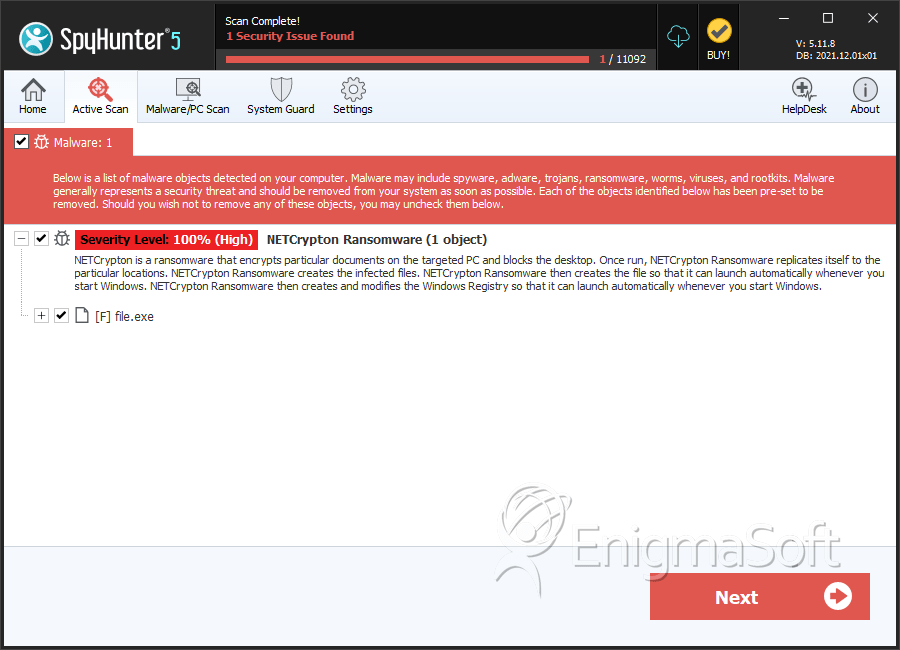
SpyHunter Detects & Remove NETCrypton Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | b60eb1590479a27ad9e2d64d81fa4a4c | 0 |

