Nemucod-AES Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 673 |
| First Seen: | April 27, 2016 |
| Last Seen: | May 3, 2023 |
| OS(es) Affected: | Windows |
The Nemucod-AES Ransomware is a variant of Nemucod, a ransomware Trojan that has been active since at least August of 2016. Malware researchers observed this new version of the old ransomware Trojan on June 30, 2017. The Nemucod-AES Ransomware may be delivered to victims through corrupted spam email attachments, which may take the form of email messages that include a corrupted attached file that uses bad scripts to infect the victim's computer. A typical example of this is a fake UPS delivery invoice file named 'UPS-Delivery-005156577.doc.js.' Note the JS extension, which is added after the DOC extension. By using a double extension and an icon for the file that impersonates the default icon for DOC files, con artists can trick computer users into downloading and executing corrupted JavaScript files and similar content that they would avoid normally.
Table of Contents
The Nemucod-AES Ransomware is an Updated Version of Another Threat
As soon as the Nemucod-AES Ransomware infects a computer, it will report on the infected computer to its Command and Control server. Some of the information that the Nemucod-AES Ransomware will gather and report about is the infected computer's Windows operating system version, the infected computer's IP address, the BIOS version and type of the infected PC, configuration and security settings, and whether or not a debugger is present on the infected computer. The Nemucod-AES Ransomware will relay this information to its Command and Control servers, which seem to be hosted on the following IP addresses as of the writing of this report:
- 118.44.99.208
- 128.172.195.141
- 161.178.56.125
- 187.9.125.102
- 19.226.208.209
- 218.33.235.57
- 223.246.43.6
- 50.39.219.180
- 65.194.82.52
- 73.112.104.144
- 75.60.48.226
It is likely that these servers will continue to change the IP addresses as known IP addresses related to the Nemucod-AES Ransomware become blocked by security software. In its attack, the Nemucod-AES Ransomware will use an encryption algorithm to make the victim's files inaccessible. The Nemucod-AES Ransomware uses the AES 256 encryption to make the victim's files inaccessible.
How Con Artists Use the Nemucod-AES Ransomware to Profit
After the Nemucod-AES Ransomware has finished encrypting the victim's files, it will display a ransom note on the victim's desktop. The Nemucod-AES Ransomware takes the victim's files hostage. The Nemucod-AES Ransomware displays a JPEG and a TXT version of its ransom note, on a document with the name 'Decrypt.txt,' which is dropped on the infected computer's desktop. The Nemucod-AES Ransomware also will change the infected computer's desktop image into a ransom note displayed over a red background. The Nemucod-AES Ransomware's ransom note contains the following text:
'ATTENTION!
All your documents, photos, databases and other important personal files were encrypted using a combination of strong RSA-2048 and AES-128 algorithms.
The only way to restore your files is to buy decryptor. Please, follow these steps:
1. Create your Bitcoin wallet here:
xxxxs://blockchain.info/wallet/new
2. Buy 0.11471 bitcoins here:
https://localbitcoins.com/buy_bitcoins
3. Send 0.11471 bitcoins to this address:
<%ADDRESS%>
4. Open one of the following links in your browser:
xxxx://elita5.md/counter/71GCn9vz73FNDmoVxgxXqjo7dSXyLmfnTDt
xxxx://artdecorfashion.com/counter/71GCn9vz73FNDmoVxgxXqjo7dSXyLmfnTDt
xxxx://goldwingclub.ru/counter/71GCn9vz73FNDmoVxgxXqjo7dSXyLmfnTDt
xxxx://perdasbasalti.it/counter/71GCn9vz73FNDmoVxgxXqjo7dSXyLmfnTDt
xxxx://natiwa.com/counter/71GCn9vz73FNDmoVxgxXqjo7dSXyLmfnTDt
5. Download and run decryptor to restore your files.
You can find this instruction in "DECRYPT" file on your desktop.'
Dealing with a Nemucod-AES Ransomware Infection
Malware analysts advocate against paying the Nemucod-AES Ransomware ransom, which currently is close to $290 USD at the current BitCoin exchange rate. The people responsible for the Nemucod-AES Ransomware may ignore the victims' payments and, furthermore, paying these ransoms merely allows these people to continue creating and distributing threats like the Nemucod-AES Ransomware by financing their activities. Instead of paying the Nemucod-AES Ransomware ransom, they should take preventive measures. Threat experts advise computer users to have file backups. Having backup copies of their files will make them immune to attacks like the Nemucod-AES Ransomware since the extortionists lose any power they have to demand a ransom payment if the victim is capable of restoring any of the compromised files from a backup copy.
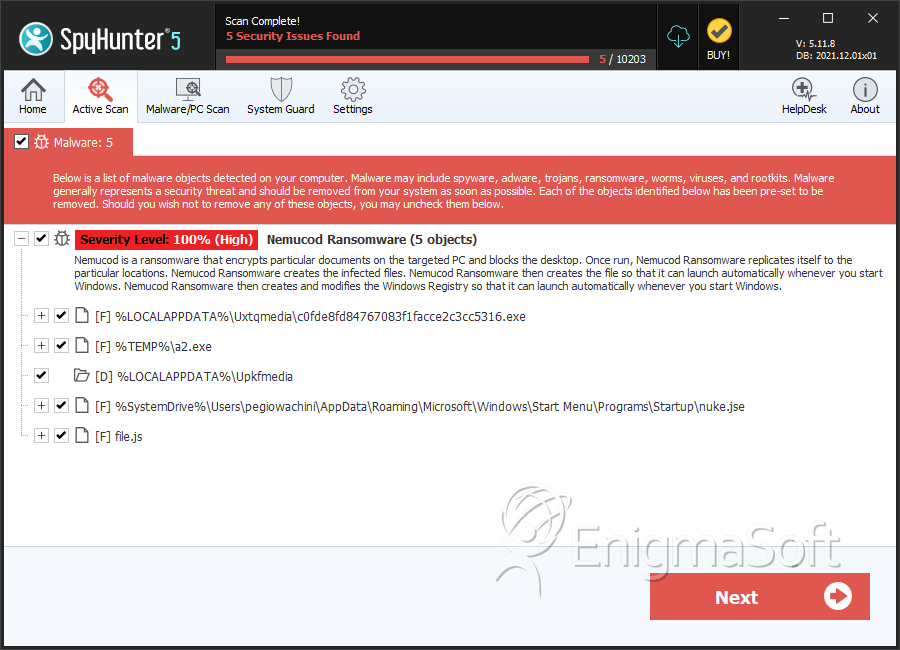
SpyHunter Detects & Remove Nemucod-AES Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | c0fde8fd84767083f1facce2c3cc5316.exe | c0fde8fd84767083f1facce2c3cc5316 | 92 |
| 2. | a2.exe | 4d0f490e3e21bef1c6f0c6fa93de90ed | 44 |
| 3. | nuke.jse | 0954e1587829390a454ec761bfae87d2 | 11 |
| 4. | nuke.jse | ba6dd9e84b54273e553dfbce81a36b02 | 5 |
| 5. | nuke.jse | 263e0c0575fde12adff9877f9fce5e59 | 4 |
| 6. | nuke.jse | a980fbe6b297e8b576cd0a5e420dc229 | 4 |
| 7. | nuke.jse | b4362a410bffbf4d71620c700c21f6cd | 4 |
| 8. | nuke.jse | 1b78a537744b7f9cdd1fe64ef1d82040 | 3 |
| 9. | nuke.jse | f6e251aefb5d094c71511c4210fe9fcd | 2 |
| 10. | nuke.jse | 256cc82c208d021d90b5a82cb0a62292 | 2 |
| 11. | nuke.jse | 2f4f06cb432169ccd4501596fe71758b | 1 |
| 12. | nuke.jse | c1a3a310327493ac13baf4c2bf9ea353 | 1 |
| 13. | nuke.jse | 0ac26e33c7d239b340d8b25ac36f5c05 | 1 |
| 14. | nuke.jse | e56ac7e5354df06673495d6da96cd8ef | 1 |
| 15. | file.js | ba44cb88fb6b3d68a0198ad29ad9f27b | 0 |
Registry Details
Directories
Nemucod-AES Ransomware may create the following directory or directories:
| %LOCALAPPDATA%\Upkfmedia |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.