Ndm448 Ransomware
The growing sophistication of modern ransomware campaigns highlights how critical it is for users and organizations to protect their devices against malware. A single successful intrusion can lead to operational disruption, financial loss, reputational damage, and exposure of sensitive information. One particularly dangerous strain currently analyzed by researchers is Ndm448 Ransomware, a highly disruptive threat that combines file encryption with data exfiltration and extortion tactics.
Table of Contents
Ndm448 Ransomware: A Makop Family Variant with Advanced Extortion Tactics
Ndm448 Ransomware has been identified as a variant of the well-known Makop ransomware family. Like other Makop-based threats, Ndm448 is engineered to infiltrate compromised systems, encrypt valuable data, and pressure victims into paying a ransom for restoration.
Once executed, the malware performs a series of coordinated actions. It encrypts files across the system, alters their filenames, drops a ransom note named '+README-WARNING+.txt,' and modifies the desktop wallpaper to ensure the victim is immediately aware of the attack. The encryption process renders files inaccessible without a corresponding decryption key held by the attackers.
File Renaming Pattern and Encryption Behavior
A defining trait of Ndm448 is its distinctive file renaming convention. After encrypting files, it appends three elements to each filename:
- The victim's unique ID
- An attacker-controlled email address
- The .ndm448 extension
For example, a file originally named '1.png' is renamed to '1.png.[2AF20FA3].[thomasandersen70@onionmail.org].ndm448,' while '2.pdf becomes 2.pdf.[2AF20FA3].[thomasandersen70@onionmail.org].ndm448.'
This structured renaming system allows attackers to identify victims individually while clearly marking encrypted data. The addition of the dedicated extension also prevents standard applications from recognizing or opening the files.
Ransom Note and Double Extortion Strategy
The ransom note provides detailed instructions and escalates psychological pressure. Victims are informed that their files have been encrypted and that sensitive data has been stolen. The attackers claim that the stolen information will be deleted, sold, or publicly disclosed if the victim fails to cooperate.
Communication is directed through the email address thomasandersen70@onionmail.org or via qTox messenger. The note emphasizes that the only way to restore access is by purchasing a proprietary decryption tool. Victims are warned against restarting systems, modifying encrypted files, or attempting third-party recovery solutions, claiming such actions could permanently damage data.
A strict deadline is imposed. If no agreement is reached within a few days, the attackers threaten to destroy decryption keys and leak the stolen information. Although payment is presented as a guarantee of recovery and data deletion, there is no assurance that attackers will honor these claims. Many ransomware operators fail to provide working decryption tools even after payment.
Infection Vectors and Distribution Methods
Ndm448 spreads through multiple delivery mechanisms designed to exploit human error and system vulnerabilities. It often infiltrates systems when users unknowingly execute malicious content disguised as legitimate files. These may include infected executables, scripts, compressed archives, or documents such as Word, Excel, and PDF files.
Common distribution channels include:
- Fraudulent email campaigns containing malicious attachments or links
- Pirated software, key generators, and cracking tools
- Exploitation of software vulnerabilities and outdated applications
- Compromised USB drives and peer-to-peer networks
- Fake technical support scams and deceptive advertisements
- Hijacked or counterfeit websites distributing trojanized downloads
These diverse entry points make ransomware like Ndm448 highly adaptable and difficult to contain once active in an environment.
The Risks of Payment and Persistent Infection
Ransomware attacks create immediate operational paralysis. Without uncompromised backups, recovery options become severely limited. However, paying the ransom is strongly discouraged. Attackers may not deliver functional decryption tools, may demand additional payments, or may still leak stolen data.
Immediate removal of the ransomware is essential. If left active, it can continue encrypting newly created files and may attempt to spread laterally across local networks, increasing the scale of damage.
Strengthening Defense: Essential Security Best Practices
Mitigating threats like Ndm448 requires a layered and disciplined security strategy. Users and organizations should implement the following core practices to significantly reduce exposure:
- Maintain regular offline or cloud-based backups that are isolated from the primary system.
- Keep operating systems and software fully updated to patch known vulnerabilities.
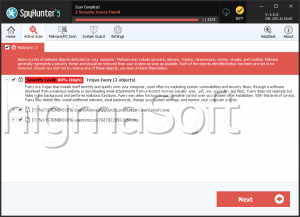
- Use reputable, real-time security solutions with ransomware detection capabilities.
- Avoid downloading pirated software or unofficial activation tools.
- Exercise caution with email attachments, links, and unsolicited communications.
- Restrict administrative privileges and apply the principle of least privilege.
- Disable macros in documents unless absolutely necessary.
- Segment networks to limit lateral movement in case of compromise.
Beyond these measures, ongoing cybersecurity awareness training plays a crucial role in reducing human-related attack vectors. Employees and individual users alike must be educated on recognizing phishing attempts, suspicious downloads, and social engineering tactics.
Conclusion
Ndm448 Ransomware exemplifies the evolution of modern ransomware into a double-extortion threat capable of encrypting data while simultaneously leveraging stolen information for additional pressure. As a member of the Makop family, it combines strong encryption techniques with aggressive psychological tactics designed to coerce payment.
Robust preventive security measures, consistent backups, and proactive threat detection remain the most effective defenses. In an environment where ransomware campaigns continue to grow in scale and sophistication, preparedness and vigilance are indispensable safeguards against devastating data loss and financial harm.