Multitimer
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 13,001 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 505 |
| First Seen: | February 12, 2024 |
| Last Seen: | May 20, 2026 |
| OS(es) Affected: | Windows |
The Multitimer software is promoted as a productivity application for Windows. The Multitimer application is said to allow users o track time zones, set countdowns, and set up events of importance. The Multitimer software comes with a GNU Free License, and PC users are not required to pay for the program. However, that does not mean it is not monetized in another form. It was found that Multitimer collects non-personally identifiable data like your Internet history, IP address, and software configuration for market development purposes. PC users who may be using the Multitimer software may see ads with the slogan 'Powered by Multitimer' on frequently visited pages.
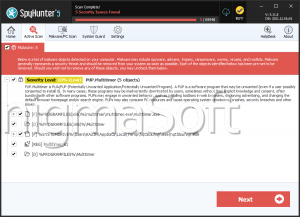
The program at hand is known to add an autorun key to the Registry and boot with Windows. There is no option to disable the Registry key created by Multitimer from within its interface, and you may need to do it manually or use tools like CCleaner and MSCONFIG. Computer security researchers classify Multitimer as a Potentially Unwanted Program (PUP) that can be found in the Program Files (x86) system directory, or it may be listed in the 'Control Panel' as 'Multitimer\version 1.0.' You can remove Multitimer and related tracking Web beacons with the help of a trusted anti-spyware scanner. AV engines use the following detection names for Multitimer:
- Adware.Tuto4PC
- PUP.Multitimer
- PUP.Optional.Multitimer
- Suspicious_GEN.F47V0127
- Suspicion: unknown virus
- UnclassifiedMalware
- W32/GenBl.EBC0B805!Olympus
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Spy.Agent.RS |
|---|---|
| Packers: | UPX |
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
c1e7a01246db29fd67a54434b8895374
SHA1:
e9229f844c36de52480d30d571c074381803a56c
SHA256:
3BF47454F9E2F1DBF5C3747ADA1A8B8FA72B0C8172B4AE16062ACC9CBB531CDA
File Size:
359.42 KB, 359424 bytes
|
|
MD5:
e9d4410a2ab6d6b6e6b5d4f117f3ca8a
SHA1:
8ea906958858b490905e393020dece0cf1a47a3b
SHA256:
AA2DCDE87B0A7C69A9DFAD966DBA1BF31238AC47234C53AFAE6EF5D11C40FE3B
File Size:
345.60 KB, 345600 bytes
|
|
MD5:
483cb41dbef9a47a5f4e409480759b1a
SHA1:
2fbe06a703e023cb19967975569c3b683e4fb26f
SHA256:
74741D4CDF8ACDE8BAACA11DBE269F92B33B004F29CEA9FA1C191BA2E7C1DBEA
File Size:
344.58 KB, 344576 bytes
|
|
MD5:
5a8e77a216121a2c5a8209135bd465d9
SHA1:
48c8a486a8468b0df3344324355532baaacd6a60
SHA256:
FB2A82CF7AC9ADA2C3641DCCF5010CACFEC19E87EB6EBB013197D2E4D955613A
File Size:
358.40 KB, 358400 bytes
|
|
MD5:
b416f16e2cfb1f077d997d7323148297
SHA1:
3aad275621fbefd4d32c31501f177fc7fb4c2050
SHA256:
33E2A319E01F942D891AC525B9B0FD3670CDA458235EB2CB5012E9FCFC495E87
File Size:
7.90 MB, 7896576 bytes
|
Show More
|
MD5:
64f7ff31a9bcbb17d5b545ecf47e5b43
SHA1:
0883523a64e7607c6e1d569c64f73b98ec573f60
SHA256:
D4E9E7D1176B0C13F19B21E1AF40D41E7049E8D000C568987709321C62A34291
File Size:
154.62 KB, 154624 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File has been packed
- File has exports table
- File has TLS information
- File is 32-bit executable
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | Geode Mod Loader |
| Company Name | Geode Development Team |
| File Description | Geode mod loader. |
| File Version | 4,9,0,0 |
| Internal Name | geode-loader |
| Legal Copyright | 2025 The Geode Team |
| Original Filename | geode-loader.dll |
| Product Name | Geode Loader |
| Product Version | 4,9,0,0 |
File Traits
- dll
- HighEntropy
- No Version Info
- packed
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 557 |
|---|---|
| Potentially Malicious Blocks: | 277 |
| Whitelisted Blocks: | 104 |
| Unknown Blocks: | 176 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Lumma.AO
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Encryption Used |
|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3aad275621fbefd4d32c31501f177fc7fb4c2050_0007896576.,LiQMAxHB
|