'_morf56@meta.ua_ File Extension' Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
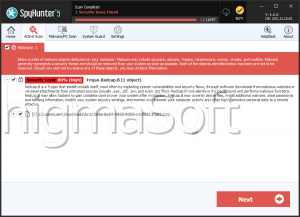
| Popularity Rank: | 6,495 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 6,034 |
| First Seen: | December 9, 2016 |
| Last Seen: | November 25, 2025 |
| OS(es) Affected: | Windows |
The '_morf56@meta.ua_ File Extension' Ransomware is an encryption Trojan that is named after the marker it uses to notify the users about the data encryption. The files affected by the '_morf56@meta.ua_ File Extension' Ransomware feature the '_morf56@meta.ua_' suffix appended after the default file extension. For example, 'Essexite rock.docx' will be encrypted to 'Essexite rock.docx_morf56@meta.ua_' and you may need to do another report on a silica-undersaturated mafic plutonic rock.
Macro-Enabled Documents Serve as Decoys While the '_morf56@Meta.ua_ File Extension' Ransomware is Installed in the Background
The '_morf56@meta.ua_ File Extension' Ransomware is a Trojan that is spread among Windows users via a spam campaign that carries macro-enabled documents. As you may know, the macro functionality in digital documents is abused by threat actors to deliver threats. Security researchers discovered the '_morf56@meta.ua_ File Extension' Ransomware in the second week of December 2016 and PC users may encounter the Trojan under the name FLKR Ransomware as well since one of the executable it uses is 'flkr.exe'. The '_morf56@meta.ua_ File Extension' Ransomware is designed to encode all files outside system folders such as:
- Windows
- Program Files
- Program Files (x86)
- System Volume Information
- Documents and Settings
- Users
- Install
- Music
- Intel
Data stored outside those directories are encrypted with Blowfish algorithm indiscriminately of the file type. We have seen the same practice incorporated with the 'ODCODC' Ransomware and the CryptoWire Ransomware. The ransom demand is dropped to the desktop as INSTRUCT.txt and opened with the default program for TXT files. The message is written in English and states:
'Information is encrypted with a strong password.
To decrypt it e-mail: morf56@meta.ua for instructions.
Reserve communication channel - this jabber: fhmjfjf@default.rs
Use jabber only when conversation via email is not possible'
The Channel on Jabber may Reveal the Persons behind the '_morf56@Meta.ua_ File Extension' Ransomwar
Instead of using the anonymous network of BitMessage like the Yakes Ransomware does, users can contact the operators of the '_morf56@meta.ua_ File Extension' Ransomware via the Jabber IM Network. The channel on Jabber could be used as a way to identify the operators of the '_morf56@meta.ua_ File Extension' Ransomware if AV vendors and the USSHC cooperate. The USSHC (United States Secure Hosting and Colocation) is a private company that hosts the Jabber Network. Users might be welcomed to write an email to morf56@meta.ua and ask for payment instructions. Researchers remind that threats like the 'Supermagnet@india.com' Ransomware and the 'Orgasm@india.com' Ransomware require from 370 USD to 780 USD to provide a decryptor. Windows users affected by the '_morf56@meta.ua_ File Extension' Ransomware could be invited to spend a considerable sum of money in the hope of being sent a decryption tool. We do not endorse cooperation with the team of cyber-extortionists since paying the ransom is a gamble, and you may not be given the proper decryption software. Instead, you could use backup images to recover from an attack with the '_morf56@meta.ua_ File Extension' Ransomware. Experts agree that you need to use a trusted anti-malware utility to eliminate the '_morf56@meta.ua_ File Extension' Ransomware Trojan safely. AV vendors reported that the '_morf56@meta.ua_ File Extension' Ransomware was seen to seen to use the following executables:
- launcher.exe
- delmelaun.bat
- delmeflk.bat
- flkr.exe
Analysis Report
General information
| Family Name: | Trojan.Coinminer.GE |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
dca246df6ad7e33ec053595595243eb4
SHA1:
873a69327a4ed16fc1ffc49f363f6ed1b4bfd354
SHA256:
64DFFA8E4DD1BBE42B230DECD09D9BE6906859A9BED3B68D8003716916095620
File Size:
1.55 MB, 1552384 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- No Version Info
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,382 |
|---|---|
| Potentially Malicious Blocks: | 541 |
| Whitelisted Blocks: | 1,784 |
| Unknown Blocks: | 57 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Coinminer.GE