Mitu Ransomware
Cybersecurity researchers have discovered a new ransomware threat called Mitu. Similar to many other malware threats of this nature, Mitu operates by encrypting files on the victim's computer once it successfully infects the system. To indicate the encryption process, Mitu modifies the original filenames by appending the '.mitu' extension. For instance, a file originally named '1.pdf' would be transformed into '1.pdf.mitu,' while '2.doc' would become '2.doc.mitu,' and so on. In addition to encrypting files, Mitu generates a ransom note on the compromised device in the form of a text file named '_readme.txt.'
It's important to note that the Mitu Ransomware belongs to the Djvu family of ransomware. Consequently, there is a possibility that other malware threats might have been deployed on the compromised devices. The operators of the STOP/Djvu variants have been known to infect systems with additional unsafe software, such as information stealers like RedLine, and Vidar. Therefore, the presence of the Mitu ransomware suggests the potential existence of associated malware threats on the affected devices.
The Mitu Ransomware Locks a Wide Range of File Types and Extorts Victims
The ransom-demanding message delivered to the victims of the Mitu Ransomware serves as a notification that their files have been encrypted. According to the message, the only known method for recovering the encrypted data is by purchasing the decryption key and tool from the cybercriminals responsible for the ransomware attack.
The ransom amount specified in the message is 980 USD. However, there is a provision mentioned that if the victim initiates contact with the attackers within 72 hours, the ransom amount will be reduced by 50%. The message also states that, before fulfilling the ransom demands, the victim has the option to test the decryption process by sending a single encrypted file to the criminals.
In most cases, attempting to decrypt the files without the involvement of the attackers is exceedingly difficult, if not impossible. Rare exceptions exist where flaws in the ransomware may allow for independent decryption.
Moreover, it is essential to note that even if the victim complies with the ransom demands, there is no guarantee that they will receive the promised decryption keys or software. Therefore, it is strongly advised against paying the ransom, as it not only fails to guarantee data recovery but also supports and encourages this illegal activity.
Taking steps to remove the Mitu Ransomware from the operating system is crucial to prevent further data encryption. However, it is important to understand that the removal process does not restore files that have already been compromised and encrypted by ransomware.
Make Sure that Your Devices and Data are Protected from Ransomware Attacks
To ensure the safety of devices and data from ransomware threats, users can implement the following security measures:
- Keep software up to date: Regularly update operating systems, anti-malware software, and all other applications on your devices. Software updates often brings security patches that address vulnerabilities that can be exploited by ransomware.
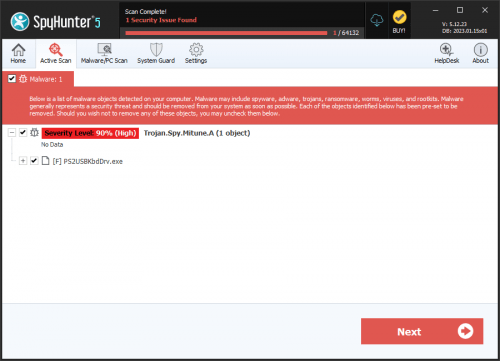
- Install reputable anti-malware software: Choose a reliable anti-malware solution and keep it updated. This software can detect and block known ransomware threats and suspicious activities.
- Exercise caution with email attachments and links: Be vigilant when opening email attachments or accessing links, especially if they come from unknown or suspicious sources. Ransomware can often be delivered through phishing emails or malicious downloads, so it's important to verify the sender and exercise caution.
- Backup important data regularly: Regularly back up your necessary files and data to an independent storage device or a cloud-based backup service. Ensure that the backups are disconnected from the network to prevent them from being affected by ransomware. Having up-to-date backups ensures that you can restore your files without paying the ransom in case of an attack.
- Enable firewall protection: Activate and maintain a firewall on your devices and network. Firewalls filter and monitor incoming and outgoing network traffic, providing an additional layer of protection against unauthorized access and potential ransomware infections.
- Use strong, unique passwords: Create strong passwords for all your accounts and devices, and avoid using the same password across multiple platforms. Think about using a password manager to store and manage your passwords securely.
- Educate yourself and your staff: Stay informed about the latest ransomware threats and educate yourself and your team about best practices for online security. Training programs and regular awareness sessions can help prevent unintentional actions that may lead to ransomware infections.
Do not forget that prevention is key when it comes to ransomware attacks. By implementing these security measures and practicing safe online habits, you can significantly reduce the risk of falling victim to ransomware and protect your devices and data.
The full text of the ransom note dropped by the Mitu Ransomware is:
'ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-nSxayRgUNO
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:'