Mischa Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 10,815 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 424 |
| First Seen: | May 12, 2016 |
| Last Seen: | September 5, 2023 |
| OS(es) Affected: | Windows |
The Mischa Ransomware is a ransomware Trojan that is used to force computer users to pay a ransom by taking their files hostage. The Mischa Ransomware, as late as May of 2016, is active in the wild. The Mischa Ransomware uses the AES encryption to encrypt its victims' files, demanding a payment through BitCoin. This is an approach commonly seen in most encryption ransomware Trojans. The Mischa Ransomware targets the most commonly used files, making sure that it encrypts any documents or media files that could be important to the victim. The Mischa Ransomware may be delivered using corrupted email attachments. The Mischa Ransomware also deletes Shadow Volume Copies and System Restore points, making it impossible for computer users to recover their files without a backup. Because of this, the best way to deal with the Mischa Ransomware is to restore the encrypted files from a backup location.
Table of Contents
Particularities About the Mischa Ransomware Attack
The Mischa Ransomware attack encrypts all files on the victim's computer. The Mischa Ransomware is delivered using typical threat delivery methods, the most common being corrupted email attachments or social media spam. When computer users click on a corrupted link, the Mischa Ransomware is installed on their computers. As soon as the Mischa Ransomware is installed, it starts encrypting the victim's files. Apart from encrypting the files, the Mischa Ransomware also drops text and HTML files containing instructions for payment. The Mischa Ransomware also changes the victim's Desktop image and displays a pop-up message. The Mischa Ransomware uses a fairly unique message composed of green lettering on a black background, reminiscent of older text-based computer terminals. The ransom note associated with the Mischa Ransomware says:
You became victim of the Mischa RANSOMWARE!
The files on your computer have been encrypted with an military grade encryption algorithm. There is no way to
restore your data without a special key. You can purchase this key on the darknet page shown in step 2.
To purchase your key and restore your data, please follow these three easy steps:
1. Download the Tor Browser at "https://www.torproject.org/". If you need
help, please google for "access onion page".
2. Visit one of the following pages with the Tor Browser:
http://the Mischapuk6hyrn72.onion/1MZKMy
http://the Mischa5xyix2mrhd.onion/1MZKMy
When the victims connect to these websites, they receive instructions for payment and also have the opportunity to converse with the perpetrators of the Mischa Ransomware using a chat console. The people responsible for the Mischa Ransomware will allow victims to decrypt one file to prove that they can decrypt the files.
Dealing with the Mischa Ransomware
Paying the Mischa Ransomware ransom is not a recommended action. Paying the Mischa Ransomware ransom only enables these con artists to continue carrying out these hoaxes. Furthermore, there is no guarantee that the con artists responsible for the Mischa Ransomware will honor their promise and deliver the decryption key. There is also a possibility that the Mischa Ransomware will encrypt the victim's files again if not removed completely.
The best way to deal with the Mischa Ransomware is to backup all files preemptively by using an exterior memory device or the cloud. If computer users everywhere make it a standard practice to backup all files, then attacks like the Mischa Ransomware will be completely ineffective, and will stop entirely. Essentially, the best way to deal with the Mischa Ransomware is to wipe the affected hard drive and restore files from the backup location. If you do not have backups of your files, then it is nearly impossible to recover the encrypted files. Before paying the ransom, PC security researchers recommend that computer users find out if there is a decryption utility available. Some encryption ransomware threats have been cracked by PC security researchers, and since many are similar, it may be worthwhile to test a decryption utility before paying the ransom amount.
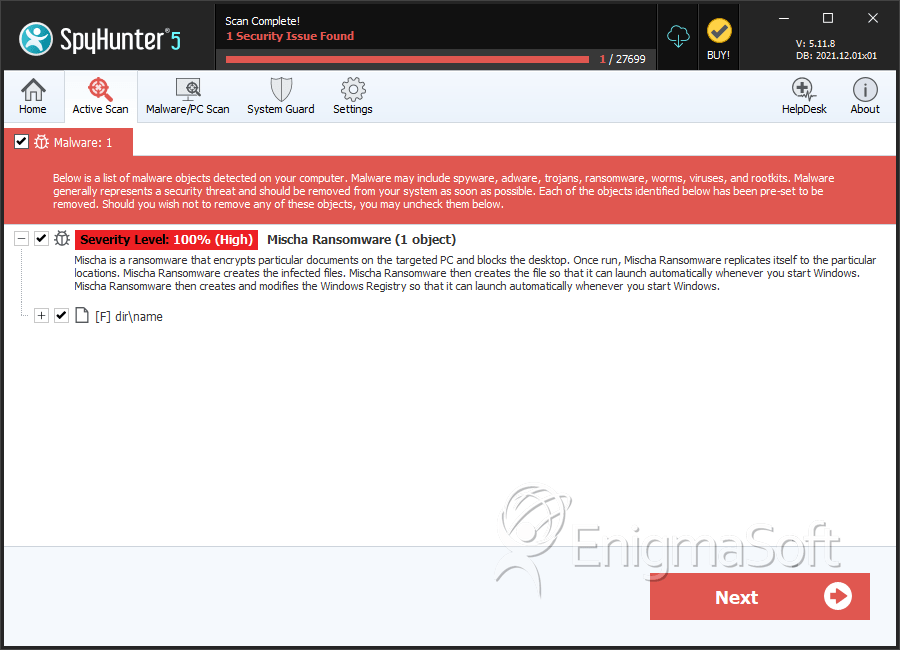
SpyHunter Detects & Remove Mischa Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Petya_and_Mischa.exe | 8a241cfcc23dc740e1fadc7f2df3965e | 4 |

