'Merry X-Mas!' Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 8,042 |
| First Seen: | January 3, 2017 |
| Last Seen: | October 7, 2022 |
| OS(es) Affected: | Windows |
The 'Merry X-Mas!' Ransomware receives its name because of the title of its ransom note. Victims of the 'Merry X-Mas!' Ransomware have reported that their files become encrypted during the attack and a ransom note is displayed wishing them a Merry Christmas. The 'Merry X-Mas!' Ransomware is being distributed through spam email messages. The spam email campaign associated with the 'Merry X-Mas!' Ransomware seems to impersonate a claim from the Federal Trade Commission, accusing the victim of violating the law and instructing the victim to click on an embedded link. Computer users will note that the domain used to send the email is ftc.gov.uk, which does not exist. After all, a domain located in the United Kingdom would not make sense for an agency of the United States government! Clicking on the link leads to a domain under the control of the developers of the 'Merry X-Mas!' Ransomware, despite it being masked as the legitimate Web page for the Federal Trade Commission.
The 'Merry X-Mas!' Ransomware Attack is Very Common
Clicking on the link in the spam email associated with the 'Merry X-Mas!' Ransomware downloads a ZIP archive onto the victim's computer. This file contains a file named 'complaint.pdf.exe,' which may show up as 'COMPLAINT.pdf' in most computers, which disable extensions. Computer users believing that this file is a legitimate PDF file may open it, allowing the 'Merry X-Mas!' Ransomware to be installed on their computers. The 'Merry X-Mas!' Ransomware will work in the background to encrypt the victim's files. The 'Merry X-Mas!' Ransomware connects to its Command and Control server using TOR and upload information about the victim's computer, as well as receive instructions for the attack.
During its infection, the 'Merry X-Mas!' Ransomware scans the infected computer's drives for certain file types and then uses a strong encryption algorithm to encrypt these files. The files encrypted by the 'Merry X-Mas!' Ransomware can be identified by their new extensions. The 'Merry X-Mas!' Ransomware will append the extensions '.PEGS1', '.MRCR1', or '.RARE1' to the end of each affected file's name. In each directory where files are encrypted, the 'Merry X-Mas!' Ransomware will drop a ransom note contained in an HTA file named 'YOUR_FILES_ARE_DEAD.hta.' This ransom file displays a pop-up window each time Windows starts up. The 'Merry X-Mas!' Ransomware ransom note instructs the victim to contact the 'Merry X-Mas!' Ransomware's creators through the email address comodosec@yandex.com or the @comodosecurity Telegram address. Unfortunately, the files encrypted by the 'Merry X-Mas!' Ransomware are not decryptable without the decryption key.
The 'Merry X-Mas!' Ransomware can encrypt a large number of file types. Below is the full list of file types that will become inaccessible after a 'Merry X-Mas!' Ransomware infection:
001, .1cd, .3d, .3d4, .3df8, .3dm, .3ds, .3fr, .3g2, .3ga, .3gp, .3gp2, .3mm, .3pr, .7z, .7zip, .8ba, .8bc, .8be, .8bf, .8bi8, .8bl, .8bs, .8bx, .8by, .8li, .a2c, .aa, .aa3, .aac, .aaf, .ab4, .abk, .abw, .ac2, .ac3, .accdb, .accde, .accdr, .accdt, .ace, .ach, .acr, .act, .adb, .ade, .adi, .adp, .adpb, .adr, .ads, .adt, .aep, .aepx, .aes, .aet, .afp, .agd1, .agdl, .ai, .aif, .aiff, .aim, .aip, .ais, .ait, .ak, .al, .allet, .alphacrypt, .amf, .amr, .amu, .amx, .amxx, .ans, .aoi, .ap, .ape, .api, .apj, .apk, .apnx, .app, .arc, .arch00, .ari, .arj, .aro, .arr, .arw, .as, .as3, .asa, .asc, .ascx, .ase, .asf, .ashx, .asm, .asmx, .asp, .aspx, .asr, .asset, .asx, .automaticdestinations-ms, .avi, .avs, .awg, .azf, .azs, .azw, .azw1, .azw3, .azw4, .b2a, .back, .backup, .backupdb, .bad, .bak, .bank, .bar, .bat, .bay, .bc6, .bc7, .bck, .bcp, .bdb, .bdp, .bdr, .bfa, .bgt, .bi8, .bib, .bic, .big, .bik, .bin, .bkf, .bkp, .bkup, .blend, .blob, .blp, .bmc, .bmf, .bml, .bmp, .boc, .bp2, .bp3, .bpk, .bpl, .bpw, .brd, .bsa, .bsk, .bsp, .btoa, .bvd, .bz2, .c, .cag, .cam, .camproj, .cap, .car, .cas, .cat, .cbf, .cbr, .cbz, .cc, .ccd, .ccf, .cch, .cd, .cdf, .cdi, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cef, .cer, .cert, .cfg, .cfm, .cfp, .cfr, .cgf, .cgi, .cgm, .cgp, .chk, .chml, .cib, .class, .clr, .cls, .clx, .cmd, .cmf, .cms, .cmt, .cnf, .cng, .cod, .col, .con, .conf, .config, .contact, .cp, .cpi, .cpio, .cpp, .cr2, .craw, .crd, .crt, .crw, .crwl, .crypt, .crypted, .cryptra, .cryptXXX, .cs, .csh, .csi, .csl, .cso, .csr, .css, .csv, .ctt, .cty, .cue, .cwf, .d3dbsp, .dac, .dal, .dap, .das, .dash, .dat, .database, .dayzprofile, .dazip, .db, .db_journal, .db0, .db3, .dba, .dbb, .dbf, .dbfv, .db-journal, .dbx, .dc2, .dc4, .dch, .dco, .dcp, .dcr, .dcs, .dcu, .ddc, .ddcx, .ddd, .ddoc, .ddrw, .dds, .default, .dem, .der, .des, .desc, .design, .desklink, .dev, .dex, .dfm, .dgc, .dic, .dif, .dii, .dim, .dime, .dip, .dir, .directory, .disc, .disk, .dit, .divx, .diz, .djv, .djvu, .dlc, .dmg, .dmp, .dng, .dob, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dox, .dpk, .dpl, .dpr, .drf, .drw, .dsk, .dsp, .dtd, .dvd, .dvi, .dvx, .dwg, .dxb, .dxe, .dxf, .dxg, .e4a, .edb, .efl, .efr, .efu, .efx, .eip, .elf, .emc, .emf, .eml, .enc, .enx, .epk, .eps, .epub, .eql, .erbsql, .erf, .err, .esf, .esm, .euc, .evo, .ex, .exf, .exif, .f90, .faq, .fcd, .fdb, .fdr, .fds, .ff, .ffd, .fff, .fh, .fhd, .fla, .flac, .flf, .flp, .flv, .flvv, .for, .forge, .fos, .fpenc, .fpk, .fpp, .fpx, .frm, .fsh, .fss, .fxg, .gadget, .gam, .gbk, .gbr, .gdb, .ged, .gfe, .gfx, .gho, .gif, .gif,.bmp, .gpg, .gpx, .gray, .grey, .grf, .groups, .gry, .gthr, .gxk, .gz, .gzig, .gzip, .h, .h3m, .h4r, .hbk, .hbx, .hdd, .hex, .hkdb, .hkx, .hplg, .hpp, .hqx, .htm, .html, .htpasswd, .hvpl, .hwp, .ibank, .ibd, .ibooks, .ibz, .ico, .icxs, .idl, .idml, .idx, .ie5, .ie6, .ie7, .ie8, .ie9, .iff, .iif, .iiq, .img, .incpas, .indb, .indd, .indl, .indt, .ink, .inx, .ipa, .iso, .isu, .isz, .itdb, .itl, .itm, .iwd, .iwi, .jac, .jar, .jav, .java, .jbc, .jc, .jfif, .jge, .jgz, .jif, .jiff, .jks, .jnt, .jpc, .jpe, .jpeg, .jpf, .jpg, .jpw, .js, .json, .jsp, .just, .k25, .kc2, .kdb, .kdbx, .kdc, .kde, .key, .kf, .klq, .kml, .kmz, .kpdx, .kwd, .kwm, .laccdb, .lastlogin, .lay, .lay6, .layout, .lbf, .lbi, .lcd, .lcf, .lcn, .ldb, .ldf, .lgp, .lib, .lit, .litemod, .lngttarch2, .localstorage, .locky, .log, .lp2, .lpa, .lrf, .ltm, .ltr, .ltx, .lua, .lvivt, .lvl, .m, .m2, .m2ts, .m3u, .m3u8, .m4a, .m4p, .m4u, .m4v, .mag, .man, .map, .mapimail, .max, .mbox, .mbx, .mcd, .mcgame, .mcmeta, .mcrp, .md, .md0, .md1, .md2, .md3, .md5, .mdb, .mdbackup, .mdc, .mddata, .mdf, .mdl, .mdn, .mds, .mef, .menu, .meo, .mfd, .mfw, .mic, .mid, .mim, .mime, .mip, .mjd, .mkv, .mlb, .mlx, .mm6, .mm7, .mm8, .mme, .mml, .mmw, .mny, .mobi, .mod, .moneywell, .mos, .mov, .movie, .moz, .mp1, .mp2, .mp3, .mp4, .mp4v, .mpa, .mpe, .mpeg, .mpg, .mpq, .mpqge, .mpv2, .mrw, .mrwref, .ms11, .ms11(Securitycopy), .mse, .msg, .msi, .msp, .mts, .mui, .mxp, .myd, .myi, .nav, .ncd, .ncf, .nd, .ndd, .ndf, .nds, .nef, .nfo, .nk2, .nop, .note, .now, .nrg, .nri, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .ntl, .number, .nvram, .nwb, .nx1, .nx2, .nxl, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odi, .odm, .odp, .ods, .odt, .oft, .oga, .ogg, .oil, .opd, .opf, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .owl, .oxt, .p12, .p7b, .p7c, .pab, .pack, .pages, .pak, .paq, .pas, .pat, .pbf, .pbk, .pbp, .pbs, .pcd, .pct, .pcv, .pdb, .pdc, .pdd, .pdf, .pef, .pem, .pfx, .php, .pif, .pkb, .pkey, .pkh, .pkpass, .pl, .plb, .plc, .pli, .plugin, .plus_muhd, .pm, .pmd, .png, .po, .pot, .potm, .potx, .ppam, .ppd, .ppf, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prc, .prel, .prf, .priv, .privat, .props, .prproj, .prt, .ps, .psa, .psafe3, .psd, .psk, .pspimage, .pst, .psw6, .ptx, .pub, .puz, .pwf, .pwi, .pwm, .pxp, .py, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .qcow, .qcow2, .qdf, .qed, .qel, .qic, .qif, .qpx, .qt, .qtq, .qtr, .r00, .r01, .r02, .r03, .r3d, .ra, .ra2, .raf, .ram, .rar, .rat, .raw, .rb, .rdb, .rdi, .re4, .res, .result, .rev, .rgn, .rgss3a, .rim, .rll, .rm, .rng, .rofl, .rpf, .rrt, .rsdf, .rsrc, .rss, .rsw, .rte, .rtf, .rts, .rtx, .rum, .run, .rv, .rvt, .rw2, .rwl, .rwz, .rzk, .rzx, .s3db, .sad, .saf, .safe, .sas7bdat, .sav, .save, .say, .sb, .sc2save, .sch, .scm, .scn, .scx, .sd0, .sd1, .sda, .sdb, .sdc, .sdf, .sdn, .sdo, .sds, .sdt, .search-ms, .sef, .sen, .ses, .sfs, .sfx, .sgz, .sh, .shar, .shr, .shw, .shy, .sid, .sidd, .sidn, .sie, .sis, .sitx, .sldm, .sldx, .slk, .slm, .sln, .slt, .sme, .snk, .snp, .snx, .so, .spd, .spr, .sql, .sqlite, .sqlite3, .sqlitedb, .sqllite, .sqx, .sr2, .srf, .srt, .srw, .ssa, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stm, .stt, .stw, .stx, .sud, .suf, .sum, .svg, .svi, .svr, .swd, .swf, .switch, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .syncdb, .t01, .t03, .t05, .t12, .t13, .tar, .tar.bz2, .tarbz2, .tax, .tax2013, .tax2014, .tbk, .tbz2, .tch, .tcx, .teslacrypt, .tex, .text, .tg, .tga, .tgz, .thm, .thmx, .tif, .tiff, .tlb, .tlg, .tlz, .tmp, .toast, .tor, .torrent, .tpu, .tpx, .trp, .ts, .tu, .tur, .txd, .txf, .txt, .uax, .udf, .uea, .umx, .unity3d, .unr, .unx, .uop, .uot, .upk, .upoi, .url, .usa, .usx, .ut2, .ut3, .utc, .utx, .uu, .uud, .uue, .uvx, .uxx, .val, .vault, .vb, .vbox, .vbs, .vc, .vcd, .vcf, .vcxpro, .vdf, .vdi, .vdo, .ver, .vfs0, .vhd, .vhdx, .vlc, .vlt, .vmdk, .vmf, .vmsd, .vmt, .vmx, .vmxf, .vob, .vp, .vpk, .vpp_pc, .vsi, .vtf, .w3g, .w3x, .wab, .wad, .wallet, .war, .wav, .wave, .waw, .wb2, .wbk, .wdgt, .wks, .wm, .wma, .wmd, .wmdb, .wmmp, .wmo, .wmv, .wmx, .wotreplay, .wow, .wpd, .wpe, .wpk, .wpl, .wps, .wsf, .wsh, .wtd, .wtf, .wvx, .x11, .x3f, .xcodeproj, .xf, .xhtml, .xis, .xl, .xla, .xlam, .xlc, .xlk, .xll, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlv, .xlw, .xlwx, .xml, .xpi, .xps, .xpt, .xqx, .xsl, .xtbl, .xvid, .xwd, .xxe, .xxx, .yab, .ycbcra, .yenc, .yml, .ync, .yps, .yuv, .z02, .z04, .zap, .zip, .zipx, .zoo, .zps, .ztmp.
Dealing with the 'Merry X-Mas!' Ransomware
PC security analysts advise computer users to prevent the 'Merry X-Mas!' Ransomware attacks by taking precautions when handling unsolicited email messages and using a reliable security application to intercept the 'Merry X-Mas!' Ransomware infection. The best protection against the 'Merry X-Mas!' Ransomware is to have backups of all files in place. This allows victims of the 'Merry X-Mas!' Ransomware attack to recover by restoring the affected files from a backup quickly.
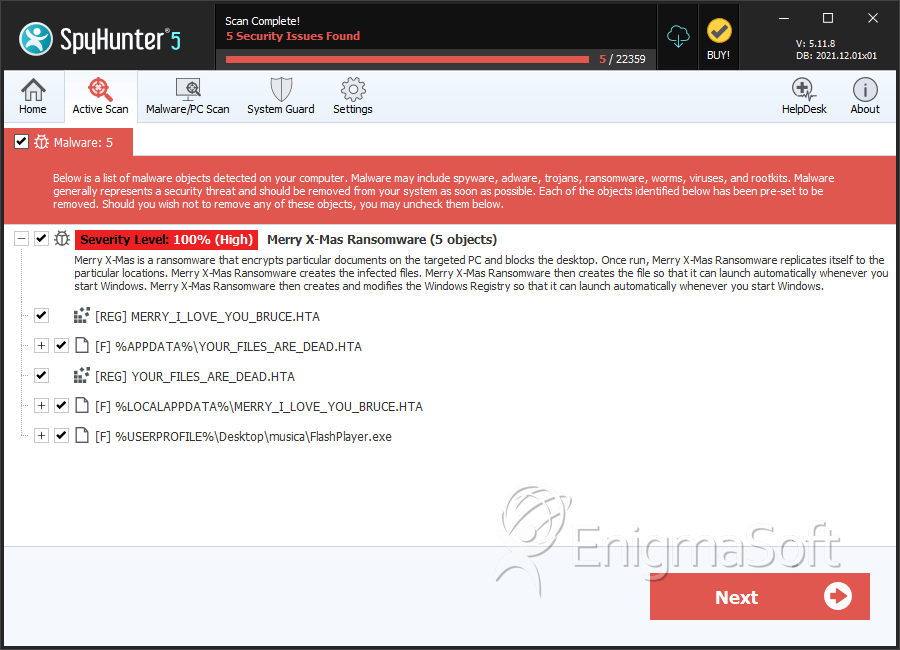
SpyHunter Detects & Remove 'Merry X-Mas!' Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | YOUR_FILES_ARE_DEAD.HTA | b3b7ca940b20082a3f349fcddc0cf991 | 254 |
| 2. | YOUR_FILES_ARE_DEAD.HTA | f64970998e5172392d55c54f466ebbd8 | 239 |
| 3. | YOUR_FILES_ARE_DEAD.HTA | d2ae721490c4525e8c371755e7f59eb4 | 121 |
| 4. | YOUR_FILES_ARE_DEAD.HTA | e4e2699ef7b9971d7e5a6a181fd69d90 | 99 |
| 5. | MERRY_I_LOVE_YOU_BRUCE.HTA | f2520cd0bf34b3b0350e8db21a759c7c | 70 |
| 6. | MERRY_I_LOVE_YOU_BRUCE.HTA | 68305a160d35d4347434637f470b3873 | 63 |
| 7. | MERRY_I_LOVE_YOU_BRUCE.HTA | 0e37416d8fefbfd16cbe1516df794920 | 55 |
| 8. | MERRY_I_LOVE_YOU_BRUCE.HTA | 3a1b5f64ff33d95d425291599be6b4e0 | 48 |
| 9. | YOUR_FILES_ARE_DEAD.HTA | 4d7297e309ee1cdb9793eaffc5c42646 | 46 |
| 10. | MERRY_I_LOVE_YOU_BRUCE.HTA | 713870beb7dc5456756a66d97b01a566 | 38 |
| 11. | MERRY_I_LOVE_YOU_BRUCE.HTA | e7aca562ae026f4727d68f27c87727b2 | 32 |
| 12. | MERRY_I_LOVE_YOU_BRUCE.HTA | 948d25c3299f577001768a25b04110fb | 31 |
| 13. | MERRY_I_LOVE_YOU_BRUCE.HTA | 5569b7db81d3f7a19eac96326143ea4c | 26 |
| 14. | MERRY_I_LOVE_YOU_BRUCE.HTA | f6e9eff2bb4e03cb057a73ff9ab77546 | 24 |
| 15. | MERRY_I_LOVE_YOU_BRUCE.HTA | eb85102d83f7aa16dffa88ba98d9bdfd | 20 |
| 16. | MERRY_I_LOVE_YOU_BRUCE.HTA | 1920ff41610e3415a9f29454af0336a7 | 17 |
| 17. | MERRY_I_LOVE_YOU_BRUCE.HTA | 66c157de8d98be180b6dd7b1e7329fa0 | 17 |
| 18. | MERRY_I_LOVE_YOU_BRUCE.HTA | 3ce28581ec43c41cb5e36e9312ef3299 | 15 |
| 19. | MERRY_I_LOVE_YOU_BRUCE.HTA | 7e45c5993dcc73ba5270437a9a576ac5 | 15 |
| 20. | MERRY_I_LOVE_YOU_BRUCE.HTA | 97be4525045485dd6bb6db72fa9708bb | 15 |
| 21. | MERRY_I_LOVE_YOU_BRUCE.HTA | 72ed1a179175c03c086c495da4a10406 | 13 |
| 22. | MERRY_I_LOVE_YOU_BRUCE.HTA | da5799e65d8f142adebb822b61bde0aa | 11 |
| 23. | MERRY_I_LOVE_YOU_BRUCE.HTA | 7b8ff3d7b107b53f8192fd228a8787bf | 11 |
| 24. | MERRY_I_LOVE_YOU_BRUCE.HTA | d0cccafeef4314dffcda5caf92a42ba3 | 9 |
| 25. | MERRY_I_LOVE_YOU_BRUCE.HTA | 4ecc47378f492933b3f31c9b626448dc | 9 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.