Mega Ad Blocker
Keeping devices free from intrusive and untrustworthy software is vital for maintaining privacy, security, and performance. Potentially Unwanted Programs (PUPs) often disguise themselves as legitimate tools, but they may perform questionable actions that compromise users' safety. One such example is Mega Ad Blocker, a browser extension marketed as an ad-blocking utility. Despite its claims, this app exhibits traits associated with adware and could introduce multiple privacy and security issues.
Table of Contents
Mega Ad Blocker – A Misleading Adware Extension
Although promoted as a solution for blocking intrusive ads, Mega Ad Blocker behaves quite the opposite. Instead of preventing unwanted advertising, it may inject or display additional ads across visited websites. These ads often include misleading or deceptive content, such as:
- Fake system alerts claiming the device is infected or outdated
- Fraudulent prize notifications and lottery pop-ups
- Misleading prompts encouraging the installation of other unwanted software
- Bogus error messages or updates designed to trick users
Interacting with such advertisements could expose users to phishing pages, malicious downloads, and fake technical support scams. As a result, sensitive data — including login credentials or financial information — may be stolen or misused.
Data Access and Browser Manipulation
Mega Ad Blocker's intrusive behavior extends beyond displaying ads. The extension may be capable of reading and altering data on all visited websites. This means that personal details, such as passwords, payment card data, and private messages, might be accessible to the app or shared with third parties.
Moreover, Mega Ad Blocker could modify webpage content, inject promotional material, and alter browser settings without explicit user consent. Such actions not only jeopardize privacy but also degrade the overall browsing experience by slowing down the system and generating intrusive pop-ups.
Deceptive Distribution Methods Used by PUPs
Programs like Mega Ad Blocker rarely rely on transparent installation methods. Instead, they frequently use questionable distribution tactics designed to trick users into installing them unintentionally. Common strategies include:
Bundled Installers: PUPs are often included in freeware or shareware installers. Users who rush through the setup process without selecting 'Advanced' or 'Manual' installation options may end up adding unwanted components unknowingly.
Deceptive Online Promotions: Fake update notifications, download buttons, and advertisements on suspicious websites may initiate the download of adware-laden installers.
Third-Party Platforms: Unofficial download pages, torrent sites, and file-sharing platforms are common sources of PUPs disguised as legitimate software or browser extensions.
Some untrustworthy sites may also use push notifications or pop-ups to promote apps like Mega Ad Blocker, further increasing the risk of accidental installation.
Protecting Against Adware and Similar Threats
To minimize exposure to adware and other intrusive software, users should follow safe browsing and installation practices:
- Download applications only from official and reputable sources.
- Always choose custom installation options to deselect bundled offers.
- Avoid interacting with pop-ups or ads claiming urgent security updates or rewards.
- Keep browsers, operating systems, and security tools up to date.
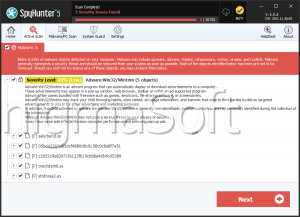
If Mega Ad Blocker is already installed, it should be removed immediately to prevent data exposure and restore normal browser functionality.
Conclusion
While Mega Ad Blocker presents itself as an ad-blocking tool, its behavior aligns more closely with adware. It may display misleading advertisements, collect sensitive data, and alter browser settings — all of which compromise user security. Exercising caution when installing software and maintaining a vigilant browsing routine is essential to protect against such potentially unwanted programs.