Maze Ransomware
Maze Ransomware Image
Most low-end authors of ransomware target regular users and extort them for their hard-earned cash. However, more highly-skilled cyber crooks would often opt to target businesses and organizations instead of private citizens. The authors of the Maze Ransomware appear to fit the profile of the latter. These cybercriminals would lock the target’s data and threaten to leak it online unless they are paid a significant ransom sum. Of course, the attackers claim that if the victim pays the ransom fee demanded, they will not only prevent their data from being leaked but also will receive a decryption key that will help them recover their files. Needless to say, leaking sensitive data such as classified documents online could cause great damage to any business.
The creators of the Maze Ransomware have certainly put a lot of time and effort into creating this data-locking Trojan. The Maze Ransomware is not only a rather complex threat in regards to its functionality, but it also is very stealthy. Cybersecurity analysts who have tried to study this piece of malware have found this to be quite a task because the Maze Ransomware:
- Makes sure to perform regular checks to determine if there are any software debuggers present on the compromised system and if the scan returns positive results, the threat will halt its operation.
- Aims at confusing malware researchers with a significant amount of what is known as ‘trash code’ and ‘fake functions’ whose goal is to obfuscate the code of the threat and make it more difficult to analyze.
- Checks the currently running processes and looks for any processes related to malware analysis and debugging tools. If a match is found, the Maze Ransomware will cease the attack and, instead, it will begin to execute pointless tasks that consume hardware resources - a simple trick to waste the time of malware researchers.
This Week in Malware Ep 6: Maze Ransomware #thisweekinmalware
According to cybersecurity analysts, the Maze Ransomware has likely been the creation of Russian cybercriminals. This is being speculated as the Maze Ransomware would perform a check on the infiltrated computers and halt its activity if it detects that the default keyboard is using the layout utilized in ex-Soviet states. Furthermore, the Maze Ransomware would not bother users and organizations whose default keyboard is Bosnian or Serbian.
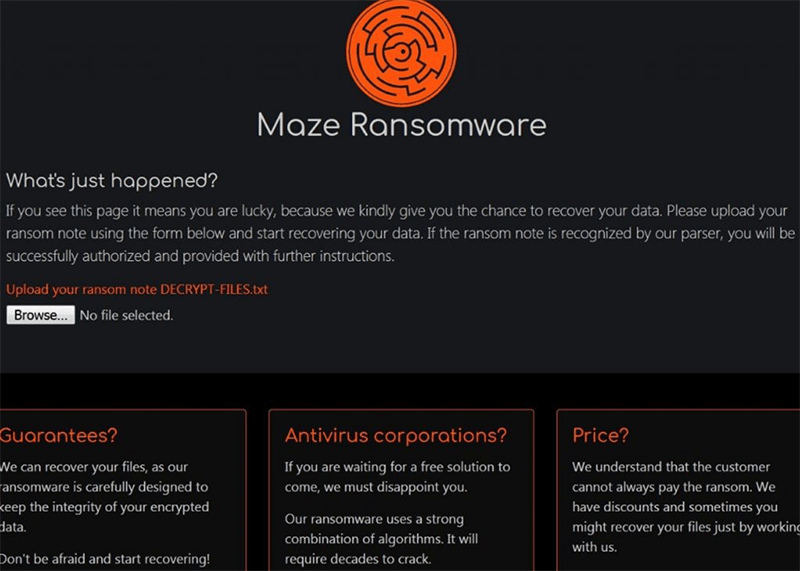
Once the Maze Ransomware infiltrates a target that fits its criteria, it will use an encryption method to lock all the data on the system. This file-locking Trojan appends a randomly generated extension to all the encrypted files’ names. The Maze Ransomware avoids tampering with certain filetypes – ‘.LNK,’ ‘.EXE,’ ‘.DLL’ and ‘.SYS.’ To avoid any system errors, this data-locking Trojan will skip the %APPDATA%, ‘Local Settings, and ‘Program Files’ folders. After locking all the targeted data, the Maze Ransomware would proceed with the attack by dropping a ransom note on the infected host. The name of the note is ‘DECRYPT-FILES.txt.’
Furthermore, the Maze Ransomware would alter the user’s wallpaper and set up a new one that contains the ransom message of the attackers. The payment page of the cyber crooks responsible for the Maze Ransomware is hosted on the Dark Web and thus is only accessible through the Tor Web browser. The attackers’ page is supposed to provide the victims with details regarding the processing of the payment. The creators of the Maze Ransomware offer to decrypt several files free of charge to prove that they are in possession of a functioning decryption key. There is no solid ransom fee announced by the authors of the Maze Ransomware. It would appear that the fee is calculated on an individual basis, likely depending on the amount and information type encrypted by the file-locking Trojan. Not paying the ransom fee will not only result in the victim’s data remaining locked but also their files being leaked online for everyone to see. As we mentioned, this can have devastating effects on a business.
What Makes Maze Stand Out?
Ransomware has become the poster child for cybersecurity attacks in recent years. There has been a significant increase in ransomware attacks in the past five years, with activity increasing in 2016. It feels like one can hardly turn on the news without finding a report of a company being crippled by ransomware.
With that said, ransomware has generally been a single-fronted attack for the most part. People have their data locked away on a target machine and have to pay a ransom to have it restored. While having data encrypted locally is a hassle, it isn’t much of a problem for the tech-savvy security-minded individual. Many ransomware victims are more than capable of getting their data back without any help by merely restoring it from a backup.
This is where Maze stands out from other ransomware. Maze employs a three-step attack of encryption, exfiltration, and extortion.
The critical difference between Maze and other kinds of ransomware is that Maze exfiltrates data. It pulls it from the target computer and copies it to an external server. The result is that victims can be attacked on more than one front. As well as encrypting data locally, Maze adds extra pressure through threats of publishing sensitive data online for the world to see.
Please make no mistake about it that this is a clear threat Maze is more than ready to deliver on. There have been several cases of Maze releasing sensitive information about their targets through websites. The data leaking began in December 2019 when Maze began posting documents and databases they had stolen from victims on websites.
How Does Maze Ransomware Work?
The term "work" is subjective for malware like this, as different malware perform different tasks. It is down to the code of malware to determine just how it works. Given that ransomware has to do little more than get into a system to work, the actual infection phase is where the bulk of the battle happens.
Unlike regular ransomware, which spreads through social engineering and spam emails, Maze uses drive-by downloads and exploit kits. Exploit kits are a compilation of software vulnerabilities that work together to exploit any computer that hasn’t been updated or patched yet.
This Week In Malware Episode 22 Part 2: SunCrypt Ransomware Joins Forces with Maze Ransomware Hacker Cartel
The use of an exploit kit is another standout feature of Maze compared to other ransomware. Exploit kits themselves are nothing new, but very few – if any – ransomware use them. Exploit kits are used for other kinds of viruses and aren’t considered suitable for ransomware attacks.
Maze uses the Fallout exploit kit in particular. One vulnerability Fallout exploits is the CVE-2018-15982 exploit in Flash player. Fallout is relatively new to the exploit kit scene and uses PowerShell to operate instead of the web browser. Fallout isn’t the only exploit kit Maze uses, though, as it has been seen to run Spelevo.
Dealing with ransomware threats is always tricky, but this does not mean that you should pay up if your system has been infiltrated. Paying cybercriminals only goes to motivate them to continue with their heinous online activities further and may not result in having your files back.

