MasterBuster Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 4 |
| First Seen: | November 2, 2016 |
| Last Seen: | January 18, 2020 |
| OS(es) Affected: | Windows |
The MasterBuster Ransomware is one of the many variants of HiddenTear that are being used to carry out attacks on computer users. HiddenTear was a ransomware project that was presented as an 'educational ransomware' infection. However, as should have been obvious, extortionists adapted the HiddenTear's code quickly and are creating a wide variety of ransomware Trojan variants to carry out attacks on the public easily. The MasterBuster Ransomware is one of these variants. The MasterBuster Ransomware is being distributed in a spam email campaign that uses corrupted Microsoft Office documents that exploit vulnerabilities in the macro feature in this application. If the MasterBuster Ransomware has been installed on your computer, PC security analysts advise against paying the ransom the con artists demand.
Table of Contents
The Master that Busters Your Finances
The MasterBuster Ransomware seems to be targeted towards individual computer users rather than to corporate targets. Because of this, the MasterBuster Ransomware does not have some of the most sophisticated features often seen in modern ransomware Trojans, such as the ability to infect shared network drives or server databases. However, there is no question that the MasterBuster Ransomware's attack is quite effective in taking the victim's data hostage and demanding the payment of a ransom.
The MasterBuster Ransomware tends to target media files and documents used by individuals, such as text and spreadsheet documents. The files that have been affected by the MasterBuster Ransomware will have the extension '.hcked' added to their name, making it easy to note which files have been affected by the MasterBuster Ransomware attack. The MasterBuster Ransomware will deliver its ransom note in the form of a text file dropped on the victim's Desktop. This file is named 'READ_THIS_FILE_IMPORTANT.txt'. The full contents of the MasterBuster Ransomware ransom note are printed below:
'IMPORTANT!!!!
Apnar Computer er shokol gurottopurno file encrypt kora hoyeche.
KONO FILE TOUCH KORBEN NA!
Amra shokol file recover kore dibo.
Jebhabe apnar file recover korben: -
1) Ei link e jan:
- [link to a form hosted on Google Drive]
2) Form fill-up korun.
3) 24 hours er moddhe apnar email + mobile SMS a shokol dhoroner instructions chole jabe.
Thank you!
DarkWing020'
'IMPORTANT!!!!
The files on your computer were encrypted securely
DO NOT DELETE THE FILES!
We can recover your files using a decoder.
To obtain a decoder you must do the following steps:
1) open the link:
[link to a form hosted on Google Drive]
2) Fill up the form.
3) Wait 24 hours to confirm payment via email + SMS and follow the instructions sent to you
Thank you!
DarkWing020'
The form that is used to carry out the MasterBuster Ransomware ransom payment was created by using the Google Forms and is hosted on the Google Drive. The form, like the ransom note, is written in Bengali and contains the following information:
'Files Recovery Process - DarkWing020
If you are asked to fill up this form, if all the files on your computer have been locked by our software. Do not be afraid !! By filling out this form you can get your files back easily without any problem !! You can use English / Bangla or in Banglish (English letters written in Bengali) to fill out the form. You should deposit the total amount of fine and will be notified by email and phone.
* The amount of the fine is 3,500 Rupee.
* If you take longer than 10 days to pay the fine there will be an additional fine of 5,000 to 10,000 Rupee.'
Taking a Look at the MasterBuster Ransomware’s Ransom
The ransom amount demanded by the MasterBuster Ransomware is not particularly large – about $52 USD. However, this is quite a large amount of money in terms of the average salary in India, where most the MasterBuster Ransomware attacks are carried out. Computer users are advised to prevent monetary and productivity losses associated with the MasterBuster Ransomware and other ransomware Trojans by taking important preventive measures such as backing up all data and using a reliable security application that is fully up-to-date.
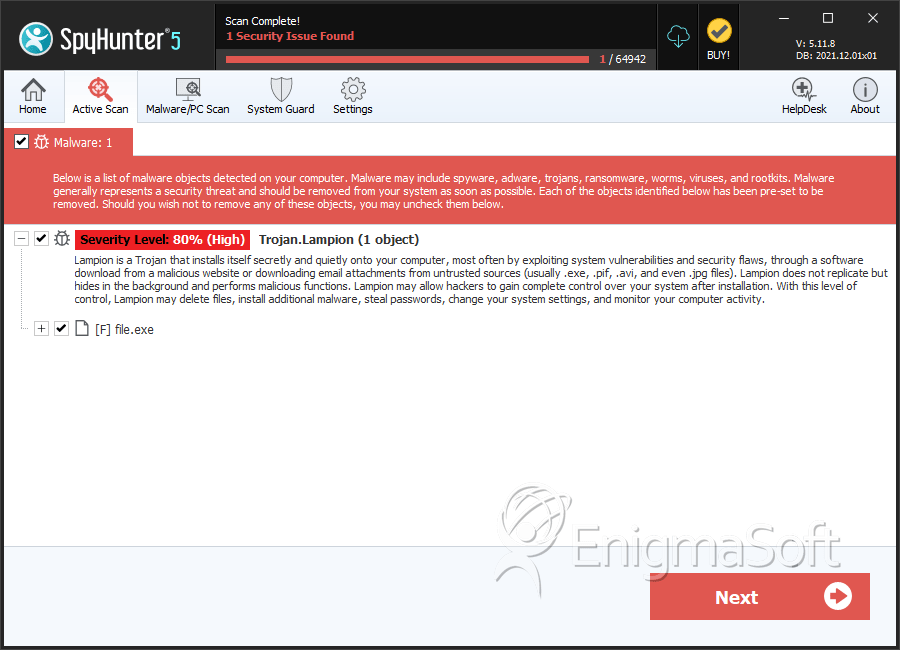
SpyHunter Detects & Remove MasterBuster Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 18977c78983d5e3f59531bd6654ad20f | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.