MalumPoS Malware
The MalumPoS Malware is a point-of-sale threat. The MalumPoS Malware is designed to collect credit card information on point-of-sale systems, that is, computers that are used to read credit cards or operated at the point of a retail sale. One of the characteristics of the MalumPoS Malware that makes it particularly threatening is that the MalumPoS Malware may be easily adapted to attack numerous different types of point-of-sale devices and computers.
Table of Contents
How the MalumPoS Malware Attacks a Computer
The MalumPoS Malware is particularly good at avoiding detection. In general, the MalumPoS Malware may impersonate an NVIDIA driver or service as a way to trick inexperienced computer users into installing the MalumPoS Malware on the affected Web browser. The MalumPoS Malware may be customized, making it extremely flexible and more threatening than other, similar point-of-sale threat. Although capable of attacking various devices, the MalumPoS Malware is especially designed to target computers using the Oracle MICROS, a platform that is quite common in hotels and retail computers, which may involve operations carried out with credit cards.
The MalumPoS Malware Attacks and Similar Point-of-Sale Infections
The MalumPoS Malware may collect data from various different credit cards and bypass certain security protections. Once the MalumPoS Malware is installed, the MalumPoS Malware carries out attacks that are similar to most other point-of-sale attacks. The MalumPoS Malware will search for credit card data running on the affected computer's memory. To prevent computer users from detecting the MalumPoS Malware, the MalumPoS Malware disguises itself as an NVIDIA Display Driver. The MalumPoS Malware is installed as a Windows service, running automatically when the infected computer starts up.
The MalumPoS Malware can inspect up to one hundred running memory processes, comparing it to a set of conditions established for credit card information. When the MalumPoS Malware detects this information on the affected computer, which may be scanned from a credit card's magnetic strip, the MalumPoS Malware stores it in an encrypted file. This file, named nvsvc.dll, is disguised to look like an NVIDIA driver. This file is encrypted and then sent to a remote server. This information may then be sold to a third-party to generate revenue or on underground forums on the Darknet, instead of being used directly by the creator of the MalumPoS Malware.
The MalumPoS Malware is designed to collect data from credit cards by Visa, MasterCard, American Express, Discover Cards, Diner’s Club and some Japanese credit cards. The MalumPoS Malware also targets Oracle Forms and Shift4 systems. Systems that are accessed using Internet Explorer are particularly vulnerable to the MalumPoS Malware attacks. The MalumPoS Malware may be modified to add new modules to gather data from other credit card companies or point-of-sale computers.
Some In-Depth Information Regarding the MalumPoS Malware
The MalumPoS Malware is very similar to Rdasrv, another point-of-sale infection. Shift4 point-of-sale systems and other systems that integrate point-to-point encryption hardware are not vulnerable to the MalumPoS Malware and other point-of-sale threats that scrape credit card data from the affected computer's RAM. Although the MalumPoS Malware and similar infections may attack older point-of-sale computers, point-of-sale system developers have taken significant steps to ensure that all of their devices and systems are adequately protected with the most recent patches and protections available from the MalumPoS Malware and similar point-of-sale attacks. After recent high-profile point-of-sale attacks on companies like Target, Home Depot and P. F. Chang's, it is crucial for retailers and companies dealing with credit cards to take adequate precautions to avoid these kinds of infections.
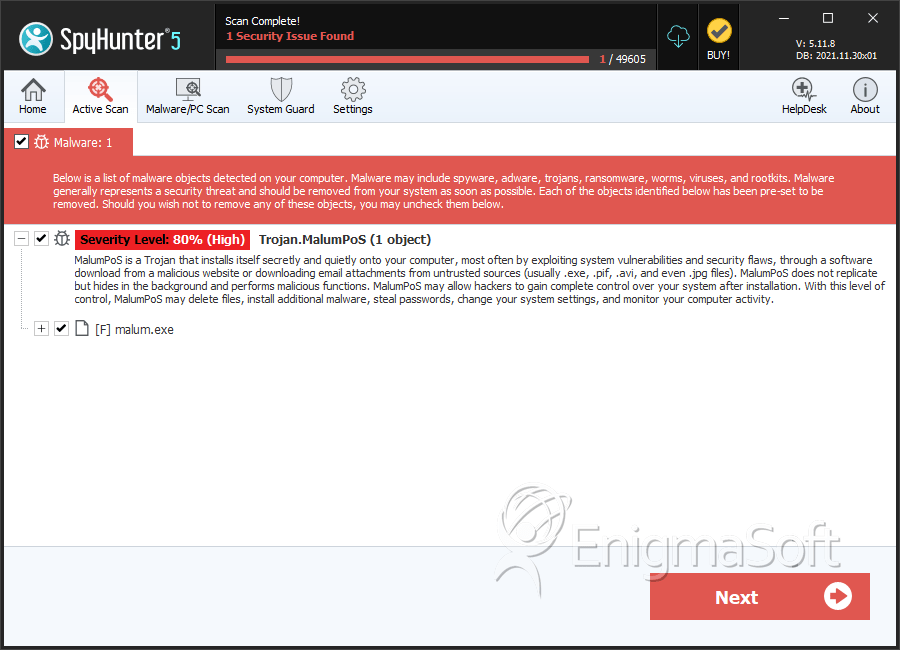
SpyHunter Detects & Remove MalumPoS Malware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | malum.exe | 06d2fa506fb454f869376ac50e8f7940 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.