LoJax
PC security researchers have been concerned about the concept of UEFI rootkits, which are considered as extremely threatening because they are very hard to detect and can survive thorough removal methods such as a replacement of the infected hard drive or reinstalling the affected operating system. PC security researchers have observed that UEFI rootkits have been presented in a proof of concept method and are being used by government operators. However, LoJax is the first UEFI rootkit campaign that is being used to carry out attacks in the wild, which confirms the existence and implementation of these threats.
Table of Contents
Some Details about the LoJax Creation
UEFI rootkits were just presented as attractive concepts to be shared in theory initially. However, PC security researchers have received information about attacks involving LoJax, which is being used in attacks by Sednit, a criminal group that has been responsible for various high-profile malware attacks. The LoJax rootkit is developed by this group, which goes under several other names such as APT28, STRONTIUM, Sofacy and Fancy Bear. The LoJax campaign was first presented at a conference on September 27, 2018, which called attention to the particularly harmful aspects of the LoJax threat.
What is the Objective of the Criminals Responsible for the LoJax Attacks
The criminal group responsible for the LoJax attacks has been active since 2004 and has received quite a lot of attention because they have been involved in a wide variety of high-profile attacks. This group is considered responsible for the political attacks on the Democratic party in the United States in 2016, as well as various hacks on several television networks and other high-profile targets. The people responsible for the LoJax attacks have several malware threats at their disposal, which they can use to carry out a wide variety of attacks.
How the LoJax Attack Works
At least once the LoJax attack has been successful in writing a threatening UEFI module on the targeted computer's memory. This allows LoJax to drop and execute its malware when the affected computer is booting. This method of attack is threatening because it allows LoJax to survive if the operating system is reinstalled or if the hard drive is replaced especially. However, cleaning the affected computer's UEFI firmware is an operation that is very uncommon and out of reach of the average computer users. The LoJax attacks seem to have been used to target government networks in Central Europe, Eastern Europe and the Balkans.
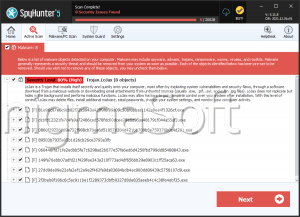
Detailing the LoJax Attacks
LoJax attacks are being carried out through a unified platform that enables criminals to target multiple vulnerabilities at once. The LoJax attack is extremely sophisticated, requiring numerous resources and, at this moment, is well beyond the capabilities of the average criminal group. Essentially, LoJax is designed to read the affected computer's UEFI settings and export them to a text file. Then, a copy of the affected system's firmware is built, adding a backdoor service to this firmware and overwriting the SPI flash memory on the target device, installing a corrupted UEFI on the infected computer. LoJax gains persistence that is unheard of in other threats through this attack. The typical methods that are considered thorough when dealing with other malware are not capable of removing LoJax or similar infections. The LoJax backdoor allows criminals to gain access to the targeted computer. Through this backdoor, the criminals can carry out any number of attacks, installing other malware onto the victim's computer, spying on its activities, or monetizing the infection in a variety of other ways. It will be interesting to see how malware researchers will react to attacks like LoJax and provide new protections for vulnerable PCs.