Lockout Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 4 |
| First Seen: | May 23, 2017 |
| Last Seen: | October 1, 2019 |
| OS(es) Affected: | Windows |
The Lockout Ransomware is a ransomware Trojan that is being used to carry out attacks on computer users. The Lockout Ransomware is being distributed through the use of bogus email attachments that use social engineering techniques to trick computer users into downloading and executing a corrupted code onto their computers. The Lockout Ransomware seems to be mainly targeted towards small and medium sized businesses and tends to use social engineering tactics that involve faking email messages from employees within a particular company.
Table of Contents
A Lockout Ransomware Infection Locks out Your Files
The Lockout Ransomware uses a combination of the AES and RSA encryptions to make its victims' files inaccessible. To do this, the Lockout Ransomware will encrypt the victim's files and refuse to release the decryption application until the victim pays a large ransom. The files that become encrypted by the Lockout Ransomware attack are marked with the file extension '.lockout,' making it simple to know which files have become affected by the Lockout Ransomware infection. The Lockout Ransomware will use the executable file 'c.exe' when carrying out an attack. The Lockout Ransomware is capable of encrypting numerous file types, including the following:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Lockout Ransomware will display a ransom note and change the Windows Welcome Screen adding a text to this picture containing the Lockout Ransomware ransom note. The Lockout Ransomware also will change the Desktop wallpaper image and drop its ransom note in a text file named 'Payment-instructions.txt,' which will be opened by the default text editor on the infected computer. The Lockout Ransomware will display the following ransom note on the infected computer to demand that the victim pays the ransom amount to recover the affected files:
'Your Payment ID: [9 RANDOM CHARACTERS]
Contact bnd54@mail2tor.com with your Payment ID from above to get price and payment details for unique decryption software. Files are encrypted with RSA-2048 encryption, so the only way to recover your data is using our software. we will decrypt 1 file for you to show you will get all data back using our unlocker. Price will double in 3 days so don't delay!'
Dealing with a Lockout Ransomware Infection
PC security researchers strongly advise computer users to refrain from contacting the people responsible for the Lockout Ransomware attack. These extortionists are likely to ignore the ransom payment or even re-infect the victim's computer. Since it is not possible to restore files encrypted by the encryption methods deployed by the Lockout Ransomware, PC security researchers strongly advise computer users to take preventive measures to limit the damage that can be caused by the Lockout Ransomware and other ransomware Trojans.
There are several preventive measures computer users can take to limit the damage in a Lockout Ransomware attack. The single best preventive measure computer users can e is a reliable backup method. Having backup copies of files on an external memory device or the cloud can make computer users completely invulnerable to schemes like the Lockout Ransomware. This is because the ability to restore the affected files removes any leverage or power the con artists gain over the victim during the attack, removing any need the computer users might have to pay the ransom amount. In addition to file backups, PC security analysts advise the use of a reliable, fully updated anti-malware application.
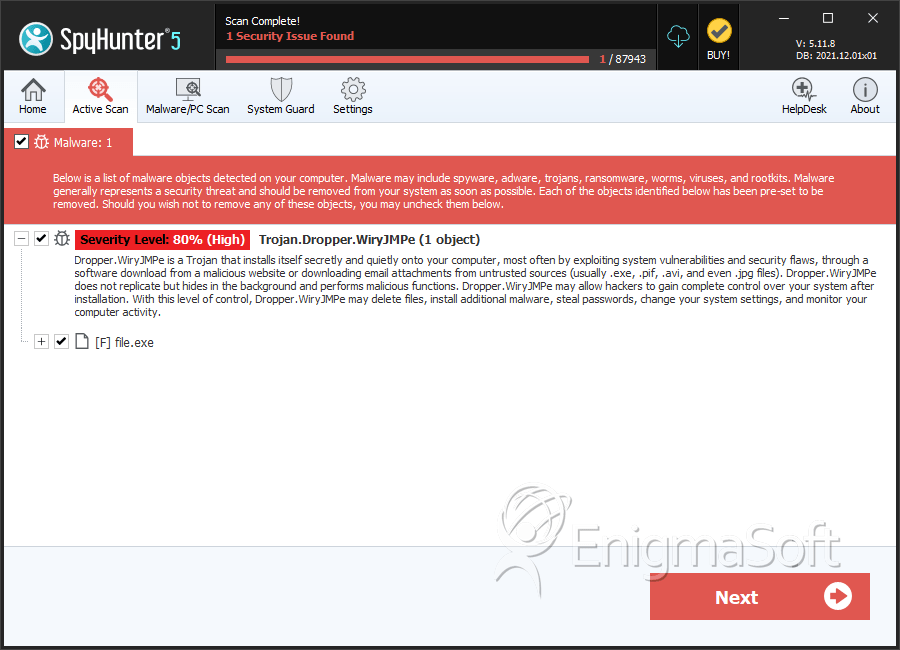
SpyHunter Detects & Remove Lockout Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | e3137275d9ef204209418b297d10e10c | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.